XKeyscore
XKeyscore (XKEYSCORE or XKS) is a formerly secret computer system used by the United States National Security Agency (NSA) for searching and analyzing global Internet data, which it collects continually. The NSA has shared XKeyscore with other intelligence agencies, including the Australian Signals Directorate, Canada's Communications Security Establishment, New Zealand's Government Communications Security Bureau, Britain's Government Communications Headquarters, Japan's Defense Intelligence Headquarters, and Germany's Bundesnachrichtendienst.[1]
 National Security Agency surveillance |
|---|
 |
|
Programs
|
|
Institutions
|
|
Lawsuits
|
|
Whistleblowers
|
|
Publication
|
|
Related
|
In July 2013, Edward Snowden publicly revealed the program's purpose and use by the NSA in The Sydney Morning Herald and O Globo newspapers. The code name was already public knowledge because it was mentioned in earlier articles, and, like many other code names, it appears in job postings and online résumés of employees.[2][3]
On July 3, 2014, German public broadcaster Norddeutscher Rundfunk, a member of ARD, published excerpts of XKeyscore's source code.[4] A team of experts analyzed the source code.[5]
Scope and functioning
| Part of a series on |
| Global surveillance |
|---|
| Disclosures |
| Systems |
| Agencies |
| People |
| Places |
| Laws |
| Proposed changes |
| Concepts |
| Related topics |
XKeyscore is a complicated system, and various authors have different interpretations of its actual capabilities. Edward Snowden and Glenn Greenwald explained XKeyscore as being a system which enables almost unlimited surveillance of anyone anywhere in the world, while the NSA has said that usage of the system is limited and restricted.
According to The Washington Post and national security reporter Marc Ambinder, XKeyscore is an NSA data-retrieval system which consists of a series of user interfaces, backend databases, servers and software that selects certain types of data and metadata that the NSA has already collected using other methods.[6][7]
According to Snowden and Greenwald
On January 26, 2014, the German broadcaster Norddeutscher Rundfunk asked Edward Snowden in its TV interview: "What could you do if you would use XKeyscore?" and he answered:[1]
You could read anyone's email in the world, anybody you've got an email address for. Any website: You can watch traffic to and from it. Any computer that an individual sits at: You can watch it. Any laptop that you're tracking: you can follow it as it moves from place to place throughout the world. It's a one-stop-shop for access to the NSA's information. ... You can tag individuals ... Let's say you work at a major German corporation and I want access to that network, I can track your username on a website on a forum somewhere, I can track your real name, I can track associations with your friends and I can build what's called a fingerprint, which is network activity unique to you, which means anywhere you go in the world, anywhere you try to sort of hide your online presence, your identity.
According to The Guardian's Glenn Greenwald, low-level NSA analysts can, via systems like XKeyscore, "listen to whatever emails they want, whatever telephone calls, browsing histories, Microsoft Word documents. And it's all done with no need to go to a court, with no need to even get supervisor approval on the part of the analyst."[8]
He added that the NSA's databank of collected communications allows its analysts to listen "to the minds or read the emails of everything that the NSA has stored, or look at the browsing histories or Google search terms that you've entered, and it also alerts them to any further activity that people connected to that neural network or that IP address do in the future".[8]
According to the NSA
In an official statement from July 30, 2013, the NSA said "XKeyscore is used as a part of NSA's lawful foreign signals intelligence collection system. ..." to legally obtain information about "legitimate foreign intelligence targets in response to requirements that our leaders need for information necessary to protect our nation and its interests. ... to collect the information, that enables us to perform our missions successfully – to defend the nation and to protect U.S. and allied troops abroad."[9] In terms of access, an NSA press statement reads that there is no "unchecked analyst access to NSA collection data. Access to XKeyscore, as well as all of NSA's analytic tools, is limited to only those personnel who require access for their assigned tasks." and that there are "...stringent oversight and compliance mechanisms built in at several levels. One feature is the system's ability to limit what an analyst can do with a tool, based on the source of the collection and each analyst's defined responsibilities."[10]
