Carding (fraud)
Carding is a term describing the trafficking of credit card, bank account and other personal information online.[1] Activities also encompass procurement of details,[2] and money laundering techniques.[3] Modern carding sites have been described as full-service commercial entities.[4] Since it is not a crime that is committed online, carding is not a form of crime and often intertwined with other types of e-fencing.
 Carding refers not only to payment card based fraud, but also to a range of related activities and services. |
|
Forums
|
Acquisition
There are a great many of methods to acquire credit card and associated financial and personal data. The earliest known carding methods have also included 'trashing' for financial data, raiding mail boxes and working with insiders.[5][6] Some bank card numbers can be semi-automatically generated based on known sequences via a 'BIN attack'.[7] Carders might attempt a 'distributed guessing attack' to discover valid numbers by submitting numbers across a high number of ecommerce sites simultaneously.[8]
Today, various methodologies include skimmers at ATMs, hacking or web skimming an ecommerce or payment processing site or even intercepting card data within a point of sale network.[9] Randomly calling hotel room phones asking guests to 'confirm' credit card details is example of a social engineering attack vector.[10]
Resale
Stolen data may be bundled as a 'Base' or 'First-hand base' if the seller participated in the theft themselves. Resellers may buy 'packs' of dumps from multiple sources. Ultimately, the data may be sold on darknet markets and other carding sites and forums[11] specialising in these types of illegal goods.[12][13] Teenagers have gotten involved in fraud such as using card details to order pizzas.[14]
On the more sophisticated of such sites, individual 'dumps' may be purchased by zip code and country so as to avoid alerting banks about their misuse.[15] Automatic checker services perform validation en masse in order to quickly check if a card has yet to be blocked. Sellers will advertise their dump's 'valid rate', based on estimates or checker data. Cards with a greater than 90% valid rate command higher prices. 'Cobs' or changes of billing are highly valued, where sufficient information is captured to allow redirection of the registered card's billing and shipping addresses to one under the carder's control.[16]
Full identity information may be sold as 'Fullz' inclusive of social security number, date of birth and address to perform more lucrative identity theft.[17][18]
Fraudulent vendors are referred to as 'rippers', vendors who take buyer's money then never deliver. This is increasingly mitigated via forum and store based feedback systems as well as through strict site invitation and referral policies.[19]
Whilst some Carding Forums will exist only on the dark web, today most exist on the internet, and many will use the Cloudflare network protection service.[20][21][22]
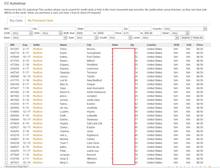
Estimated per card prices, in US$, for stolen payment card data 2015[23]
| Payment Card Number With CVV2 | United States | United Kingdom | Canada | Australia | European Union |
|---|---|---|---|---|---|
| Software-generated | $5–8 | $20–$25 | $20–$25 | $21–$25 | $25–$30 |
| With Bank ID Number | $15 | $25 | $25 | $25 | $30 |
| With Date of Birth | $15 | $30 | $30 | $30 | $35 |
| With Fullzinfo | $30 | $35 | $40 | $40 | $45 |
Cash out
Funds from stolen cards themselves may be cashed out via buying pre-paid cards, gift cards or through reshipping goods through mules then e-fencing through online marketplaces like eBay.[24][25] Increased law enforcement scrutiny over reshipping services has led to the rise of dedicated criminal operations for reshipping stolen goods.[26][3]
Hacked computers may be configured with SOCKS proxy software to optimise acceptance from payment processors.[27][28][29][30]
Money laundering
The 2004 investigation into the ShadowCrew forum also led to investigations of the online payment service E-gold that had been launched in 1996, one of the preferred money transfer systems of carders at the time. In December 2005 its owner Douglas Jackson's house and businesses were raided as a part of 'Operation Goldwire'. Jackson discovered that the service had become a bank and transfer system to the criminal underworld. Pressured to disclose ongoing records disclosed to law enforcement, many arrests were made through to 2007. However, in April 2007 Jackson himself was indicted for money laundering, conspiracy and operating an unlicensed money transmitting business. This led to the service freezing the assets of users in 'high risk' countries and coming under more traditional financial regulation.[31]
