NSA ANT catalog
The NSA ANT catalog is a 50-page classified document listing technology available to the United States National Security Agency (NSA) Tailored Access Operations (TAO) by the Advanced Network Technology (ANT) Division to aid in cyber surveillance. Most devices are described as already operational and available to US nationals and members of the Five Eyes alliance. According to Der Spiegel, which released the catalog to the public on December 30, 2013, "The list reads like a mail-order catalog, one from which other NSA employees can order technologies from the ANT division for tapping their targets' data."[1][2][3][4][5][6][7][8][9] The document was created in 2008.[10]
Security researcher Jacob Appelbaum gave a speech at the Chaos Communications Congress in Hamburg, Germany, in which he detailed techniques that the simultaneously published Der Spiegel article he coauthored indicate the NSA uses in its surveillance efforts in the US and internationally.[6][11]
The prices of the items in the catalog range from free (typically for software) to US$250,000.[1]
Background
In 2013, Der Spiegel published an article, co-written by Jacob Appelbaum, Judith Horchert and Christian Stöcker, that exposed the NSA "toolbox". Their source of the document was not disclosed. While it came from one of the news agencies in possession of documents leaked by former NSA contractor Edward Snowden,[12] security expert Bruce Schneier said he doesn't "believe the TAO catalog came from the Snowden documents. I think there's a second leaker out there."[12][13]
Exploits described in the document are mostly targeted at devices manufactured by US companies, including Apple,[14] Cisco, Dell, Juniper Networks, Maxtor, Seagate, and Western Digital, although there is nothing in the document that suggests that the companies were complicit.[1][15] After Der Spiegel revealed that NSA has the ability to inject software onto iPhones using an ANT product called DROPOUTJEEP, Apple issued a statement denying any prior knowledge of the NSA spyware and stated that they would take steps to protect their customers from security attacks "regardless of who's behind them".[16] Cisco has mustered their Cisco Product Security Incident Response Team (PSIRT) to investigate the hack vulnerability.[17]
Capabilities list
The NSA ANT document contains codeword references to hardware and software surveillance technology available to the NSA.[18]
- BULLDOZER: Technology that creates a hidden wireless bridge allowing NSA personnel to remotely control a system wirelessly.[15][19]
- CANDYGRAM: A $40,000 tripwire device that emulates a GSM cellphone tower.
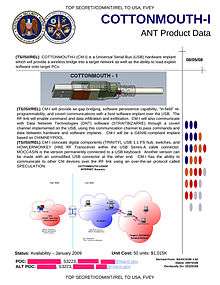 COTTONMOUTH-I
COTTONMOUTH-I - COTTONMOUTH: (see image at right) A family of modified USB and Ethernet connectors that can be used to install Trojan horse software and work as wireless bridges, providing covert remote access to the target machine.[20] COTTONMOUTH-I is a USB plug that uses TRINITY as digital core and HOWLERMONKEY as RF transceiver. Cost in 2008 was slightly above $1M for 50 units.
- COTTONMOUTH-II is deployed in a USB socket (rather than plug), and costs only $200K per 50 units, but requires further integration in the target machine to turn into a deployed system.
- COTTONMOUTH-III is a stacked Ethernet and USB plug costing approximately $1.25M for 50 units.
- CROSSBEAM is "a GSM communications module capable of collecting and compressing voice data" [21]
- CTX4000: Continuous wave radar device that can ""illuminate" a target system for recovery of "off net" information.[22]
- CYCLONE-HX9 - GSM Base Station Router
- DEITYBOUNCE: Technology that installs a backdoor software implant on Dell PowerEdge servers via the motherboard BIOS and RAID controller(s).[23][24]
- DROPOUTJEEP: "A software implant for the Apple iPhone that utilizes modular mission applications to provide specific SIGINT functionality. This functionality includes the ability to remotely push/pull files from the device. SMS retrieval, contact list retrieval, voicemail, geolocation, hot mic, camera capture, cell tower location, etc. Command, control and data exfiltration can occur over SMS messaging or a GPRS data connection. All communications with the implant will be covert and encrypted."[8]
- EBSR is a "tri-band active GSM base station with internal 802.11/GPS/handset capability" [25]
- ENTOURAGE
- FEEDTROUGH: Software that can penetrate Juniper Networks firewalls allowing other NSA-deployed software to be installed on mainframe computers.[1][9][26]
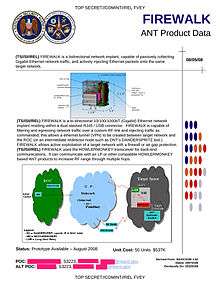 FIREWALK
FIREWALK - FIREWALK: (see image at right) A device that looks identical to a standard RJ45 socket that allows data to be injected, or monitored and transmitted via radio technology.[27] using the HOWLERMONKEY RF transceiver. It can for instance create a VPN to the target computer. Cost in 2008: $537K for 50 units.