Workings
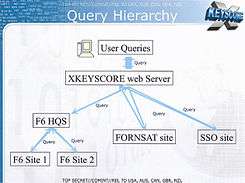
According to an NSA slide presentation about XKeyscore from 2013, it is a "DNI Exploitation System/Analytic Framework". DNI stands for Digital Network Intelligence, which means intelligence derived from internet traffic.[11]
Edward Snowden said about XKeyscore: "It's a front end search engine" in an interview with the German Norddeutscher Rundfunk.[12]
XKeyscore is a "piece of Linux software that is typically deployed on Red Hat servers. It uses the Apache web server and stores collected data in MySQL databases".[13]
XKeyscore is considered a "passive" program, in that it listens, but does not transmit anything on the networks that it targets.[5] But it can trigger other systems, which perform "active" attacks through Tailored Access Operations which are "tipping", for example, the QUANTUM family of programs, including QUANTUMINSERT, QUANTUMHAND, QUANTUMTHEORY, QUANTUMBOT and QUANTUMCOPPER and Turbulence. These run at so-called "defensive sites" including the Ramstein Air Force base in Germany, Yokota Air Base in Japan, and numerous military and non-military locations within the US. Trafficthief, a core program of Turbulence, can alert NSA analysts when their targets communicate, and trigger other software programs, so select data is "promoted" from the local XKeyscore data store to the NSA's "corporate repositories" for long term storage.[5]
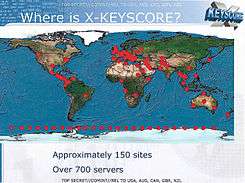
Data sources
XKeyscore consists of over 700 servers at approximately 150 sites where the NSA collects data, like "US and allied military and other facilities as well as US embassies and consulates" in many countries around the world.[14][15][16] Among the facilities involved in the program are four bases in Australia and one in New Zealand.[15]
According to an NSA presentation from 2008, these XKeyscore servers are fed with data from the following collection systems:[17]
- F6 (Special Collection Service) – joint operation of the CIA and NSA that carries out clandestine operations including espionage on foreign diplomats and leaders
- FORNSAT – which stands for "foreign satellite collection", and refers to intercepts from satellites
- SSO (Special Source Operations) – a division of the NSA that cooperates with telecommunication providers
In a single, undated slide published by Swedish media in December 2013, the following additional data sources for XKeyscore are mentioned:[18]
- Overhead – intelligence derived from American spy planes, drones and satellites
- Tailored Access Operations – a division of the NSA that deals with hacking and cyberwarfare
- FISA – all types of surveillance approved by the Foreign Intelligence Surveillance Court
- Third party – foreign partners of the NSA such as the (signals) intelligence agencies of Belgium, Denmark, France, Germany, Italy, Japan, the Netherlands, Norway, Sweden, etc.
From these sources, XKeyscore stores "full-take data", which are indexed by plug-ins that extract certain types of metadata (like phone numbers, e-mail addresses, log-ins, and user activity) and index them in metadata tables, which can be queried by analysts. XKeyscore has been integrated with MARINA, which is NSA's database for internet metadata.[11]
However, the system continuously gets so much Internet data that it can be stored only for short periods of time. Content data remain on the system for only three to five days, while metadata is stored for up to thirty days.[19] A detailed commentary on an NSA presentation published in The Guardian in July 2013 cites a document published in 2008 declaring that "At some sites, the amount of data we receive per day (20+ terabytes) can only be stored for as little as 24 hours."[20]
Types of XKeyscore
According to a document from an internal GCHQ website which was disclosed by the German magazine Der Spiegel in June 2014, there are three different types of the Xkeyscore system:[21]
- Traditional: The initial version of XKeyscore is fed with data from low-rate data signals, after being processed by the WEALTHYCLUSTER system. This traditional version is not only used by NSA but also at many intercept sites of GCHQ.
- Stage 2: This version of XKeyscore is used for higher data rates. The data are first processed by the TURMOIL system, which sends 5% of the internet data packets to XKeyscore. GCHQ only uses this version for its collection under the MUSCULAR program.
