Electoral fraud
Electoral fraud, sometimes referred to as election fraud, election manipulation or vote rigging, is illegal interference with the process of an election, either by increasing the vote share of the favored candidate, depressing the vote share of the rival candidates, or both. What exactly constitutes electoral fraud varies from country to country.
| Political corruption | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Concepts | ||||||||||||
| Corruption by country | ||||||||||||
|
||||||||||||
Many kinds of election fraud[1] are outlawed in electoral legislations, but others are in violation of general laws, such as those banning assault, harassment or libel. Although technically the term "electoral fraud" covers only those acts which are illegal, the term is sometimes used to describe acts which are legal, but considered morally unacceptable, outside the spirit of an election or in violation of the principles of democracy.[2][3] Show elections, containing only one candidate, are sometimes classified as electoral fraud, although they may comply with the law and are presented more as referendums.
In national elections, successful electoral fraud can have the effect of a coup d'état, democracy protest[4] or corruption of democracy. In a narrow election, a small amount of fraud may be enough to change the result. Even if the outcome is not affected, the revelation of fraud can reduce voters' confidence in democracy. In April 2020, a 20-year voter fraud study by MIT University found the level of fraud "exceedingly rare" since it occurs only in "0.00006 percent" of instances nationally, and, in one state, "0.000004 percent — about five times less likely than getting hit by lightning in the United States."[5]
Electorate manipulation
| Part of the Politics series |
| Elections |
|---|
| Basic types |
| Terminology |
| Subseries |
| Lists |
| Related |
| Politics portal |
Electoral fraud can occur in advance of voting if the composition of the electorate is altered. The legality of this type of manipulation varies across jurisdictions. Deliberate manipulation of election outcomes is widely considered a violation of the principles of democracy.[6]
Artificial migration or party membership
In many cases, it is possible for authorities to artificially control the composition of an electorate in order to produce a foregone result. One way of doing this is to move a large number of voters into the electorate prior to an election, for example by temporarily assigning them land or lodging them in flophouses.[7][8] Many countries prevent this with rules stipulating that a voter must have lived in an electoral district for a minimum period (for example, six months) in order to be eligible to vote there. However, such laws can also be used for demographic manipulation as they tend to disenfranchise those with no fixed address, such as the homeless, travelers, Roma, students (studying full-time away from home), and some casual workers.
Another strategy is to permanently move people into an electoral district, usually through public housing. If people eligible for public housing are likely to vote for a particular party, then they can either be concentrated into one area, thus making their votes count for less, or moved into marginal seats, where they may tip the balance towards their preferred party. One notable example of this occurred in the City of Westminster in England under Shirley Porter.[9]
Immigration law may also be used to manipulate electoral demography. For instance, Malaysia gave citizenship to immigrants from the neighboring Philippines and Indonesia, together with suffrage, in order for a political party to "dominate" the state of Sabah; this controversial process was known as Project IC.[10]
A method of manipulating primary contests and other elections of party leaders are related to this. People who support one party may temporarily join another party (or vote in a crossover way, when permitted) in order to elect a weak candidate for that party's leadership. The goal ultimately is to defeat the weak candidate in the general election by the leader of the party that the voter truly supports. There were claims that this method was being utilised in the UK Labour Party leadership election in 2015, where Conservative-leaning Toby Young encouraged Conservatives to join Labour and vote for Jeremy Corbyn in order to "consign Labour to electoral oblivion".[11][12] Shortly after, #ToriesForCorbyn trended on Twitter.[13]
Disenfranchisement
The composition of an electorate may also be altered by disenfranchising some classes of people, rendering them unable to vote. In some cases, states have passed provisions that raised general barriers to voter registration, such as poll taxes, literacy and comprehension tests, and record-keeping requirements, which in practice were applied against minority populations to discriminatory effect. From the turn of the century into the late 1960s, most African Americans in the southern states of the former Confederacy were disenfranchised by such measures. Corrupt election officials may misuse voting regulations such as a literacy test or requirement for proof of identity or address in such a way as to make it difficult or impossible for their targets to cast a vote. If such practices discriminate against a religious or ethnic group, they may so distort the political process that the political order becomes grossly unrepresentative, as in the post-Reconstruction or Jim Crow era until the Voting Rights Act of 1965. Felons have been disenfranchised in many states as a strategy to prevent African Americans from voting.[14]
Groups may also be disenfranchised by rules which make it impractical or impossible for them to cast a vote. For example, requiring people to vote within their electorate may disenfranchise serving military personnel, prison inmates, students, hospital patients or anyone else who cannot return to their homes. Polling can be set for inconvenient days, such as midweek or on holy days of religious groups: for example on the Sabbath or other holy days of a religious group whose teachings determine that voting is prohibited on such a day. Communities may also be effectively disenfranchised if polling places are situated in areas perceived by voters as unsafe, or are not provided within reasonable proximity (rural communities are especially vulnerable to this).
In some cases, voters may be invalidly disenfranchised, which is true electoral fraud. For example, a legitimate voter may be "accidentally" removed from the electoral roll, making it difficult or impossible for the person to vote.
In the Canadian federal election of 1917, during the Great War, the Union government passed the Military Voters Act and the Wartime Elections Act. The Military Voters Act permitted any active military personnel to vote by party only and allowed that party to decide in which electoral district to place that vote. It also enfranchised those women who were directly related or married to an active soldier. These groups were believed to be disproportionately in favor of the Union government, as that party was campaigning in favor of conscription. The Wartime Elections Act, conversely, disenfranchised particular ethnic groups assumed to be disproportionately in favour of the opposition Liberal Party.
Division of opposition support
Stanford University professor Beatriz Magaloni described a model governing the behaviour of autocratic regimes. She proposed that ruling parties can maintain political control under a democratic system without actively manipulating votes or coercing the electorate. Under the right conditions, the democratic system is maneuvered into an equilibrium in which divided opposition parties act as unwitting accomplices to single-party rule. This permits the ruling regime to abstain from illegal electoral fraud.[15]
Preferential voting systems such as score voting, instant-runoff voting, and single transferable vote are designed to prevent systemic electoral manipulation and political duopoly.[16][17]
Intimidation
Voter intimidation involves putting undue pressure on a voter or group of voters so that they will vote a particular way, or not at all. Absentee and other remote voting can be more open to some forms of intimidation as the voter does not have the protection and privacy of the polling location. Intimidation can take a range of forms including verbal, physical, or coercion. This was so common that in 1887, a Kansas Supreme Court in New Perspectives on Election Fraud in The Gilded Age said "[...] physical retaliation constituted only a slight disturbance and would not vitiate an election."
- Violence or the threat of violence: In its simplest form, voters from a particular demographic or known to support a particular party or candidate are directly threatened by supporters of another party or candidate or by those hired by them. In other cases, supporters of a particular party make it known that if a particular village or neighborhood is found to have voted the 'wrong' way, reprisals will be made against that community. Another method is to make a general threat of violence, for example, a bomb threat which has the effect of closing a particular polling place, thus making it difficult for people in that area to vote.[18] One notable example of outright violence was the 1984 Rajneeshee bioterror attack, where followers of Bhagwan Shree Rajneesh deliberately contaminated salad bars in The Dalles, Oregon, in an attempt to weaken political opposition during county elections.
- Attacks on polling places: Polling places in an area known to support a particular party or candidate may be targeted for vandalism, destruction or threats, thus making it difficult or impossible for people in that area to vote.
- Legal threats: In this case, voters will be made to believe, accurately or otherwise, that they are not legally entitled to vote, or that they are legally obliged to vote a particular way. Voters who are not confident about their entitlement to vote may also be intimidated by real or implied authority figures who suggest that those who vote when they are not entitled to will be imprisoned, deported or otherwise punished.[19][20] For example, in 2004, in Wisconsin and elsewhere voters allegedly received flyers that said, "If you already voted in any election this year, you can't vote in the Presidential Election", implying that those who had voted in earlier primary elections were ineligible to vote. Also, "If anybody in your family has ever been found guilty of anything you can't vote in the Presidential Election." Finally, "If you violate any of these laws, you can get 10 years in prison and your children will be taken away from you."[21][22] Another method, allegedly used in Cook County, Illinois in 2004, is to falsely tell particular people that they are not eligible to vote.[20]
- Coercion: The demographic that controlled the voting ballot would try to persuade others to follow them. By singling out those who were against the majority, people would attempt to switch the voters' decision. Their argument could be that since the majority sides with a certain candidate, they should admit defeat and join the winning side. If this didn't work, this led to the threatening of violence seen countless times during elections. Coercion, electoral intimidation was seen in the Navy. In 1885 William C. Whitney started an investigation that involved the men in the Navy. As said by Whitney "the vote of the yard was practically coerced and controlled by the foremen. This instance shows how even in the Navy there were still instances of people going to great lengths for the desired elective to win.