- FOXACID: Technology that can install spyware using a "quantum insert" capable of infecting spyware at a packet level. (Not numbered because FOXACID may or may not be part of the NSA ANT catalog; sources differ.)
- GENESIS
- GINSU: Technology that uses a PCI bus device in a computer, and can reinstall itself upon system boot-up.[28]
- GOPHERSET: GSM software that uses a phone's SIM card's API (SIM Toolkit or STK) to control the phone through remotely sent commands.[29]
- GOURMETTROUGH: User-configurable persistence implant for certain Juniper Networks firewalls.[22]
- HALLUXWATER: Back door exploit for Huawei Eudemon firewalls.[22]
- HEADWATER: Persistent backdoor technology that can install spyware using a "quantum insert" capable of infecting spyware at a packet level on Huawei routers.[22]
 HOWLERMONKEY
HOWLERMONKEY - HOWLERMONKEY: (see image at right) A RF transceiver that makes it possible (in conjunction with digital processors and various implanting methods) to extract data from systems or allow them to be controlled remotely.
- IRATEMONK: Technology that can infiltrate the firmware of hard drives manufactured by Maxtor, Samsung, Seagate, and Western Digital.[30]
- IRONCHEF: Technology that can "infect" networks by installing itself in a computer I/O BIOS.[15] IRONCHEF includes also "Straitbizarre" and "Unitedrake" which have been linked to the spy software REGIN.[31]
- JUNIORMINT
- JETPLOW: Firmware that can be implanted to create a permanent backdoor in a Cisco PIX series and ASA firewalls.[22]
- LOUDAUTO: $30 audio-based RF retro-reflector listening device.[22]
 TRINITY
TRINITY - MAESTRO-II: a multi-chip module approximately the size of a dime that serves as the hardware core of several other products. The module contains a 66 MHz ARM7 processor, 4 MB of flash, 8 MB of RAM, and a FPGA with 500,000 gates. Unit cost: $3–4K (in 2008). It replaces the previous generation modules which were based on the HC12 microcontroller.
- MONKEYCALENDAR: Software that transmits a mobile phone's location by hidden text message.
- NEBULA
- NIGHTSTAND: Portable system that wirelessly installs Microsoft Windows exploits from a distance of up to eight miles.[22]
- NIGHTWATCH: Portable computer used to reconstruct and display video data from VAGRANT signals; used in conjunction with a radar source like the CTX4000 to illuminate the target in order to receive data from it.
- PICASSO: Software that can collect mobile phone location data, call metadata, access the phone's microphone to eavesdrop on nearby conversations.[29]
- PHOTOANGLO: A joint NSA/GCHQ project to develop a radar system to replace CTX4000.[22]
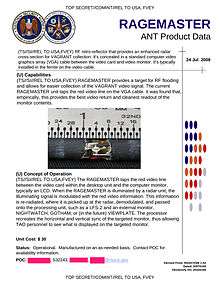
- RAGEMASTER: (see image above, right) A concealed $30 device that taps the video signal from a target's computer's VGA signal output so the NSA can see what is on a targeted desktop monitor. It is powered by a remote radar and responds by modulating the VGA red signal (which is also sent out most DVI ports) into the RF signal it re-radiates; this method of transmission is codenamed VAGRANT. RAGEMASTER is usually installed/concealed in the ferrite choke of the target cable. The original documents are dated 2008-07-24. Several receiver/demodulating devices are available, e.g. NIGHTWATCH.[6]
- SCHOOLMONTANA: Software that makes DNT implants persistent on JUNOS-based (FreeBSD-variant) J-series routers/firewalls.[22]
- SIERRAMONTANA: Software that makes DNT implants persistent on JUNOS-based M-series routers/firewalls.[22]
- STUCCOMONTANA: Software that makes DNT implants persistent on JUNOS-based T-series routers/firewalls.[22]
- SOMBERKNAVE: Software that can be implanted on a Windows XP system allowing it to be remotely controlled from NSA headquarters.