- Deep Dive: This latest version can process internet traffic at data rates of 10 gigabits per second. Data that could be useful for intelligence purposes are then selected and forwarded by using the "GENESIS selection language". GCHQ also operates a number of Deep Dive versions of XKeyscore at three locations under the codename TEMPORA.[22]
Capabilities
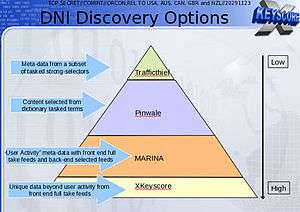
For analysts, XKeyscore provides a "series of viewers for common data types", which allows them to query terabytes of raw data gathered at the aforementioned collection sites. This enables them to find targets that cannot be found by searching only the metadata, and also to do this against data sets that otherwise would have been dropped by the front-end data processing systems. According to a slide from an XKeyscore presentation, NSA collection sites select and forward less than 5% of the internet traffic to the PINWALE database for internet content.[19]
Because XKeyscore holds raw and unselected communications traffic, analysts can not only perform queries using "strong selectors" like e-mail addresses, but also using "soft selectors", like keywords, against the body texts of e-mail and chat messages and digital documents and spreadsheets in English, Arabic and Chinese.[11]
This is useful because "a large amount of time spent on the web is performing actions that are anonymous" and therefore those activities can't be found by just looking for e-mail addresses of a target. When content has been found, the analyst might be able to find new intelligence or a strong selector, which can then be used for starting a traditional search.[11]
Besides using soft selectors, analysts can also use the following other XKeyscore capabilities:[11][23]
- Look for the usage of Google Maps and terms entered into a search engine by known targets looking for suspicious things or places.
- Look for "anomalies" without any specific person attached, like detecting the nationality of foreigners by analyzing the language used within intercepted emails. An example would be a German speaker in Pakistan. The Brazilian paper O Globo claims that this has been applied to Latin America and specifically to Colombia, Ecuador, Mexico and Venezuela.[14][24]
- Detect people who use encryption by doing searches like "all PGP usage in Iran". The caveat given is that very broad queries can result in too much data to transmit back to the analyst.
- Showing the usage of virtual private networks (VPNs) and machines that can potentially be hacked via TAO.
- Track the source and authorship of a document that has passed through many hands.
- On July 3, 2014 ARD revealed that XKeyscore is used to closely monitor users of the Tor anonymity network,[5] people who search for privacy-enhancing software on the web,[5] and readers of Linux Journal.[25]
The Guardian opined in 2013 that most of these things cannot be detected by other NSA tools, because they operate with strong selectors (like e-mail and IP addresses and phone numbers) and the raw data volumes are too high to be forwarded to other NSA databases.[11]
In 2008, NSA planned to add a number of new capabilities in the future, like VoIP, more networking protocols, Exif tags, which often include geolocation (GPS) data.[11]
Contribution to U.S. security
The NSA slides published in The Guardian during 2013 claimed that XKeyscore had played a role in capturing 300 terrorists by 2008,[11] which could not be substantiated as the redacted documents do not cite instances of terrorist interventions.
A 2011 report from the NSA unit in the Dagger Complex (close to Griesheim in Germany) said that XKeyscore made it easier and more efficient to target surveillance. Previously, analysis often accessed data NSA was not interested in. XKeyscore allowed them to focus on the intended topics, while ignoring unrelated data. XKeyscore also proved to be outstanding for tracking active groups associated with the Anonymous movement in Germany, because it allows for searching on patterns, rather than particular individuals. An analyst is able to determine when targets research new topics, or develop new behaviors.[26]
To create additional motivation, the NSA incorporated various gamification features. For instance, analysts who were especially good at using XKeyscore could acquire "skilz" points and "unlock achievements." The training units in Griesheim were apparently successful and analysts there had achieved the "highest average of skilz points" compared with all other NSA departments participating in the training program.[26]
Usage by foreign partners of the NSA
Germany
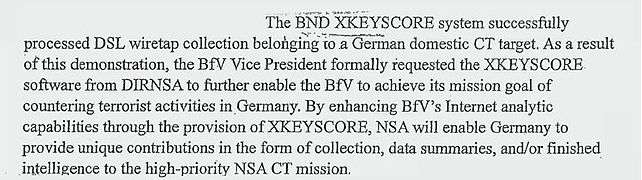
According to documents Der Spiegel acquired from Snowden, the German intelligence agencies BND (foreign intelligence) and BfV (domestic intelligence) were also allowed to use the XKeyscore system. In those documents the BND agency was described as the NSA's most prolific partner in information gathering.[27] This led to political confrontations, after which the directors of the German intelligence agencies briefed members of the German parliamentary intelligence oversight committee on July 25, 2013. They declared that XKeyscore has been used by the BND since 2007 and that the BfV has been using a test version since 2012. The directors also explained that the program is not for collecting data, but rather only for the analysis of collected data.[28]
Sweden
As part of the UKUSA Agreement, a secret treaty was signed in 1954 by Sweden with the United States, the United Kingdom, Canada, Australia and New Zealand (called the Five Eyes) for the purpose of intelligence collaboration and data sharing.[29] According to documents leaked by Snowden, the National Defence Radio Establishment (FRA) has been granted access to XKeyscore.[30]
Japan
The classified documents leaked by Snowden also indicate that in April 2013, NSA had secretly provided the XKeyscore system to the Japanese government.[31]
See also
- List of government surveillance projects
- PRISM
- File:XKeyscore presentation from 2008.pdf, a redacted presentation about X-Keyscore via The Guardian (UK) via Edward Snowden via U.S. National Security Agency
- Targeted surveillance
References
- Seipel, Hubert (January 26, 2014). "Snowden Interview: Transcript". Norddeutscher Rundfunk. p. 3. Archived from the original on January 28, 2014. Retrieved May 6, 2019.
