Clickjacking
Clickjacking (classified as a User Interface redress attack, UI redress attack, UI redressing) is a malicious technique of tricking a user into clicking on something different from what the user perceives, thus potentially revealing confidential information or allowing others to take control of their computer while clicking on seemingly innocuous objects, including web pages.[1][2][3][4]
Clickjacking is an instance of the confused deputy problem, wherein a computer is innocently fooled into misusing its authority.[5]
History
In 2002, it had been noted that it was possible to load a transparent layer over a web page and have the user's input affect the transparent layer without the user noticing. However, this was mainly ignored as a major issue until 2008.[6]
In 2008, Jeremiah Grossman and Robert Hansen had discovered that Adobe Flash Player was able to be clickjacked, allowing an attacker to gain access of the computer without the user's knowledge.[6]
The term "clickjacking" was coined by Jeremiah Grossman and Robert Hansen,[7][8] a portmanteau of the words "click" and "hijacking." [6]
As more attacks of a similar nature were discovered, the focus of the term "UI redressing" was changed to describe the category of these attacks, rather than just clickjacking itself.[6]
Description
Clickjacking takes advantage of vulnerabilities that are present in applications and web pages to allow the attacker to manipulate the user's computer.
For example, a clickjacked page tricks a user into performing undesired actions by clicking on a concealed link. On a clickjacked page, the attackers load another page over it in a transparent layer. The unsuspecting users think that they are clicking visible buttons, while they are actually performing actions on the invisible page. The hidden page may be an authentic page; therefore, the attackers can trick users into performing actions which the users never intended. There is no way of tracing such actions to the attackers later, as the users would have been genuinely authenticated on the hidden page.
Clickjacking is not limited to this type though, and are present in other forms.
Clickjacking categories
- Classic: works mostly through a web browser[6]
- Likejacking: utilizes Facebook's social media capabilities[9][10]
- Nested: clickjacking tailored to affect Google+[11]
- Cursorjacking: manipulates the cursor's appearance and location[6]
- MouseJacking: inject keyboard or mouse input via remote RF link[12]
- Browserless: does not use a browser[6]
- Cookiejacking: acquires cookies from browsers[6][13]
- Filejacking: capable of setting up the affected device as a file server[6][14]
- Password manager attack: clickjacking that utilizes a vulnerability in the autofill capability of browsers[15]
Classic
Classic clickjacking refers to when an attacker uses hidden layers on web pages to manipulate the actions a user's cursor does, resulting in the user being misled about what truly is being clicked on.
A user might receive an email with a link to a video about a news item, but another webpage, say a product page on Amazon, can be "hidden" on top or underneath the "PLAY" button of the news video. The user tries to "play" the video but actually "buys" the product from Amazon. The hacker can only send a single click, so they rely on the fact that the visitor is both logged into Amazon.com and has 1-click ordering enabled.
While technical implementation of these attacks may be challenging due to cross-browser incompatibilities, a number of tools such as BeEF or Metasploit Project offer almost fully automated exploitation of clients on vulnerable websites. Clickjacking may be facilitated by - or may facilitate - other web attacks, such as XSS.[16][17]
Likejacking
Likejacking is a malicious technique of tricking users of a website into "liking" a Facebook page that they did not intentionally mean to "like".[18] The term "likejacking" came from a comment posted by Corey Ballou in the article How to "Like" Anything on the Web (Safely),[19] which is one of the first documented postings explaining the possibility of malicious activity regarding Facebook's "like" button.[20]
According to an article in IEEE Spectrum, a solution to likejacking was developed at one of Facebook's hackathons.[21] A "Like" bookmarklet is available that avoids the possibility of likejacking present in the Facebook like button.[22]
Nested
Nested clickjacking, compared to classic clickjacking, works by embedding a malicious web frame between two frames of the original, harmless web page: that from the framed page and that which is displayed on the top window. This works due to a vulnerability in the HTTP header X-Frame-Options, in which, when this element has the value SAMEORIGIN, the web browser only checks the two aforementioned layers. The fact that additional frames can be added in between these two while remaining undetected means that attackers can use this for their benefit.