Disinformation
People may distribute false or misleading information in order to affect the outcome of an election.[2] For example, in the Chilean presidential election of 1970, the U.S. government's Central Intelligence Agency used "black propaganda"—materials purporting to be from various political parties—to sow discord between members of a coalition between socialists and communists.[23]
Another use of disinformation is to give voters incorrect information about the time or place of polling, thus causing them to miss their chance to vote. As part of the 2011 Canadian federal election voter suppression scandal, Elections Canada traced fraudulent phone calls, telling voters that their polling stations had been moved, to a telecommunications company that worked with the Conservative Party.[24]
Vote buying
Vote buying occurs when a political party or candidate seeks to buy the vote of a voter in an upcoming election. Vote buying can take various forms such as a monetary exchange, as well as an exchange for necessary goods or services.[25] This practice is often used to incentivise or persuade voters to turn out to elections and vote in a particular way. Despite the fact that this practice is illegal in many countries such as the United States, Argentina, Mexico, Kenya, Brazil and Nigeria, its prevalence remains worldwide.
In some parts of the United States in the mid- and late 19th century, members of competing parties would vie, sometimes openly and other times with much greater secrecy, to buy and sell votes. Voters would be compensated with cash or the covering of one's house/tax payment. To keep the practice of vote buying secret, parties would open fully staffed vote-buying shops.[26] Parties would also hire runners, who would go out into the public and find floating voters and bargain with them to vote for their side.[26]
In England, documentation and stories of vote buying and vote selling are also well known. The most famous episodes of vote buying came in 18th century England when two or more rich aristocrats spent whatever money it took to win. The notorious "Spendthrift election" came in Northamptonshire in 1768, when three earls spent over £100,000 each to win a seat.[27]
Voters may be given money or other rewards for voting in a particular way, or not voting. In some jurisdictions, the offer or giving of other rewards is referred to as "electoral treating".[28] Electoral treating remains legal in some jurisdictions, such as in the Seneca Nation of Indians.[29]
Vote buying can take the form of "turnout buying", where a broker brings many people to the polls, with a background sure to vote one way, and the results are seen in the precinct results.[30]
Whom to target
One of the main concerns with vote buying lies in the question of which population or group of voters are most likely to be susceptible to accepting compensation in exchange for their vote. Scholars such as Stokes argue that it is the weakly opposed voters are the best ones to target for vote buying.[31] This means that in a situation in which there are two parties running for office, for example, the voters who are not inclined to vote one way or the other are the best to target. Other scholars argue that it is people of lower income status who are the best group to target, as they are the most likely to be receptive to monetary or other forms of compensation.[31] This has proven to be the case in both Argentina and Nigeria. Since the wealthy are presumably not in need of money, goods or services, it would require a much larger compensation in order to sway their vote. However, as seen in the case of Argentina for example, citizens who reside within poor communities are in great need of income, or medical services, for example, to feed their families and keep them in good health. With that being said, a much smaller sum of cash or a medical prescription would be of much greater value and thus their political support can be much easier to purchase.
How to monitor
When postal ballots are mailed to voter,s the buyer can fill them out or see how they are filled out. Monitoring is harder when ballots are cast secretly at a polling place.[31] In some cases, there have been instances of voter tickets, or monitoring by individuals.[32] Voters seeking to be compensated for their votes would use specially-provided voter ballots, or would fold their ballot in a particular way in order to indicate that they voted for the candidate they were paid to vote for.
If a buyer is able to obtain a blank ballot (by theft, counterfeit, or a legitimate absentee ballot) the buyer can then mark the ballot for their chosen candidates and pay a voter to take the pre-marked ballot to a polling station, exchange it for the blank ballot issued and return the blank ballot to the attacker. This is known as chain voting.[33] It can be controlled in polling places by issuing each ballot with a unique number, which is checked and torn off as the ballot is placed in the ballot box.
Another strategy has been to invoke personalized social norms to make voters honor their contracts at the voting booth.[25] Such social norms could include personal obligation such as moral debts, social obligations to the buyers, or a threat of withholding or ceasing to produce necessary resources. This is made more effective when the rewards are delivered personally by the candidate or someone close to them, in order to create a sense of gratitude on behalf of the voters towards the candidate.[25]
Consequences
There are several negative consequences that arise from the practice of vote buying. The presence of vote buying in democratic states poses a threat to democracy itself, as it interferes with the ability to rely on a popular vote as a measure of people's support for potential governments' policies.[34]
Another noted consequence is that the autonomy of voters is undermined. Since getting paid or receiving rewards for their votes generates a form of income that they may need to support themselves or their families, they have no autonomy to cast the vote that they truly want.[31] This is extremely problematic because if it is the most corrupt politicians who are engaging in vote buying, then it is their interests that remain the ones that dictate how the country is going to be run. This, in turn, perpetuates corruption in the system even further creating an unbreakable cycle.
Thirdly, vote buying can create a dependency of voters on the income or goods that they are receiving for their votes, and can further perpetuate a type of poverty trap.[35] If they are receiving medicine from their communities' broker for example, if this tie is cut off then they may no longer have access to this necessity. It can be true that the broker in that community has no interest or incentive to actually increase the standards of living of the community members, as it is very possible that they are only interested in getting whatever share of the profit they are entitled to for working for the party.[36] Additionally, if the goods or money are coming directly from a candidate, this candidate's only wish is to maintain their power. That being said, they may provide services but their real interest may lie in keeping the voters dependent on the rewards they are providing in order to stay in power.
Latin America
The 2010 and 2012 surveys for the Americas Barometer showed that 15% of surveyed voters in Latin America had been offered something of value in exchange for voting a particular way.[37]
Argentina
Vote buying and the overall practice of clientelism is widespread in Argentina. According to Simeon Nichter, one of the main perpetrators of these illegal activities were the Peronist party.[32] The relationship between voters and Peronist candidates allegedly are such that voters are offered particular goods, services, favours or monetary compensation in exchange for their political support for the party. These rewards could include a job, medicine, a roof, clothing, foods, and other goods or services. The case of Argentina in particular in that it relies heavily on face-to-face and day-to-day interactions between "brokers" who act as middlemen and voters.[38] Since many of the communities in Argentina are ridden with poverty and are in need of these particular resources, it is these communities that have statistically shown to be in a certain demographic that were targeted for voted buying. Additionally, vote buying in this region focuses on citizens who are not strongly in favour or opposed to the political machine, and whose political loyalty does not necessarily lie with one party or another.[31] In this way, vote buying acts as a mechanism to sway the decisions of weakly opposed voters. In a study done by Susan C. Stokes, she finds that the brokers in these communities are known to all the citizens and have access to the necessary resources from the municipality. They maintain relationships with the voters and grant them rewards and favours continuously in order to keep the party they work for in the office. This is one main explanation for why many lower-income voters are seen voting for populist leaders, as well as authoritarian ones.[31] Many citizens view these brokers as positive pillars in their lives and have the utmost respect for the help they distribute. However, others view them as hands of corruption. Stokes further explains that the capacity of these brokers is constrained due to the fact that they can only maintain this type of transactional relationship with a limited number of voters.[31] Furthermore, the brokers have the additional responsibility of maintaining trusting and solid relationships with their resource suppliers. Without these strong ties, they would have no means through which to carry out vote-buying practices.[38]
Mexico
Similarly to Argentina, it has been found that vote-buying in Mexico is most likely in rural and poor regions of the country.[39] There are many instances of vote buying that have occurred in the history of Mexican elections, however, there are two main instances of fund in the literature that occurred in the last two decades. The first was the 2006 Mexican election, where it was found that 8.8% of the population that was not a beneficiary of a specific social program was offered compensation for their vote.[40] Similarly, a corruption inquiry arrested Andrés Granier Melo for embezzlement of funds in the state of Tabasco during his governorship: among other things, some of these funds were used for vote-buying (although Melo has denied all accusations).[41]
Venezuela
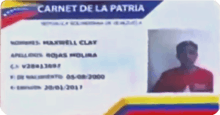
During the 2018 Venezuelan presidential election, reports of vote buying were prevalent during the presidential campaigning. Venezuelans suffering from hunger were pressured to vote for Maduro, with the government bribing potential supporters with food.[43] Maduro promised rewards for citizens who scanned their Carnet de la Patria at the voting booth, which would allow the government to monitor the political party of their citizens and whether or not they had voted. These prizes were reportedly never delivered.[42]
Everyone who has a Carnet de la Patria has to go to vote on 20 May. ... I am thinking of giving a prize to the people of Venezuela who go out to vote that day with the Carnet de la Patria
In a visit to Delta Amacuro, president and reelection candidate Nicolás Maduro gave away eight motor boats, nine ambulances, and reopened the "Antonio Díaz" Tucupita Airport, among other announcements, violating Article 223 of the Organic Law of Electoral Processes which forbids the use of state resources during election campaigns, as well as one of the prerogatives in the Agreement of Electoral Guarantees signed by the presidential candidates to the CNE.[45][46][47] On 8 May Maduro again violated the electoral law during an electoral act in the Amazonas state by promising to give fuel to the entity in exchange for votes.[48][49][50][51]