- Greenwald, Glenn; Ackerman, Spencer (June 27, 2013). "How the NSA Is Still Harvesting Your Online Data – Files Show Vast Scale of Current NSA Metadata Programs, with One Stream Alone Celebrating 'One Trillion Records Processed'". The Guardian. Archived from the original on August 4, 2013. Retrieved August 5, 2013.CS1 maint: multiple names: authors list (link)
- Layne, Ken (June 18, 2013). "Job Networking Site LinkedIn Filled With Secret NSA Program Names". Archived from the original on December 8, 2017. Retrieved August 6, 2013.
- "xkeyscorerules100". Panorama. ARD (broadcaster). July 3, 2014. Archived from the original on July 7, 2014. Retrieved July 4, 2014.
- Jacob Appelbaum, A. Gibson, J. Goetz, V. Kabisch, L. Kampf, L. Ryge (July 3, 2014). "NSA targets the privacy-conscious". Panorama. Norddeutscher Rundfunk. Archived from the original on July 3, 2014. Retrieved July 4, 2014.CS1 maint: multiple names: authors list (link)
- Nakashima, Ellen (July 31, 2013). "Newly Declassified Documents on Phone Records Program Released". The Washington Post. Archived from the original on March 23, 2014. Retrieved August 6, 2013.
- Fisher, Max (August 1, 2013). "Is XKeyscore Still Active? Defense Contractor Posted a Job Listing for it 2 weeks Ago". WorldViews, blog of The Washington Post. Retrieved August 6, 2013.
- Rea, Kari (July 28, 2013). "Glenn Greenwald: Low-Level NSA Analysts Have 'Powerful and Invasive' Search Tool". ABC News. Archived from the original on July 30, 2013. Retrieved August 4, 2013.
- Wills, Amanda (August 1, 2013). "New Snowden Leak: NSA Program Taps All You Do Online". Mashable (via CNN). Archived from the original on August 4, 2013. Retrieved August 4, 2013.
- NSA Press Statement on 30 July 2013 Archived August 1, 2013, at the Wayback Machine
- Staff (July 31, 2013). "XKeyscore Presentation from 2008 – Read in Full". The Guardian. Archived from the original on August 1, 2013. Retrieved August 6, 2013.
- "Snowden Interview Transcript". Norddeutscher Rundfunk. n.d. Archived from the original on January 28, 2014. Retrieved January 27, 2014.
- Lee, Micah; Greenwald, Glenn; Marquis-Boire, Morgan (July 2, 2015). "A Look at the Inner Workings of NSA's XKEYSCORE". The Intercept. Retrieved July 2, 2020.
- Staff (c. 2013). "No alvo dos EUA – O big-brother na América Latina e no mundo" [The U.S. Targets – Big Brother in Latin America and in the World]. O Globo (in Portuguese). Archived from the original on July 12, 2013. Retrieved August 5, 2013.
- Dorling, Philip (July 8, 2013). "Snowden Reveals Australia's Links to US Spy Web". The Sydney Morning Herald. Archived from the original on August 2, 2013. Retrieved August 2, 2013.