In the past, with Google+ and the faulty version of X-Frame-Options, attackers were able to insert frames of their choice by using the vulnerability present in Google's Image Search engine. In between the image display frames, which were present in Google+ as well, these attacker-controlled frames were able to load and not be restricted, allowing for the attackers to mislead whoever came upon the image display page.[11]
Cursorjacking
Cursorjacking is a UI redressing technique to change the cursor from the location the user perceives, discovered in 2010 by Eddy Bordi, a researcher at Vulnerability.fr,[23] Marcus Niemietz demonstrated this with a custom cursor icon, and in 2012 Mario Heiderich by hiding the cursor.[24][25]
Jordi Chancel, a researcher at Alternativ-Testing.fr, discovered a cursorjacking vulnerability using Flash, HTML and JavaScript code in Mozilla Firefox on Mac OS X systems (fixed in Firefox 30.0) which can lead to arbitrary code execution and webcam spying.[26]
A second CursorJacking vulnerability was again discovered by Jordi Chancel in Mozilla Firefox on Mac OS X systems (fixed in Firefox 37.0) using once again Flash, HTML and JavaScript code which can lead also to the spying of the webcam and the execution of a malicious addon allowing the execution of a malware on the computer of the trapped user.[27]
MouseJacking
Different form other clickjacking techniques that redress a UI, MouseJacking is a wireless hardware based UI vulnerability first reported by Marc Newlin of Bastille in 2016 which allows external keyboard input to be injected into vulnerable dongles.[28] Logitech supplied firmware patches but other manufacturers failed to respond.[29]
Browserless
In browserless clickjacking, attackers utilize vulnerabilities in programs to replicate classic clickjacking in them, without being required to use the presence of a web browser.
This method of clickjacking is mainly prevalent among mobile devices, usually on Android devices, especially due to the way in which toast notifications work. Because toast notifications have a small delay in between the moment the notification is requested and the moment the notification actually displays on-screen, attackers are capable of using that gap to create a dummy button that lies hidden underneath the notification and can still be clicked on.[6]
Cookiejacking
Cookiejacking is a form of clickjacking in which cookies are stolen from web browsers. This is done by tricking the user into dragging an object which seemingly appears harmless, but is in fact making the user select the entire content of the cookie being targeted. From there, the attacker can acquire the cookie and all of the data that is within it.[13]
Filejacking
In filejacking, attackers use the web browser's capability to navigate through the computer and access computer files in order to acquire personal data. It does so by tricking the user into establishing an active file server (through the file and folder selection window that browsers use). With this, attackers can now access and take files from their victims' computers.[14]
Password manager attack
A 2014 paper from researcher at the Carnegie Mellon University found that while browsers refuse to autofill if the protocol on the current login page is different from the protocol at the time the password was saved, some password managers would insecurely fill in passwords for the http version of https-saved passwords. Most managers did not protect against iFrame- and redirection-based attacks and exposed additional passwords where password synchronization had been used between multiple devices.[15]
Prevention
Client-side
NoScript
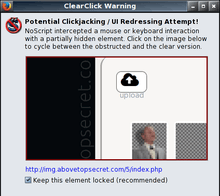
Protection against clickjacking (including likejacking) can be added to Mozilla Firefox desktop and mobile[30] versions by installing the NoScript add-on: its ClearClick feature, released on 8 October 2008, prevents users from clicking on invisible or "redressed" page elements of embedded documents or applets.[31] According to Google's "Browser Security Handbook" from year 2008, NoScript's ClearClick is a "freely available product that offers a reasonable degree of protection" against Clickjacking.[32] Protection from the newer cursorjacking attack was added to NoScript 2.2.8 RC1.[24]
NoClickjack
The "NoClickjack" web browser add-on (browser extension) adds client-side clickjack protection for users of Google Chrome, Mozilla Firefox, Opera and Microsoft Edge without interfering with the operation of legitimate iFrames. NoClickjack is based on technology developed for GuardedID. NoClickjack add-on is free.
GuardedID
GuardedID (a commercial product) includes client-side clickjack protection for users of Internet Explorer without interfering with the operation of legitimate iFrames.[33] GuardedID clickjack protection forces all frames to become visible. GuardedID teams with web browser add-on "NoClickjack" to add protection for Google Chrome, Mozilla Firefox, Opera and Microsoft Edge.
Gazelle
Gazelle is a Microsoft Research project secure web browser based on IE, that uses an OS-like security model, and has its own limited defenses against clickjacking.[34] In Gazelle, a window of different origin may only draw dynamic content over another window's screen space if the content it draws is opaque.