Africa
The fifth Afrobarometer survey showed that 48% of voters in 33 African countries feared violence during elections, and 16% of voters were offered money or other goods in exchange for voting a particular way in the most recent election.[37]
Nigeria
On a self-reported survey that was conducted, 1 in 5 Nigerian has experienced an offer for their vote. The rewards offered by Nigerian politicians include money, commodities such as food and clothing, or a job.[52] Although the practice of vote buying is widespread, 58% of Nigerians surveyed at the time of the 2007 election viewed vote buying as immoral.[52] Despite this, when asked if they thought it was wrong to accept rewards or monetary compensation for your vote, 78% said no.[52] One factor that needs to be iterated when it comes to studies that are based on surveys is that since vote buying is illegal in most countries, a researcher's ability to collect accurate data is hindered. This is because many citizens may not feel comfortable revealing their experience or involvement with corrupt activities, or fear that they will suffer repercussions from their governments for coming forward with such information.[52]
Kenya
Since the 1990s, Kenya has had regular multiparty elections in which vote buying has played a central role. In his article, scholar Eric Kramon states that: "According to the data gathered by the Coalition for Accountable Political Finance in Kenya, cash handouts to voters represents around 40% of the average parliamentary candidates' campaign budget, making up the largest budget item."[53] These handouts are made in various ways including stops on the campaign trail, and at-large campaign rallies[54][55]. "In the 2002 election, 40% of surveyed adult Kenyans reported having accepted a bribe in exchange for their vote, and 22% for the 2007 elections."[53]
It is noted by Kramen that access to information is a huge factor in determining the success of vote buying in Kenya. If the voters have little access to political information or lack political knowledge then they are more likely to be swayed by clientelistic reasoning.[53] Moreover, if the voter does have access to information about an incumbent, then the price to sway their vote is more likely to go up. Additionally, Kramon notes that citizens of Kenya tend to value candidates who provide rewards because their ability to do so points to how great their abilities will be once they are in office.[53]
Asia
Philippines
Despite the Commission on Elections's (COMELEC) tight campaign against vote buying in the Philippines, it was rampant across the country especially near the election period.[56] According to the Philippine National Police, the business of vote buying was done in the dark where the number of people gathered there to received a sample ballot with the money, mostly at least ₱500 attached to it.[56] However, the authorities have since apprehended those who involved.[57]
Voting process and results
A list of threats to voting systems, or electoral fraud methods considered as sabotage are kept by the National Institute of Standards and Technology.[58]
Misleading or confusing ballot papers
Ballot papers may be used to discourage votes for a particular party or candidate, using the design or other features which confuse voters into voting for a different candidate. For example, in the 2000 U.S. presidential election, Florida's butterfly ballot paper was criticized as poorly designed, leading some voters to vote for the wrong candidate. While ballot was designed by a Democrat, it was the Democrat, Al Gore, who was most harmed by voter errors because of this design.[59] Poor or misleading design is usually not illegal and therefore not technically election fraud, but it can nevertheless subvert the principles of democracy.
Sweden has a system with separate ballots used for each party, to reduce confusion among candidates. However, ballots from small parties such as Piratpartiet, Junilistan and Feministiskt initiativ have been omitted or placed on a separate table in the election to the EU parliament in 2009.[60] Ballots from Sweden Democrats have been mixed with ballots from the larger Swedish Social Democratic Party, which used a very similar font for the party name written on the top of the ballot.
Another method of confusing people into voting for a different candidate than intended is to run candidates or create political parties with similar names or symbols as an existing candidate or party. The goal is to mislead voters into voting for the false candidate or party to influence the results.[61] Such tactics may be particularly effective when a large proportion of voters have limited literacy in the language used on the ballot. Again, such tactics are usually not illegal but often work against the principles of democracy.
Another type of possible electoral confusion is multiple variations of voting by different electoral systems. This may cause ballots to be counted as invalid if the wrong system is used. For instance, if a voter puts a first-past-the-post cross in a numbered single transferable vote ballot paper, it is invalidated. For example, in Scotland and other parts of the United Kingdom, up to four different voting systems and types of ballots may be used, based on the jurisdictional level of elections for candidates. Local elections are determined by single transferable votes; Scottish parliamentary elections by the additional member system; national elections for the UK Parliament by first-past-the-post; and elections to the European Parliament by a party list system.
Ballot stuffing

Ballot stuffing, or "ballot-box stuffing", is the illegal practice of one person submitting multiple ballots during a vote in which only one ballot per person is permitted.
Ballot stuffing is still possible with electronic machines. For example, a version of the Sequoia touchscreen voting machine has a yellow button on the back side that allows repeated voting. Pressing the button triggers two audible beeps to alert election observers about the illegal votes.[62]
- In the 1883 election for the district of Cook, in Queensland, Australia, arrests were made in connection with accusations of ballot stuffing, and the election committee subsequently changed the result of the election.
- The Major League Baseball All-Star Game has suffered from ballot stuffing more than once.
- In 1957, Cincinnati Reds fans arranged for seven of the eight elected starting fielders to be Reds players.
- In 1999, the online ballot was stuffed in favor of Nomar Garciaparra.
- In 2015, Major League Baseball annulled 65 million (out of a total of 620 million) online ballots.
- During the 2018 Russian Presidential Election, there were multiple instances, some caught on camera, throughout Russia of voters and polling-staff alike stuffing multiple votes for incumbent President Vladimir Putin in the ballot box.[63]
Misrecording of votes
Votes may be misrecorded at source, on a ballot paper or voting machine, or later in misrecording totals. The 2019 Malawian general election was nullified by the Constitutional Court in 2020 because many results were changed by use of correction fluid, as well as duplicate, unverified and unsigned results forms.[64] [65]
Where votes are recorded through electronic or mechanical means, the voting machinery may be altered so that a vote intended for one candidate is recorded for another, or electronic results are duplicated or lost, and there is rarely evidence whether the cause was fraud or error.[66] [67] [68]
Many elections feature multiple opportunities for unscrupulous officials or 'helpers' to record an elector's vote differently from their intentions. Voters who require assistance to cast their votes are particularly vulnerable to having their votes stolen in this way. For example, a blind or illiterate person may be told that they have voted for one party when in fact they have been led to vote for another.
Misuse of proxy votes
Proxy voting is particularly vulnerable to election fraud, due to the amount of trust placed in the person who casts the vote. In several countries, there have been allegations of retirement home residents being asked to fill out 'absentee voter' forms. When the forms are signed and gathered, they are secretly rewritten as applications for proxy votes, naming party activists or their friends and relatives as the proxies. These people, unknown to the voter, cast the vote for the party of their choice. In the United Kingdom, this is known as 'granny farming.'[69]
Destruction or invalidation of ballots
One of the simplest methods of electoral fraud is to destroy ballots for an opposing candidate or party. While mass destruction of ballots can be difficult to execute without drawing attention, in a very close election, it may be possible to destroy a very small number of ballot papers without detection, thereby changing the overall result. Blatant destruction of ballot papers can render an election invalid and force it to be re-run. If a party can improve its vote on the re-run election, it can benefit from such destruction as long as it is not linked to it.
Another method is to make it appear that the voter has spoiled his or her ballot, thus rendering it invalid. Typically this would be done by adding another mark to the paper, making it appear that the voter has voted for more candidates than entitled, for instance. It would be difficult to do this to a large number of paper ballots without detection in some locales, but altogether too simple in others, especially jurisdictions where legitimate ballot spoiling by voter would serve a clear and reasonable aim. Examples may include emulating protest votes in jurisdictions that have recently had and since abolished a "none of the above" or "against all" voting option, civil disobedience where voting is mandatory, and attempts at discrediting or invalidating an election. An unusually large share of invalidated ballots may be attributed to loyal supporters of candidates that lost in primaries or previous rounds, did not run or did not qualify to do so, or some manner of protest movement or organized boycott.
Tampering with electronic voting systems
General tampering
All voting systems face threats of some form of electoral fraud. The types of threats that affect voting machines vary.[70] Research at Argonne National Laboratories revealed that a single individual with physical access to a machine, such as a Diebold Accuvote TS, can install inexpensive, readily-available electronic components to manipulate its functions.[71][72]
Other approaches include:
- Tampering with the software of a voting machine to add malicious code that alters vote totals or favors a candidate in any way.
- Multiple groups have demonstrated this possibility.[73][74][75]
- Private companies manufacture these machines. Many companies will not allow public access or review of the machines' source code, claiming fear of exposing trade secrets.[76]
- Tampering with the hardware of the voting machine to alter vote totals or favor any candidate.[74]
- Some of these machines require a smart card to activate the machine and vote. However, a fraudulent smart card could attempt to gain access to voting multiple times[77] or be pre-loaded with negative votes to favor one candidate over another, as has been demonstrated.
