Radical 6
Radical 6 meaning "hook" is one of six of the 214 Kangxi radicals that are composed of only one stroke.
| 亅 | ||
|---|---|---|
| ||
| 亅 (U+4E85) "hook" | ||
| Pinyin: | jué | |
| Bopomofo: | ㄐㄩㄝˊ | |
| Wade–Giles: | chüeh2 | |
| Cantonese Yale: | kyut3 | |
| Jyutping: | kyut3 | |
| Pe̍h-ōe-jī: | koat | |
| Kana: | はねぼう hanebō | |
| Kanji: | 撥棒 hanebō | |
| Hangul: | 갈고리 galgori | |
| Sino-Korean: | 궐 gwol | |
| Stroke order animation | ||
 | ||
In the Kangxi Dictionary, there are 19 characters (out of 49,030) to be found under this radical.
Characters with Radical 6
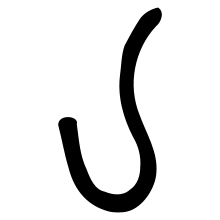
Small seal script character
| strokes | character |
|---|---|
| without additional strokes | 亅 |
| 1 additional stroke | 了 |
| 2 additional strokes | 亇 |
| 3 additional strokes | 予 |
| 5 additional strokes | 争 (Simplified Chinese only) |
| 6 additional strokes | 爭 |
| 7 additional strokes | 亊 (Korean Hanja only) |
| 8 additional strokes | 事 |
Literature
- Fazzioli, Edoardo (1987). Chinese calligraphy : from pictograph to ideogram : the history of 214 essential Chinese/Japanese characters. calligraphy by Rebecca Hon Ko. New York: Abbeville Press. ISBN 0-89659-774-1.
- Leyi, Li (1993). Tracing the Roots of Chinese Characters: 500 Cases. Beijing. ISBN 978-7-5619-0204-2.
gollark: I just think it is *not good* if it's working for someone else, generally seems actively hostile for user control, and also seems to slowly be trying to move to a subscription model.
gollark: Arch is somewhat annoying to set up, but it's probably paid back the time investment by teaching me Linux skills and not arbitrarily wasting my time for Microsoft.
gollark: You shouldn't have to work around it. OSes should let you actually use them and work for you, not for some company.
gollark: Well, it does. Because you have to put effort into that nonsense in the first place and it may break later.
gollark: Yes. You can in theory work around the nonsense it does, but all you can do is work around it.
This article is issued from Wikipedia. The text is licensed under Creative Commons - Attribution - Sharealike. Additional terms may apply for the media files.