Intersection Observer v2
The Intersection Observer v2 API[35] introduces the concept of tracking the actual "visibility" of a target element as a human being would define it.[36] This allows a framed widget to detect when it's being covered. The feature is enabled by default since Google Chrome 74, released in April 2019.[37] Chrome is the only browser to implement the API at this time.
Server-side
Framekiller
Web site owners can protect their users against UI redressing (frame based clickjacking) on the server side by including a framekiller JavaScript snippet in those pages they do not want to be included inside frames from different sources.[32]
Such JavaScript-based protection, unfortunately, is not always reliable. This is especially true on Internet Explorer,[32] where this kind of countermeasure can be circumvented "by design" by including the targeted page inside an <IFRAME SECURITY=restricted> element.[38]
X-Frame-Options
Introduced in 2009 in Internet Explorer 8 was a new HTTP header X-Frame-Options which offered a partial protection against clickjacking[39][40] and was shortly after adopted by other browsers (Safari,[41] Firefox,[42] Chrome,[43] and Opera[44]). The header, when set by website owner, declares its preferred framing policy: values of DENY, ALLOW-FROM origin, or SAMEORIGIN will prevent any framing, framing by external sites, or allow framing only by the specified site, respectively. In addition to that, some advertising sites return a non-standard ALLOWALL value with the intention to allow framing their content on any page (equivalent of not setting X-Frame-Options at all).
In 2013 the X-Frame-Options header has been officially published as RFC 7034,[45] but is not an internet standard. The document is provided for informational purposes only. The W3C's Content Security Policy Level 2 Recommendation provides an alternative security directive, frame-ancestors, which is intended to obsolete the X-Frame-Options header.[46]
A security header like X-Frame-Options will not protect users against clickjacking attacks that are not using a frame.[47]
Content Security Policy
The frame-ancestors directive of Content Security Policy (introduced in version 1.1) can allow or disallow embedding of content by potentially hostile pages using iframe, object, etc. This directive obsoletes the X-Frame-Options directive. If a page is served with both headers, the frame-ancestors policy should be preferred by the browser.[48]—although some popular browsers disobey this requirement.[49]
Example frame-ancestors policies:
# Disallow embedding. All iframes etc. will be blank, or contain a browser specific error page. Content-Security-Policy: frame-ancestors 'none' # Allow embedding of own content only. Content-Security-Policy: frame-ancestors 'self' # Allow specific origins to embed this content Content-Security-Policy: frame-ancestors www.example.com www.wikipedia.org
See also
References
- Robert McMillan (17 September 2008). "At Adobe's request, hackers nix 'clickjacking' talk". PC World. Archived from the original on 17 July 2015. Retrieved 8 October 2008.
- Megha Dhawan (29 September 2008). "Beware, clickjackers on the prowl". India Times. Retrieved 8 October 2008.
- Dan Goodin (7 October 2008). "Net game turns PC into undercover surveillance zombie". The Register. Retrieved 8 October 2008.
- Fredrick Lane (8 October 2008). "Web Surfers Face Dangerous New Threat: 'Clickjacking'". newsfactor.com. Archived from the original on 13 October 2008. Retrieved 8 October 2008.
- The Confused Deputy rides again!, Tyler Close, October 2008
- Niemietz, Marcus (2012). "UI Redressing Attacks on Android Devices" (PDF). Black Hat.
- You don't know (click)jack Robert Lemos, October 2008
- JAstine, Berry. "Facebook Help Number 1-888-996-3777". Retrieved 7 June 2016.
- "Viral clickjacking 'Like' worm hits Facebook users". Naked Security. 31 May 2010. Retrieved 23 October 2018.
- "Facebook Worm – "Likejacking"". Naked Security. 31 May 2010. Retrieved 23 October 2018.
- Lekies, Sebastian (2012). "On the fragility and limitations of current Browser-provided Clickjacking protection schemes" (PDF). USENIX.
- "Wireless Mouse Hacks & Network Security Protection". MOUSEJACK. Retrieved 3 January 2020.
- Valotta, Rosario (2011). "Cookiejacking". tentacoloViola - sites.google.com. Retrieved 23 October 2018.
- "Filejacking: How to make a file server from your browser (with HTML5 of course)". blog.kotowicz.net. Retrieved 23 October 2018.
- "Password Managers: Attacks and Defenses" (PDF). Retrieved 26 July 2015.