- Abusing the administrative access to the machine by election officials might also allow individuals to vote multiple times.
- Election results that are sent directly over the internet from the polling place centre to the vote-counting authority can be vulnerable to a man-in-the-middle attack, where they are diverted to an intermediate website where the man in the middle flips the votes in favour of a certain candidate and then immediately forwards them on to the vote-counting authority. All votes sent over the internet violate the chain of custody and hence should be avoided by driving or flying memory cards in locked metal containers to the vote-counters. For purposes of getting quick preliminary total results on election night, encrypted votes can be sent over the internet, but final official results should be tabulated the next day only after the actual memory cards arrive in secure metal containers and are counted.[78]
United States
In 2014-2017 an intruder had control of the state computer in Georgia which programmed vote-counting machines for all counties. The same computer also held voter registration records. The intrusion exposed all election files in Georgia since then to compromise and malware. The FBI studied that computer in 2017, and public disclosure came in 2020 from a court case.[79] [80] [81] Georgia did not have paper ballots to measure the amount of error in electronic tallies.
In October 2016 Russians accessed the internal computers of VR Systems, which provides election services, including compilation of election results and their release on the web, in 8 states.[82] The intruders damaged 10 computers.[83] [84] The NSA prepared a classified report in May 2017, and it was leaked in June 2017. Whether the damage affected vote tallies has not been revealed.[82]
Ukraine
In 2014 Ukraine's central election system was hacked. Officials found and removed a virus and said the totals were correct.[85]
South Africa
In 1994, the election which brought majority rule and put Nelson Mandela in office, South Africa's election compilation system was hacked, so they re-tabulated by hand.[86] [87] [88]
Voter impersonation
United States
Some commentators, such as former Federal Election Commission member Hans von Spakovsky, have claimed that voter impersonation fraud, in which one person votes by impersonating another, eligible voter, is widespread, but documentation has been scarce and prosecutions rare. Numerous others, such as Professor Larry Sabato, and a variety of studies have shown this to be "relatively rare" in the USA.[89] Since 2013, when the US Supreme Court ruled that a provision of the Voting Rights Act was no longer enforceable, several states have passed voter ID laws, ostensibly to counter the alleged fraud. But many experts counter that voter ID laws are not very effective against some forms of impersonation. These ID laws have been challenged by minority groups that claimed to be disadvantaged by the changes. By August 2016, four federal court rulings overturned laws or parts of such laws because they placed undue burdens on minority populations, including African Americans and Native Americans.[90] In each case: Texas, North Carolina, Wisconsin, and North Dakota, and may adversely affect minority voters. The states were required to accept alternatives for the November 2016 elections. These cases are expected to reach the US Supreme Court for hearings. In April 2020, a 20-year voter fraud study by MIT University found the level of fraud "exceedingly rare" since it occurs only in "0.00006 percent" of instances nationally, and, in one state, "0.000004 percent — about five times less likely than getting hit by lightning in the United States."[5]
Allegations of widespread voter fraud in the 2016 United States presidential election by busing out-of-state voters to New Hampshire were found to be false.[91] Suspicions of hacking of electronic voting machines in Wisconsin, Michigan, and Pennsylvania were determined to be unfounded.[92]
The N.C. Board of Elections reported in 2017 on questions of voter fraud and the state's proposed voter ID law. The report showed that out of 4,769,640 votes cast in the November 2016 election in North Carolina, only one illegal vote would potentially have been blocked by the voter ID law. The investigation found fewer than 500 incidences of invalid ballots cast, the vast majority of which were cast by individuals on probation for felony who were likely not aware that this status disqualified them from voting, and the total amount of invalid votes was far too small to have affected the outcome of any race in North Carolina in the 2016 election.[93][94]
Artificial results
In particularly corrupt regimes, the voting process may be nothing more than a sham, to the point that officials simply announce whatever results they want, sometimes without even bothering to count the votes. While such practices tend to draw international condemnation, voters typically have little if any recourse, as there would seldom be any ways to remove the fraudulent winner from power, short of a revolution.
In Turkmenistan, incumbent President Gurbanguly Berdymukhamedov received 97.69% of votes in the 2017 election, with his sole opponent, who was seen as pro-government, in fact being appointed by Berdymukhamedov.
Postal ballot fraud
Fraud with absentee or postal ballots has been found occasionally in the United Kingdom,[95] and the United States[96] and has been alleged in Malaysia.[97][98] In both the United Kingdom and the United States, experts estimate there is more fraud with postal ballots than in-person voting, and that even so it has affected only a few local elections.[99][100][95]
Types of fraud have included pressure on voters from family or others, since the ballot is not cast in secret;[95][101][102] collection of ballots by dishonest collectors who mark votes or fail to deliver ballots;[103][104] and insiders changing or destroying ballots after they arrive.[105][106]
A significant measure to prevent some types of fraud has been to require the voter's signature on the outer envelope, which is compared to one or more signatures on file before taking the ballot out of the envelope and counting it.[95][107] Not all places have standards for signature review,[108] and there have been calls to update signatures more often to improve this review.[95][107] While any level of strictness involves rejecting some valid votes and accepting some invalid votes,[109] there have been concerns that signatures are improperly rejected from young and minority voters at higher rates than others, with no or limited ability of voters to appeal the rejection.[110] [111]
Some problems have inherently limited scope, such as family pressure, while others can affect several percent of the vote, such as dishonest collectors[95] and signature verification.[110]
In legislature
Vote fraud can also take place in legislatures. Some of the forms used in national elections can also be used in parliaments, particularly intimidation and vote-buying. Because of the much smaller number of voters, however, election fraud in legislatures is qualitatively different in many ways. Fewer people are needed to 'swing' the election, and therefore specific people can be targeted in ways impractical on a larger scale. For example, Adolf Hitler achieved his dictatorial powers due to the Enabling Act of 1933. He attempted to achieve the necessary two-thirds majority to pass the Act by arresting members of the opposition, though this turned out to be unnecessary to attain the needed majority. Later, the Reichstag was packed with Nazi party members who voted for the Act's renewal.
In many legislatures, voting is public, in contrast to the secret ballot used in most modern public elections. This may make their elections more vulnerable to some forms of fraud since a politician can be pressured by others who will know how he or she has voted. However, it may also protect against bribery and blackmail, since the public and media will be aware if a politician votes in an unexpected way. Since voters and parties are entitled to pressure politicians to vote a particular way, the line between legitimate and fraudulent pressure is not always clear.
As in public elections, proxy votes are particularly prone to fraud. In some systems, parties may vote on behalf of any member who is not present in parliament. This protects those members from missing out on voting if prevented from attending parliament, but it also allows their party to prevent them from voting against its wishes. In some legislatures, proxy voting is not allowed, but politicians may rig voting buttons or otherwise illegally cast "ghost votes" while absent.[112]
Detection and prevention
The three main strategies for the prevention of electoral fraud in society are: 1) Auditing the election process, 2) Deterrence through consistent and effective prosecution; and 3) Cultivation of mores that discourage corruption. Some of the main fraud prevention tactics can be summarised as secrecy and openness. The secret ballot prevents many kinds of intimidation and vote selling, while transparency at all other levels of the electoral process prevents and allows detection of most interference.
Election audits
Election auditing refers to any review conducted after polls close for the purpose of determining whether the votes were counted accurately (a results audit) or whether proper procedures were followed (a process audit), or both.
Audits vary and can include checking that the number of voters signed in at the polls matches the number of ballots, seals on ballot boxes and storage rooms are intact, computer counts (if used) match hand counts, and counts are accurately totaled.
Election recounts are a specific type of audit, with elements of both results and process audits.
Prosecution
In the United States the goal of prosecutions is not to stop fraud or keep fraudulent winners out of office; it is to deter and punish years later. The Justice Department has published Federal Prosecution of Election Offenses in eight editions from 1976 to 2017, under Presidents Ford, Carter, Reagan, Clinton, Bush and Trump. It says, "Department does not have authority to directly intercede in the election process itself.... overt criminal investigative measures should not ordinarily be taken... until the election in question has been concluded, its results certified, and all recounts and election contests concluded."[113][114] Sentencing guidelines provide a range of 0–21 months in prison for a first offender;[115] offense levels range from 8 to 14.[116] Investigation, prosecution and appeals can take over 10 years.[117]
In the Philippines, former President Gloria Macapagal-Arroyo was arrested in 2011 following the filing of criminal charges against her for electoral sabotage, in connection with the 2007 Philippine general election. She was accused of conspiring with election officials to ensure the victory of her party's senatorial slate in the province of Maguindanao, through the tampering of election returns.[118]
Mores
The patterns of conventional behaviour in a society, or mores, are an effective means for preventing electoral fraud and corruption in general. A good example is Sweden, where the culture has a strong tendency toward positive values, resulting in a low incidence of political corruption.[119] Until recently Canada had a similar reputation. The In and Out scandal of 2008 and the Robocall scandal of 2011 has tarnished Canada's electoral integrity.