- SOUFFLETROUGH: BIOS injection software that can compromise Juniper Networks SSG300 and SSG500 series firewalls.[22]
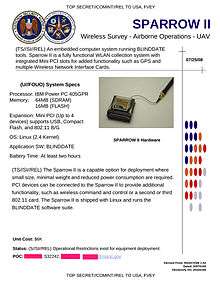 SPARROW II
SPARROW II - SPARROW II: (see image at right) A small computer intended to be used for WLAN collection, including from UAVs. Hardware: IBM Power PC 405GPR processor, 64 MB SDRAM, 16 MB of built-inflash, 4 mini PCI slots, CompactFlash slot, and 802.11 B/G hardware. Running Linux 2.4 and the BLINDDATE software suite. Unit price (2008): $6K.
- SURLYSPAWN: Keystroke monitor technology that can be used on remote computers that are not internet connected.
- SWAP: Technology that can reflash the BIOS of multiprocessor systems that run FreeBSD, Linux, Solaris, or Windows.
- TAWDRYYARD
- TOTECHASER
- TOTEGHOSTLY: Software that can be implanted on a Windows mobile phone allowing full remote control.
- TRINITY: (see image at right) A more recent and more powerful multi-chip module using a 180 MHz ARM9 processor, 4 MB of flash, 96 MB of SDRAM, and a FPGA with 1 million gates. Smaller than a penny. Estimated cost (2008) $625K for 100 units.
- WATERWITCH: A portable "finishing tool" that allows the operator to find the precise location of a nearby mobile phone.
- WISTFULTOLL
See also
- Computer and Internet Protocol Address Verifier (CIPAV) — FBI trojan
- Duqu — spyware worm
- Equation Group - a highly advanced secretive computer espionage group, suspected of being tied to the NSA
- FinFisher — private-sector trojan used by several states
- MiniPanzer and MegaPanzer — Swiss state-sponsored trojans
- R2D2 (trojan) — a German state-sponsored trojan
- TEMPEST — NSA standards for electromagnetic protection
- WARRIOR PRIDE — more recent (2010) NSA/GCHQ capabilities against smartphones
- Communications Assistance for Law Enforcement Act - CALEA
- Tempora
- NSA Playset
References
- Appelbaum, Jacob & Stöcker, Christian (December 29, 2013). "Shopping for Spy Gear: Catalog Advertises NSA Toolbox". Der Spiegel. Retrieved January 1, 2014.
- Hathaway, Jay (December 30, 2013). "The NSA has nearly complete backdoor access to Apple's iPhone". Daily Dot. Retrieved January 1, 2014.
- Condliffe, Jamie (December 31, 2013). "The NSA Has Crazy Good Backdoor Access to iPhones". Gizmodo. Retrieved January 1, 2014.
- Edwards, Jim (December 30, 2013). "DOCUMENTS: NSA Has 'A 100% Success Rate' Putting Spyware On iPhones". Business Insider. Retrieved January 1, 2014.
- "De l'interception de colis à l'espionnage de l'écran, inventaire des outils de la NSA". Le Monde. December 30, 2013. Retrieved January 1, 2014.
- Satter, Raphael (December 30, 2013). "Privacy Advocate Exposes NSA Spy Gear at Gathering". ABC News. Archived from the original on 2013-12-31. Retrieved January 1, 2014.