- "The Clickjacking meets XSS: a state of art". Exploit DB. 26 December 2008. Retrieved 31 March 2015.
- Krzysztof Kotowicz. "Exploiting the unexploitable XSS with clickjacking". Retrieved 31 March 2015.
- Cohen, Richard (31 May 2010). "Facebook Work - "Likejacking"". Sophos. Archived from the original on 4 June 2010. Retrieved 5 June 2010.
- Ballou, Corey (2 June 2010). ""Likejacking" Term Catches On". jqueryin.com. Archived from the original on 5 June 2010. Retrieved 8 June 2010.
- Perez, Sarah (2 June 2010). ""Likejacking" Takes Off on Facebook". ReadWriteWeb. Archived from the original on 16 August 2011. Retrieved 5 June 2010.
- Kushner, David (June 2011). "Facebook Philosophy: Move Fast and Break Things". spectrum.ieee.org. Retrieved 15 July 2011.
- Perez, Sarah (23 April 2010). "How to "Like" Anything on the Web (Safely)". ReadWriteWeb. Retrieved 24 August 2011.
- Podlipensky, Paul. "Cursor Spoofing and Cursorjacking". Podlipensky.com. Paul Podlipensky. Archived from the original on 22 November 2017. Retrieved 22 November 2017.
- Krzysztof Kotowicz (18 January 2012). "Cursorjacking Again". Retrieved 31 January 2012.
- Aspect Security. "Cursor-jacking attack could result in application security breaches". Retrieved 31 January 2012.
- "Mozilla Foundation Security Advisory 2014-50". Mozilla. Retrieved 17 August 2014.
- "Mozilla Foundation Security Advisory 2015-35". Mozilla. Retrieved 25 October 2015.
- "What is MouseJack!". Bastille. Retrieved 3 January 2020.
- "CERT VU#981271 Multiple wireless keyboard/mouse devices use an unsafe proprietary wireless protocol". www.kb.cert.org. Retrieved 3 January 2020.
- Giorgio Maone (24 June 2011). "NoScript Anywhere". hackademix.net. Retrieved 30 June 2011.
- Giorgio Maone (8 October 2008). "Hello ClearClick, Goodbye Clickjacking". hackademix.net. Retrieved 27 October 2008.
- Michal Zalevski (10 December 2008). "Browser Security Handbook, Part 2, UI Redressing". Google Inc. Retrieved 27 October 2008.
- Robert Hansen (4 February 2009). "Clickjacking and GuardedID ha.ckers.org web application security lab". Archived from the original on 11 July 2012. Retrieved 30 November 2011.
- Wang, Helen J.; Grier, Chris; Moschchuk, Alexander; King, Samuel T.; Choudhury, Piali; Venter, Herman (August 2009). "The Multi-Principal OS Construction of the Gazelle Web Browser" (PDF). 18th Usenix Security Symposium, Montreal, Canada. Retrieved 26 January 2010.
- "Intersection Observer - W3C Editor's Draft".
- "Trust is Good, Observation is Better".
- "De-anonymization via Clickjacking in 2019".
- Giorgio Maone (27 October 2008). "Hey IE8, I Can Has Some Clickjacking Protection". hackademix.net. Retrieved 27 October 2008.
- Eric Lawrence (27 January 2009). "IE8 Security Part VII: ClickJacking Defenses". Retrieved 30 December 2010.
- Eric Lawrence (30 March 2010). "Combating ClickJacking With X-Frame-Options". Retrieved 30 December 2010.
- Ryan Naraine (8 June 2009). "Apple Safari jumbo patch: 50+ vulnerabilities fixed". Retrieved 10 June 2009.
- https://developer.mozilla.org/en/The_X-FRAME-OPTIONS_response_header The X-Frame-Options response header — MDC
- Adam Barth (26 January 2010). "Security in Depth: New Security Features". Retrieved 26 January 2010.
- "Web specifications support in Opera Presto 2.6". 12 October 2010. Archived from the original on 14 January 2012. Retrieved 22 January 2012.
- "HTTP Header Field X-Frame-Options". IETF. 2013.
- "Content Security Policy Level 2". W3C. 2016.
- "lcamtuf's blog: X-Frame-Options, or solving the wrong problem".
- "Content Security Policy Level 2". w3.org. 2 July 2014. Retrieved 29 January 2015.
- "Clickjacking Defense Cheat Sheet". Retrieved 15 January 2016.