An advantage of cultivating positive mores as a prevention strategy is that it is effective across all electoral systems and devices. A disadvantage is that it makes other prevention and detection efforts more difficult to implement because members of society generally have more trust and less of a sense for fraudulent methods.
Secret ballot
The secret ballot, in which only the voter knows how they have voted, is believed by many to be a crucial part of ensuring free and fair elections through preventing voter intimidation or retribution.[120] Others argue that the secret ballot enables election fraud (because it makes it harder to verify that votes have been counted correctly) [121][122] and that it discourages voter participation.[123] Although the secret ballot was sometimes practiced in ancient Greece and was a part of the Constitution of the Year III of 1795, it only became common in the nineteenth century. Secret balloting appears to have been first implemented in the former British colony—now an Australian state—of Tasmania on 7 February 1856. By the turn of the century, the practice had spread to most Western democracies.
In the United States, the popularity of the Australian ballot grew as reformers in the late 19th century sought to reduce the problems of election fraud. Groups such as the Greenbackers, Nationalist, and more fought for those who yearned to vote, but were exiled for their safety. George Walthew, Greenback, helped initiate one of the first secret ballots in America in Michigan in 1885. Even George Walthew had a predecessor in John Seitz, Greenback, who campaigned a bill to " preserve the purity of elections" in 1879 after the discovery of Ohio's electoral fraud in congressional elections.
The efforts of many helped accomplish this and led to the spread of other secret ballots all across the country. As mentioned on February 18, 1890, in the Galveston News "The Australian ballot has come to stay. It protects the independence of the voter and largely puts a stop to vote to buy." Before this, it was common for candidates to intimidate or bribe voters, as they would always know who had voted which way.
Transparency
Most methods of preventing electoral fraud involve making the election process completely transparent to all voters, from nomination of candidates through casting of the votes and tabulation.[124] A key feature in ensuring the integrity of any part of the electoral process is a strict chain of custody.
To prevent fraud in central tabulation, there has to be a public list of the results from every single polling place. This is the only way for voters to prove that the results they witnessed in their election office are correctly incorporated into the totals.
End-to-end auditable voting systems provide voters with a receipt to allow them to verify their vote was cast correctly, and an audit mechanism to verify that the results were tabulated correctly and all votes were cast by valid voters. However, the ballot receipt does not permit voters to prove to others how they voted, since this would open the door towards forced voting and blackmail. End-to-end systems include Punchscan and Scantegrity, the latter being an add-on to optical scan systems instead of a replacement.
In many cases, election observers are used to help prevent fraud and assure voters that the election is fair. International observers (bilateral and multilateral) may be invited to observe the elections (examples include election observation by the Organisation for Security and Cooperation in Europe (OSCE), European Union election observation missions, observation missions of the Commonwealth of Independent States (CIS), as well as international observation organised by NGOs, such as CIS-EMO, European Network of Election Monitoring Organizations (ENEMO), etc.). Some countries also invite foreign observers (i.e. bi-lateral observation, as opposed to multi-lateral observation by international observers).
In addition, national legislatures of countries often permit domestic observation. Domestic election observers can be either partisan (i.e. representing interests of one or a group of election contestants) or non-partisan (usually done by civil society groups). Legislations of different countries permit various forms and extents of international and domestic election observation.
Election observation is also prescribed by various international legal instruments. For example, paragraph 8 of the 1990 Copenhagen Document states that "The [OSCE] participating States consider that the presence of observers, both foreign and domestic, can enhance the electoral process for States in which elections are taking place. They, therefore, invite observers from any other CSCE participating States and any appropriate private institutions and organisations who may wish to do so to observe the course of their national election proceedings, to the extent permitted by law. They will also endeavour to facilitate similar access for election proceedings held below the national level. Such observers will undertake not to interfere in the electoral proceedings".
Critics note that observers cannot spot certain types of election fraud like targeted voter suppression or manipulated software of voting machines.
Statistical indicators and election forensics
Various forms of statistics can be indicators of election fraud, e.g. exit polls which diverge from the final results. Well-conducted exit polls serve as a deterrent to electoral fraud. However, exit polls are still notoriously imprecise. For instance, in the Czech Republic, some voters are afraid or ashamed to admit that they voted for the Communist Party (exit polls in 2002 gave the Communist party 2–3 percentage points less than the actual result).
When elections are marred by ballot-box stuffing (e.g., the Armenian presidential elections of 1996 and 1998), the affected polling stations will show abnormally high voter turnouts with results favouring a single candidate. By graphing the number of votes against turnout percentage (i.e., aggregating polling stations results within a given turnout range), the divergence from bell-curve distribution gives an indication of the extent of the fraud. Stuffing votes in favour of a single candidate affects votes vs. turnout distributions for that candidate and other candidates differently; this difference could be used to quantitatively assess the number of votes stuffed. Also, these distributions sometimes exhibit spikes at round-number turnout percentage values.[125][126][127] High numbers of invalid ballots, overvoting or undervoting are other potential indicators. Risk-limiting audits are methods to assess the validity of an election result statistically without the effort of a full election recount.
Though election forensics can determine if election results are anomalous, the statistics themselves are not indicative of fraud. Election forensics can be combined with other fraud detection and prevention strategies, such as in-person monitoring.[128]
Voting machine integrity
One method for verifying voting machine accuracy is Parallel Testing, the process of using an independent set of results compared to the original machine results. Parallel testing can be done prior to or during an election. During an election, one form of parallel testing is the VVPAT. Voter-verified paper audit trail (VVPAT) or verified paper record (VPR) is a method of providing feedback to voters using a ballotless voting system. A VVPAT is intended as an independent verification system for voting machines designed to allow voters to verify that their vote was cast correctly, to detect possible election fraud or malfunction, and to provide a means to audit the stored electronic results. This method is only effective if statistically significant numbers of voters verify that their intended vote matches both the electronic and paper votes.
On election day, a statistically significant number of voting machines can be randomly selected from polling locations and used for testing. This can be used to detect potential fraud or malfunction unless manipulated software would only start to cheat after a certain event like a voter pressing a special key combination (Or a machine might cheat only if someone doesn't perform the combination, which requires more insider access but fewer voters).
Another form of testing is Logic & Accuracy Testing (L&A), pre-election testing of voting machines using test votes to determine if they are functioning correctly.
Another method to ensure the integrity of electronic voting machines is independent software verification and certification.[124] Once a software is certified, code signing can ensure the software certified is identical to that which is used on election day. Some argue certification would be more effective if voting machine software was publicly available or open source.
Certification and testing processes conducted publicly and with oversight from interested parties can promote transparency in the election process. The integrity of those conducting testing can be questioned.
Testing and certification can prevent voting machines from being a black box where voters cannot be sure that counting inside is done as intended.[124]
One method that people have argued would help prevent these machines from being tampered with would be for the companies that produce the machines to share the source code, which displays and captures the ballots, with computer scientists. This would allow external sources to make sure that the machines are working correctly.[76]
Notable United States legislation
Help America Vote Act
The Help America Vote Act (Pub.L. 107–252), or HAVA, is a United States federal law enacted on October 29, 2002.[129] It was drafted (at least in part) in reaction to the controversy surrounding the 2000 U.S. presidential election. The goals of HAVA are:[130] to replace punchcard and lever-based voting systems; create the Election Assistance Commission to assist in the administration of Federal elections; and establish minimum election administration standards.
Voting Rights Act of 1965
This was the most important federal legislation of the 20th century to protect voting rights, especially of ethnic and language minorities who had been disenfranchised for decades by states' constitutions and practices. Initially, it was particularly important for enforcing the constitutional right of African Americans in the South to vote, where millions of people had been mostly disenfranchised since the turn of the 20th century and excluded from politics. The law has also protected other ethnicities, such as Hispanics, Asians, Native Americans, and language minorities in other states, who have been discriminated against at various times, especially in the process of voter registration and electoral practices.
Civil Rights Act of 1964
The Civil Rights Act of 1964 (Pub.L. 88–352, 78 Stat. 241, enacted July 2, 1964) was a landmark piece of legislation in the United States[131] that outlawed major forms of discrimination against African Americans and other minorities.
See also
- Administrative resource
- American Center for Voting Rights
- Branch stacking
- Caging list
- Cooping
- Corruption
- Electoral integrity
- Florida Central Voter File (purging controversy)
- Foreign electoral intervention
- Gerrymandering
- List of controversial elections
- List of UK Parliamentary election petitions
- Notable instances of ballot box stuffing
- Political corruption
- Postal voting
- Show election
- Smear campaign
- Voter suppression
- Carousel voting
- Bulgarian train
Further reading
General
- Lehoucq, Fabrice. "Electoral fraud: Causes, types, and consequences." Annual review of political science (2003) 6#1 pp. 233–56.