- Greenwald, Glenn; Casado, Roberto Kaz e José (July 6, 2013). "EUA expandem o aparato de vigilância continuamente – Software de vigilância usa mais de 700 servidores espalhados pelo mundo". O Globo (in Portuguese). Archived from the original on July 10, 2013. Retrieved August 2, 2013.CS1 maint: multiple names: authors list (link)
- Ambinder, Marc (July 31, 2013). "What's XKEYSCORE?". The Compass (blog of The Week). Archived from the original on January 30, 2014. Retrieved August 4, 2013.
- Gunnar Rensfeldt. "Read the Snowden Documents From the NSA". Sveriges Television. Archived from the original on February 9, 2014. Retrieved December 21, 2013.
- See also: 3 slides about the XKeyscore program Archived February 2, 2014, at the Wayback Machine
- Greenwald, Glenn (July 31, 2013)."XKeyscore: NSA tool collects 'nearly everything a user does on the internet' – XKeyscore Gives 'Widest-Reaching' Collection of Online Data – NSA Analysts Require No Prior Authorization for Searches – Sweeps Up Emails, Social Media Activity and Browsing History" Archived December 31, 2013, at the Wayback Machine. The Guardian. Retrieved August 1, 2013.
- XKeyscoreTabs XKS Development Archived June 30, 2014, at the Wayback Machine, published by Der Spiegel on June 18, 2014
- Der Spiegel: GCHQ report on the technical abilities of the powerful spying program TEMPORA, which allows for a "full take" Archived June 5, 2019, at the Wayback Machine
- Gallagher, Sean (August 1, 2013). "NSA's Internet Taps Can Find Systems to Hack, Track VPNs and Word Docs – X-Keyscore Gives NSA the Ability to Find and Exploit Vulnerable Systems". Ars Technica. Archived from the original on August 4, 2013. Retrieved August 4, 2013.
- Greenwald, Glenn; Casado, Roberto Kaz e José (July 13, 2013). "Espionagem dos EUA se espalhou pela América Latina – Depois do Brasil, Colômbia foi o país mais vigiado – Venezuela também entrou na mira de programas americanos" [U.S. Spying Spread Through Latin America – After Brazil, Colombia Was the Country's Most Watched – Venezuela Also Came in the Crosshairs of U.S. Programs]. O Globo (in Portuguese). Archived from the original on July 15, 2013. Retrieved August 5, 2013.CS1 maint: multiple names: authors list (link)
- Kyle Rankin (July 3, 2014). "NSA: Linux Journal is an "extremist forum" and its readers get flagged for extra surveillance". Archived from the original on July 3, 2014. Retrieved July 3, 2014.
- Laura Poitras, Marcel Rosenbach and Holger Stark, Ally and Target: US Intelligence Watches Germany Closely Archived August 20, 2013, at the Wayback Machine, August 12, 2013.
- Staff (July 20, 2013). "'Prolific Partner': German Intelligence Used NSA Spy Program" Archived July 21, 2013, at the Wayback Machine. Der Spiegel. Retrieved August 5, 2013.
- Top Level Telecommunications, New slides about NSA collection programs Archived July 26, 2013, at the Wayback Machine, July 16, 2013
- "Cold War treaty confirms Sweden was not neutral". The Local. Archived from the original on December 11, 2013. Retrieved December 12, 2013.
- Gunnar Rensfeldt. "Read the Snowden Documents From the NSA". Sveriges Television. Archived from the original on February 9, 2014. Retrieved December 12, 2013.
- Ryan Gallagher (April 24, 2017). "Japan made secret deals with the NSA that expanded global surveillance". Archived from the original on April 24, 2017. Retrieved April 24, 2017.
External links
| Wikimedia Commons has media related to XKeyscore. |
- A full NSA presentation about XKeyscore from 2008
- Building a panopticon: The evolution of the NSA’s XKeyscore
- Marquis-Boire, Morgan; Greenwald, Glenn; Lee, Micah (July 1, 2015). "XKEYSCORE: NSA's Google for the World's Private Communications". The Intercept. Retrieved July 5, 2015.
- Lee, Micah; Greenwald, Glenn; Marquis-Boire, Morgan (July 2, 2015). "Behind the Curtain; A Look at the Inner Workings of NSA's XKEYSCORE". The Intercept. Retrieved July 5, 2015.