- Hardawar, Devindra (December 31, 2013). "The iPhone has reportedly been fully hacked by the NSA since 2008 (Update: Apple denies working with NSA)". Venture Beat. Retrieved January 1, 2014.
- Kain, Erik (December 30, 2013). "The NSA Reportedly Has Total Access To The Apple iPhone". Forbes. Retrieved January 1, 2014.
- Zetter, Kim (December 30, 2013). "NSA Hackers Get the 'Ungettable' With Rich Catalog of Custom Tools". Wired. Retrieved January 1, 2014.
- Lawler, Richard (December 31, 2013). "Leaked documents detail 2008 NSA program to hack and remote control iPhones". Engadget. Retrieved January 1, 2014.
- Mick, Jason (December 31, 2013). "Tax and Spy: How the NSA Can Hack Any American, Stores Data 15 Years". Daily Tech. Archived from the original on August 24, 2014. Retrieved January 1, 2014.
- Kirk, Jeremy (December 30, 2013). "The NSA intercepts computer deliveries to plant spyware". Computerworld. ISSN 0010-4841. Archived from the original on January 1, 2014. Retrieved 9 September 2014.
- Stiennon, Richard. "Is There A Second NSA Leaker?".
- Campbell, Mickey (December 30, 2013). "NSA worked on iPhone spyware to remotely monitor users, leaked documents show". Apple Insider. Retrieved January 1, 2014.
- Gallagher, Sean (December 31, 2013). "Your USB cable, the spy: Inside the NSA's catalog of surveillance magic". Ars Technica. Retrieved January 1, 2014.
- Hughes, Neil (December 31, 2013). "Apple says it was unaware of NSA's iPhone spying, vows to defend customers' privacy". Apple Insider. Retrieved January 1, 2014.
- Brandon, Russell (December 30, 2013). "The NSA's elite hackers can hijack your Wi-Fi from 8 miles away". The Verge. Retrieved January 1, 2014.
- Elmer-DeWitt, Philip (December 31, 2013). "Apple, Jacob Appelbaum and the National Security Agency". Fortune. Retrieved January 1, 2014.
- GINSU NSA ANT catalog page: File:NSA_GINSU.jpg (not publicly known to have its own page in the catalog)
- Hesseldahl, Arik (December 30, 2013). "You Won't Believe All the Crazy Hardware the NSA Uses for Spying". All Things Digital. Retrieved January 1, 2014.
- Schneier, Bruce (2014-02-21). "CROSSBEAM: NSA Exploit of the Day". Retrieved 2015-02-01.
- "NSA's ANT Division Catalog of Exploits for Nearly Every Major Software/Hardware/Firmware". LeakSource. December 30, 2013. Retrieved January 2, 2014.
- Darmawan Salihun. "NSA BIOS Backdoor a.k.a. God Mode Malware Part 1: DEITYBOUNCE" January 29th, 2014.
- DEITYBOUNCE NSA ANT catalog page: File:NSA DEITYBOUNCE.jpg
- Schneier, Bruce (2014-02-25). "EBSR: NSA Exploit of the Day". Retrieved 2015-02-01.
- Whitwam, Ryan (December 30, 2013). "The NSA regularly intercepts laptop shipments to implant malware, report says". Extreme Tech. Retrieved January 1, 2014.
- Thomson, Iain (December 31, 2013). "How the NSA hacks PCs, phones, routers, hard disks 'at speed of light': Spy tech catalog leaks". The Register. Retrieved January 1, 2014.
- GINSU NSA ANT catalog page: File:NSA_GINSU.jpg
- Estes, Adam Clark (December 31, 2013). "A Peek Inside The NSA's Spy Gear Catalogue". Gizmodo Australia. Retrieved January 1, 2014.
- Meyer, David (December 29, 2013). "NSA's backdoor catalog exposed: Targets include Juniper, Cisco, Samsung, Huawei". Gigaom. Retrieved January 1, 2014.
- Stöcker, Christian; Rosenbach, Marcel (25 November 2014). "Trojaner Regin ist ein Werkzeug von NSA und GCHQ". Spiegel Online (in German). Retrieved 2 February 2015.
| Wikimedia Commons has media related to NSA ANT. |