- Schaffer, Frederic Charles. The hidden costs of clean election reform (Cornell University Press, 2008)
Australia
- McGrath, Amy. The Forging of Votes, Tower House Publications, Kensington, NSW (1994)
- McGrath, Amy. Frauding of Elections, Tower House Publications and H.S. Chapman Society, Brighton-le Sands, NSW (2003)
- McGrath, Amy. (The Frauding of Votes, Tower House Publications, Kensington, NSW 1996)
- Perry, Peter John. Political Corruption in Australia: A Very Wicked Place? (Ashgate Pub Limited, 2001)
Canada
- Atkinson, Michael M., and Gerald Bierling. "Politicians, the public and political ethics: Worlds apart." Canadian Journal of Political Science (2005) 38#4: 1003.
France
- Ebhardt, Christian. "In Search of a Political Office: Railway Directors and Electoral Corruption in Britain and France, 1820-1870." Journal of Modern European History (2013) 11#1 pp. 72–87.
Germany
- Anderson, Margaret Lavinia. Practicing Democracy: Elections and Political Culture in Imperial Germany (2000)[132]
- Ziblatt, Daniel. "Shaping Democratic Practice and the Causes of Electoral Fraud: The Case of Nineteenth-Century Germany." American Political Science Review (2009) 103#1 pp. 1–21.
United Kingdom
- Gash, Norman. Politics in the Age of Peel: A Study in the Technique of Parliamentary Representation 1830–1850 (1953)
- O'Gorman, Frank. Voters, Patrons and Parties: The Unreformed Electoral System of Hanoverian England, 1734–1832 (Oxford, 1989).
- Harling, Philip. "Rethinking "Old Corruption," Past & Present (1995) No. 147 pp. 127–58[133]
- Namier, Lewis Bernstein. The structure of politics at the accession of George III (London: Macmillan, 1957)
- O'Leary, Cornelius. The elimination of corrupt practices in British elections, 1868–1911 (Clarendon Press, 1962)
Latin America
- Hartlyn, Jonathan, and Arturo Valenzuela, "Democracy in Latin America since 1930," in Leslie Bethell, ed. Latin America: Politics and Society since 1930 (1998), 3–66.
- Molina, Iván and Fabrice Lehoucq. "Political Competition and Electoral Fraud: A Latin American Case Study," Journal of Interdisciplinary History (1999) 30#2 pp. 199–234[134]
- Posada-Carbó, Eduardo. "Electoral Juggling: A Comparative History of the Corruption of Suffrage in Latin America, 1830–1930." Journal of Latin American Studies (2000). pp. 611–44.
- Ricci, Paolo. "'Beheading', Rule Manipulation and Fraud: The Approval of Election Results in Brazil, 1894–1930." Journal of Latin American Studies (2012) 44#3 pp. 495–521.
- Silva, Marcos Fernandes da. "The political economy of corruption in Brazil." Revista de Administração de Empresas (1999) 39#3 pp. 26–41.
Turkey
United States
- Argersinger, Peter H. "New perspectives on election fraud in the Gilded Age." Political Science Quarterly (1985) 100#4 pp. 669–87[138]
- Campbell, Tracy. Deliver the Vote: A History of Election Fraud, An American Political Tradition, 1742 2004 (Basic Books, 2005)
- Fackler, Tim, and Tse-min Lin. "Political corruption and presidential elections, 1929–1992." Journal of Politics 57 (1995): 971–93.[139]
- Mayfield, Loomis. "Voting Fraud in Early Twentieth-Century Pittsburgh," Journal of Interdisciplinary History (1993) 29#1 59–84[140]
- Morris Jr., Roy. Fraud of the Century: Rutherford B. Hayes, Samuel Tilden, and the Stolen Election of 1876 (2007)[141]
- Summers, Mark Wahlgren. The Era of Good Stealings (1993), covers corruption 1868–1877
- Sydnor, Charles. Gentlemen Freeholders: Political Practices in Washington's Virginia (1952), 18th century
References
- Jones, Douglas (2005-10-07). "Threats to Voting Systems". University of Iowa. Retrieved 2020-06-25.
- also at Jones, Douglas (2005-10-07). "An Expanded Threat Taxonomy, pages 178-179". National Institute of Standards and Technology. Retrieved 2020-06-23.
- Myagkov, Mikhail G.; Peter C. Ordeshook; Dimitri Shakin (2009-05-31). The Forensics of Election Fraud: Russia and Ukraine. Cambridge University Press. ISBN 978-0-521-76470-4.
- Alvarez, Michael; Hall, Thad; Hyde, Susan (2008). Election Fraud: Detecting and Deterring Electoral Manipulation.
- Dawn Brancati. 2016. Democracy Protests: Origins, Features, and Significance. New York: Cambridge University Press.
- Staff (April 28, 2020). "Election 2020 - Voting by mail in the U.S. is safe, honest, and fair. - Let's put the vote-by-mail 'fraud' myth to rest". MIT University. Retrieved July 28, 2020.
- Archived November 11, 2007, at the Wayback Machine
- Williamson, Chilton (1968). American Suffrage from Property to Democracy. Princeton, NJ: Princeton U. Press. ASIN B000FMPMK6.
- Saltman, Roy G. (January 2006). The History and Politics of Voting Technology. Palgrave Macmillan. ISBN 1-4039-6392-4.
- Magill v. Porter Magill v. Weeks, H=House of Lords Judgments, 13 December 2001. Accessed 2012-02-16.
- Sadiq, Kamal (2005). "When States Prefer Non-Citizens Over Citizens: Conflict Over Illegal Immigration into Malaysia" (PDF). International Studies Quarterly. 49: 101–22. doi:10.1111/j.0020-8833.2005.00336.x. Archived from the original (PDF) on 2008-06-14. Retrieved 2008-04-23.
- Young, Toby (17 June 2015). "Why Tories should join Labour and back Jeremy Corbyn" – via www.telegraph.co.uk.
- "Labour's response to #ToriesForCorbyn shows they really have lost the plot - Coffee House". 24 June 2015.
- "Labour's response to #ToriesForCorbyn shows they really have lost the plot - Coffee House". 24 June 2015.
- Bazelon, Emily (2018-09-26). "Will Florida's Ex-Felons Finally Regain the Right to Vote?". The New York Times. ISSN 0362-4331. Retrieved 2018-12-04.
- Magaloni, Beatriz. "Autocratic Elections, Voters, and the Game of Fraud" (PDF). Yale University. Retrieved 10 December 2015.
- Poundstone, William (2009). Gaming the Vote: Why Elections Aren't Fair (And What We Can Do About It). Macmillan. p. 170. ISBN 9780809048922.
- Bialik, Carl (May 14, 2011). "Latest Issue on the Ballot: How to Hold a Vote". Wall Street Journal. Retrieved June 29, 2012.
- "Did bomb threat stifle vote? (Capital Times)". Madison.com. Archived from the original on March 4, 2009. Retrieved 2012-05-03.
- Sullivan, Joseph F. (1993-11-13). "Florio's Defeat Revives Memories of G.O.P. Activities in 1981". New York Times. Retrieved 2008-10-07.
- Archived October 26, 2006, at the Wayback Machine
- "Intimidation and Deceptive Practices EP365". Archived from the original on 2008-01-21. Retrieved 2018-04-23.
- "Incidents Of Voter Intimidation & Suppression". 2006-11-08. Archived from the original on April 4, 2007. Retrieved 2012-05-03.
- Church Report (Covert Action in Chile 1963–1973), United States Senate Church Committee, 1975
- "Fraudulent election calls traced to Racknine Inc., an Edmonton firm with Tory links | News | National Post". News.nationalpost.com. 2012-02-23. Retrieved 2012-05-03.
- "Lynne Rienner Publishers - Elections for Sale The Causes and Consequences of Vote Buying". www.rienner.com.
- Mark Wahlgren Summers. Party Games: Getting, Keeping, and Using Power in Gilded Age Politics. ISBN 978-0807855379.
- Joseph Grego (1886). A History of Parliamentary Elections and Electioneering in the Old Days . Retrieved 2015-05-29.
- "Parliamentary Electorates And Elections Act 1912 – Section 149, New South Wales Consolidated Acts". Austlii.edu.au. Archived from the original on 2011-11-30. Retrieved 2012-05-03.
- Herbeck, Dan (November 15, 2011). Resentments abound in Seneca power struggle. The Buffalo News. Retrieved November 16, 2011.
- Larreguy, Horacio; Marshall, John; Querubín, Pablo (2016). "Parties, Brokers, and Voter Mobilization: How Turnout Buying Depends Upon the Party's Capacity to Monitor Brokers". American Political Science Review. 110: 160–179. doi:10.1017/S0003055415000593.
- Stokes, Susan C (2005). "Perverse Accountability: A Formal Model of Machine Politics with Evidence from Argentina". American Political Science Review. 99 (3): 315. doi:10.1017/S0003055405051683.
- Nichter, Simeon (2008). "Vote Buying or Turnout Buying? Machine Politics and the Secret Ballot". American Political Science Review. 102 (1): 19–31. doi:10.1017/S0003055408080106. JSTOR 27644495.
- Jones, Douglas (2005-10-07). "Chain Voting" (PDF). University of Iowa. Retrieved 2020-06-25.
- also at Jones, Douglas (2005-08-26). "Chain Voting (pages 53-55". National Institute of Standards and Technology. Retrieved 2020-06-23.
- "Vote-Buying and Reciprocity". Econometrica. 80 (2): 863. 2012. doi:10.3982/ECTA9035. hdl:10419/55130.
- Gersbach, Hans; Mühe, Felix (2011). "Vote-Buying and Growth". Macroeconomic Dynamics. 15 (5): 656. doi:10.1017/S1365100510000246.
- Auyero, Javier (April 1999). "'From the Client's Point(s) of View': How Poor People Perceive and Evaluate Political Clientelism". Theory and Society. 28 (2): 297–334. doi:10.1023/A:1006905214896. JSTOR 3108473.
- Mares, Isabela; Young, Lauren (2016). "Buying, Expropriating, and Stealing Votes". Annual Review of Political Science. 19: 267–288. doi:10.1146/annurev-polisci-060514-120923.
- Brusco, Valeria; Nazareno, Marcelo; Stokes, Susan Carol (2004). "Vote Buying in Argentina". Latin American Research Review. 39 (2): 66. doi:10.1353/lar.2004.0022. S2CID 154003297.
- Vilalta, Carlos (2010). "Vote-buying crime reports in Mexico: Magnitude and correlates". Crime, Law and Social Change. 54 (5): 325. doi:10.1007/s10611-010-9260-7.
- Serra, Gilles (10 May 2016). "Vote Buying with Illegal Resources: Manifestation of a Weak Rule of Law in Mexico". Journal of Politics in Latin America. 8 (1): 129–150. doi:10.1177/1866802X1600800105 – via journals.sub.uni-hamburg.de.
- Serra, Gilles (10 May 2016). "Vote Buying with Illegal Resources: Manifestation of a Weak Rule of Law in Mexico". Journal of Politics in Latin America. 8 (1): 129–150. doi:10.1177/1866802X1600800105.
- Berwick, Angus (14 November 2018). "How ZTE helps Venezuela create China-style social control". Reuters.
- "As Trump Adds Sanctions on Venezuela, Its Neighbors Reject Election Result". The New York Times. 21 May 2018. ISSN 0362-4331. Retrieved 21 May 2018.
- "Súmate denunció complicidad del CNE por compra de votos para reelección de Maduro". La Patilla (in Spanish). 17 May 2018. Retrieved 18 May 2018.
- "Sepa qué le dejó Maduro a Delta Amacuro" (in Spanish). Con el Mazo Dando. 24 April 2018. Retrieved 12 May 2018.
- "Gobierno reactivó Aeropuerto Nacional de Tucupita" (in Spanish). El Mundo. 25 April 2018. Retrieved 12 May 2018.
- "Aprobación de recursos y un breve discurso dio Maduro durante campaña en Delta Amacuro". Contrapunto. 24 April 2018. Archived from the original on 10 February 2019. Retrieved 12 May 2018.
- "Maduro promete ser el "protector" de Amazonas y "golpear" a las mafias de la gasolina". Efecto Cocuyo. 8 May 2018.
- "Maduro prometió casas, gasolina y trabajo para Puerto Ayacucho" (in Spanish). El Pitazo. 8 May 2018. Retrieved 12 May 2018.
- "Pdvsa activa plan especial de suministro de combustible en Amazonas". Últimas Noticas. 9 May 2018. Archived from the original on 12 May 2018. Retrieved 12 May 2018.
- "Pdvsa reactiva suministro de gasolina tras reclamos a Maduro en Amazonas" (in Spanish). El Estímulo. 9 May 2018. Retrieved 12 May 2018.
- Bratton, Michael (2008). "Vote buying and violence in Nigerian election campaigns". Electoral Studies. 27 (4): 621. doi:10.1016/j.electstud.2008.04.013.
- Kramon, Eric (2016). "Where is vote buying effective? Evidence from a list experiment in Kenya". Electoral Studies. 44: 397. doi:10.1016/j.electstud.2016.09.006.
- Election Shenanigans - Kenyan Hybrid Warfare (Book). ASIN B08DMZJ893.
- Election Shenanigans - Kenyan Hybrid Warfare (Book). ASIN B08DGP72MH.
- "Vote-buying mars midterm elections". Philippine Daily Inquirer. Retrieved May 13, 2019.
- "'Massive' vote-buying continues on Election Day". CNN Philippines.
- Archived October 21, 2006, at the Wayback Machine
- Lacayo, Richard. "Florida recount: In the eye of the storm". CNN. Archived from the original on 2011-06-22.
- "Sidolagda valsedlar inget lagbrott - sr.se". Archived from the original on 2009-06-15.
- Hicks, Jonathon (July 24, 2004). "Seeing Double on Ballot: Similar Names Sow Confusion". The New York Times. The New York Times Company. Archived from the original on 2009-03-04. Retrieved 18 December 2008.
- "VoteTrustUSA – Sequoia: Button On E-voting Machine Allows Multiple Votes". votetrustusa.org. Archived from the original on 2016-03-15.
- Bodner, Matthew (March 19, 2018). "Analysis | Videos online show blatant ballot-stuffing in Russia". Washington Post.
- "Malawi anxiously awaits verdict on alleged presidential election fraud". rfi.fr. Retrieved 3 February 2020.
- "Malawi top court annuls presidential election results". Al Jazeera. Retrieved 3 February 2020.
- Freed, Benjamin (2019-01-07). "South Carolina voting machines miscounted hundreds of ballots, report finds". Retrieved 2020-02-05.
- Buell, Duncan (2018-12-23). Analysis of the Election Data from the 6 November 2018 General Election in South Carolina (PDF) (Report). Retrieved 2020-02-05.
- McDaniel; et al. (2007-12-07). EVEREST: Evaluation and Validation of Election-Related Equipment, Standards and Testing (PDF) (Report). Retrieved 2020-02-05.
- "Row over Alzheimer woman's proxy". BBC News. BBC MMVIII. 2005-05-04. Archived from the original on 19 April 2016. Retrieved 13 November 2018.
- "Threat Analyses & Papers". National Institute of Standards and Technology. October 7, 2005. Archived from the original on 21 October 2006. Retrieved 5 March 2011.
- Jaikumar Vijayan (2011-09-28). "Argonne researchers 'hack' Diebold e-voting system". Computerworld. Retrieved 2012-05-03.
- Layton, J. (2006-09-22). "How can someone tamper with an electronic voting machine". Retrieved 2011-02-27.
- "Security Analysis of the Diebold AccuVote-TS Voting Machine" (PDF). Jhalderm.com. Retrieved 2015-05-29.
- "images". Retrieved February 17, 2012.
- Bonsor and Strickland, Kevin and Jonathan (2007-03-12). "How E-Voting Works". Retrieved 2011-02-27.
- Kohno, T. "Analysis of Electronic Voting System" (PDF). Retrieved 2011-02-27.
- ""Man in the Middle" Attacks to Subvert the Vote". Electiondefensealliance.org. Archived from the original on 2015-07-21. Retrieved 2015-05-29.
- Lamb, Logan (2020-01-14). "SUPPLEMENTAL DECLARATION OF LOGAN LAMB" (PDF). CourtListener. Retrieved 2020-02-03.
- "Coalition Plaintiffs' Status Report, pages 237-244". Coalition for Good Governance. 2020-01-16. Retrieved 2020-02-03.
- Bajak, Frank (2020-01-16). "Expert: Georgia election server showed signs of tampering". Associated Press. Retrieved 2020-02-03.
- Cole, Matthew; Esposito, Richard; Biddle, Sam; Grim, Ryan (2017-06-05). "Top-Secret NSA Report Details Russian Hacking Effort Days Before 2016 Election". The Intercept. Retrieved 2020-02-03.
- "UNITED STATES OF AMERICA v. VIKTOR BORISOVICH NETYKSHO, et al, Indictment, paragraph 77b". 2018-07-13. Retrieved 2020-02-03.
- "United States v. NETYKSHO (1:18-cr-00215), paragraph 77b" (PDF). Court Listener. 2018-06-13. Retrieved 2020-02-03.
- Clayton, Mark (2014-06-17). "Ukraine election narrowly avoided 'wanton destruction' from hackers". Christian Science Monitor. ISSN 0882-7729. Retrieved 2020-02-03.
- "Excerpt from Birth: The Conspiracy to Stop the '94 Election by Peter Harris". Penguin SA @ Sunday Times Books LIVE. 2010-10-25. Retrieved 2020-02-03.
- Harris, Peter (2010). Birth : the conspiracy to stop the '94 election (1st ed.). Cape Town: Umuzi. ISBN 978-1-4152-0102-2. OCLC 683401576.
- Laing, Aislinn (2010-10-24). "Election won by Mandela 'rigged by opposition'". Daily Telegraph. ISSN 0307-1235. Retrieved 2020-02-03.
- Mayer, Jane (29 October 2012). "The Voter-Fraud Myth". The New Yorker. Retrieved 9 December 2015.
- Rober Barnes (August 1, 2016). "Federal judge blocks N. Dakota's voter-ID law, calling it unfair to Native Americans". Washington Post. Retrieved 2016-08-02.
- James Pindell (1 June 2018). "N.H. says once and for all that no one was bused in to vote". The Boston Globe. Archived from the original on 26 October 2018. Retrieved 26 October 2018.
- "Nate Silver on Twitter". Twitter. Retrieved November 24, 2016.
- https://www.charlotteobserver.com/opinion/editorials/article146486019.html
- "North Carolina State Board of Elections" (PDF) (Press release). April 21, 2017. Archived from the original (PDF) on April 25, 2017. Retrieved June 28, 2018.
- Pickles, Eric (2016-08-11). "Securing the ballot, Report of Sir Eric Pickles' review into electoral fraud" (PDF). United Kingdom Government. Retrieved 2020-06-15.
- Young, Ashley (2016-09-23). "A Complete Guide To Early And Absentee Voting". Retrieved 2020-06-15.
- "Malaysian oppn accuse govt of postal vote fraud". ABC News. March 3, 2008. Retrieved 2008-04-24.
- "One foot in the door". The Sun (Malaysia). March 27, 2008. Retrieved 2008-04-24.
- "Who Can Vote? - A News21 2012 National Project". Retrieved 2020-06-12.
- Kahn, Natasha and Corbin Carson. "Investigation: election day fraud "virtually nonexistent"". Philadelphia Inquirer. Retrieved 2020-06-15.
- Journal, Glenn R. Simpson and Evan Perez (2000-12-19). "'Brokers' Exploit Absentee Voters; Elderly Are Top Targets for Fraud". Wall Street Journal. ISSN 0099-9660. Retrieved 2020-06-12.
- Bender, William. "Nursing home resident's son: 'That's voter fraud'". Retrieved 2020-06-12.
- "Judge upholds vote-rigging claims". BBC News. 2005-04-04. Retrieved 2010-09-19.
- Robertson, Gary D. (2020-04-22). "North Carolina ballot probe defendant now faces federal charges". Times-News. Retrieved 2020-06-27.
- Mazzei, Patricia (2016-10-28). "Two women busted for election fraud in Miami-Dade in 2016". Miami Herald. Retrieved 2020-06-12.
- "Judge hears testimony in Hawkins case". Retrieved 2020-06-12.
- "Signature Verification and Mail Ballots: Guaranteeing Access While Preserving Integrity" (PDF). Stanford University. 2020-04-15. Retrieved 2020-06-01.
- "Vote at Home Policy Actions: 1 and 2 Stars" (PDF). National Vote at Home Institute. May 2020. Retrieved 2020-06-18.
- Sita, Jodi; Found, Bryan; Rogers, Douglas K. (September 2002). "Forensic Handwriting Examiners' Expertise for Signature Comparison". Journal of Forensic Sciences. 47 (5): 15521J. ISSN 0022-1198.
- Smith, Daniel (2018-09-18). "Vote-By-Mail Ballots Cast in Florida" (PDF). ACLU-Florida. Retrieved 2020-06-01.
- Wilkie, Jordan (2018-10-12). "Exclusive: High Rate of Absentee Ballot Rejection Reeks of Voter Suppression". Who What Why. Retrieved 2020-06-18.
- "Is "Ghost" Voting Acceptable?". Writ.lp.findlaw.com. 2004-04-08. Retrieved 2012-05-03.
- "Federal Prosecution of Election Offenses Eighth Edition". US Dept of Justice. September 2017. Retrieved 2019-07-13.
- "Federal Prosecution of Election Offenses". votewell.net. Retrieved 2019-07-13.
- "SENTENCING TABLE" (PDF). US Sentencing Commission. 2011. Retrieved 2019-07-13.
- "2018 Chapter 2 Part C, section 2C1.1". United States Sentencing Commission. 2018-06-27. Retrieved 2019-07-13.
- WKYT. "Ex-judge convicted of vote fraud in Clay County disbarred". Retrieved 2019-07-13.
- Jeannette I. Andrade (2011-11-18). "Electoral sabotage case filed vs Arroyo, Ampatuan, Bedol". Philippine Daily Inquirer.
- "Corruption Perceptions Index". Transparency International. Transparency International. 2011. Archived from the original on 19 June 2006. Retrieved 1 December 2011.
- "Why You Should Expect Challenges To Secret Ballots". The Federalist. 2016-07-12. Retrieved 16 July 2016.
- "Scrap the "secret" ballot – return to open voting".
- Todd Davies. "Consequences of the Secret Ballot" (PDF). Symbolic Systems Program, Stanford University.
- "Abolish the Secret Ballot". The Atlantic.
- Lundin, Leigh (2008-08-17). "Dangerous Ideas". Voting Fiasco, Part 279.236(a). Criminal Brief. Retrieved 2010-10-07.
- "podmoskovnik: Cтатья о выборах из Троицкого Варианта". Podmoskovnik.livejournal.com. Retrieved 2015-05-29.
- 27 октября 2009 года. (2009-10-27). "Статистическое исследование результатов российских выборов 2007–2009 гг. : Троицкий вариант – Наука". Trvscience.ru. Archived from the original on 2013-04-23. Retrieved 2015-05-29.
- Walter R. Mebane, Jr.; Kirill Kalinin. "Comparative Election Fraud Detection" (PDF). Personal.umich.edu. Retrieved 2015-05-29.
- Hicken, Allen; Mebane, Walter R. (2017). A Guide to Elections Forensics (PDF) (Report). University of Michigan Center for Political Studies.
- United States Department of Justice Civil Rights Division Voting Section Home Page,Help America Vote Act of 2002
- 107th U.S. Congress (October 29, 2002). "Help America Vote Act of 2002 (Pub.L. 107-252)". U.S. Government Printing Office. Retrieved 2008-10-10.
- Wright, Susan (2005), The Civil Rights Act of 1964: Landmark Antidiscrimination Legislation, The Rosen Publishing Group, ISBN 1-4042-0455-5
- Practicing Democracy: Elections and Political Culture in Imperial Germany: Margaret Lavinia Anderson: 9780691048543. ASIN 0691048541.CS1 maint: ASIN uses ISBN (link)
- Philip Harling (May 1995). "Rethinking "Old Corruption"". Past & Present. Oxford University Press. 147 (147): 127–58. doi:10.1093/past/147.1.127. JSTOR 651042.
- "Political Competition and Electoral Fraud: A Latin American Case Study" (PDF). Libres.uncg.edu. Retrieved 2015-05-29.
- "Is Something Rotten In Ankara's Mayoral Election? A Very Preliminary Statistical Analysis". Erikmeyersson.com. 2014-04-01. Retrieved 2015-05-29.
- "Trouble in Turkey's Elections". Erikmeyersson.com. 2014-04-06. Retrieved 2015-05-29.
- "Capital Fraud in Turkey? Evidence from Citizen Initiatives". Erikmeyersson.com. 2014-04-11. Retrieved 2015-05-29.
- Peter H. Argersinger (1986). "New Perspectives on Election Fraud in the Gilded Age". Political Science Quarterly. The Academy of Political Science. 100 (4): 669–87. doi:10.2307/2151546. JSTOR 2151546.
- "Political Corruption and Presidential Elections, 1929–1992" (PDF). Repositories2.lib.utexas.edu. Archived from the original (PDF) on 2016-03-04. Retrieved 2015-05-29.
- Loomis Mayfield (1993). "Voting Fraud in Early Twentieth-Century Pittsburgh". The Journal of Interdisciplinary History. The MIT Press. 24 (1): 59–84. doi:10.2307/205101. JSTOR 205101.
- "Fraud of the Century: Rutherford B. Hayes, Samuel Tilden, and the Stolen Election of 1876 eBook: Roy Morris Jr". Retrieved 2015-05-29.
External links
| Wikiquote has quotations related to: Electoral fraud |
- Voter Fraud - an article from the ACE Project
- Independent Verification: Essential Action to Assure Integrity in the Voting Process, Roy G. Saltman, August 22, 2006
- Legal provisions to prevent Electoral Fraud - an article from the ACE Project
- Was the 2004 Election Stolen? by Robert F. Kennedy Jr., June 1, 2006.
- Article referencing "four-legged voting"
- 20 Ways The 2018 Election Will Be Stolen by Jeff Reifman, October 1, 2017.