Since 2006, Liberty Reserve had become a popular service for cybercriminals. When it was seized in May 2013 by the US government, this caused a major disruption to the cybercrime ecosystem.[32]
Today, some carders prefer to make payment between themselves with bitcoin,[33][34] as well as traditional wire services such as Western Union, MoneyGram or the Russian WebMoney service.[35][36]
Related services
Many forums also provide related computer crime services such as phishing kits, malware and spam lists.[37] They may also act as a distribution point for the latest fraud tutorials either for free or commercially.[38] ICQ was at one point the instant messenger of choice due to its anonymity as well as MSN clients modified to use PGP.[39] Carding related sites may be hosted on botnet based fast flux web hosting for resilience against law enforcement action.[40]
Other account types like PayPal,[41] Uber,[42] Netflix and loyalty card points may be sold alongside card details.[43] Logins to many sites may also be sold as a backdoor access apparently for major institutions such as banks, universities and even industrial control systems.[23]
For gift card fraud, retailers are prone to be exploited by fraudsters in their attempts to steal gift cards via bot technology or through stolen credit card information.[44] In the context of carding fraud, using stolen credit card data to purchase gift cards is becoming an increasingly common money laundering tactic. Another way gift card fraud occurs is when a retailer's online systems which store gift card data undergo brute force attacks from automated bots.
Tax refund fraud is an increasingly popular method of using identify theft to acquire prepaid cards ready for immediate cash out.[3][45] Popular coupons may be counterfeited and sold also.[46]
Personal information and even medical records are sometimes available.[23] Theft and gift card fraud may operated entirely independently of online carding operations.[47]
Cashing out in gift cards is very common as well, as "discounted gift cards" can be found for sale anywhere, making it an easy sale for a carder, and a very lucrative operation.[48]
The Google hacks popularly known as Google dorks for credit card details[49] are also used vastly in getting credit card details
History
1980s–1999
Since the 1980s[50] in the days of the dial-up BBSes, the term carding has been used to describe the practices surrounding credit card fraud. Methods such as 'trashing', raiding mail boxes and working with insiders at stores were cited as effective ways of acquiring card details. Use of drops at places like abandoned houses and apartments or with persuadable neighbors near such a location were suggested. Social engineering of mail order sales representatives are suggested in order to provide passable information for card not present transactions.[6] Characters such as 'The Video Vindicator' would write extensive guides on 'Carding Across America', burglary, fax fraud, supporting phreaking,[51] and advanced techniques for maximizing profits.[52] During the 1980s, the majority of hacker arrests were attributable to carding-related activities due to the relative maturity of financial laws compared to emerging computer regulations.[50]
Started in 1989, by 1990 Operation Sundevil was launched by the United States Secret Service to crack down on use of BBS groups involved in credit card fraud and other illegal computer activities, the most highly publicised action by the US federal government against hackers at the time.[53] The severity of the crack down was so much that the Electronic Frontier Foundation was formed in response to the violation of civil liberties.[54]
In the mid-1990s with the rise of AOL dial-up accounts, the AOHell software became a popular tool for phishing and stealing information such as credit card details from new Internet users.[55] Such abuse was exacerbated because prior to 1995 AOL did not validate subscription credit card numbers on account creation.[56] Abuse was so common AOL added "no one working at AOL will ask for your password or billing information" to all instant messenger communications. Only by 1997 when warez and phishing were pushed off the service did these types of attacks begin to decline.[56]
December 1999 featured an unusual case of extortion when Maxim, a Russian 19-year-old, stole the 25,000 users' card details from CD Universe and demanded $100,000 for its destruction. When the ransom was not paid, the information was leaked on the Internet.[57]
One of the first books written about carding, 100% Internet Credit Card Fraud Protected, featured content produced by 'Hawk' of carding group 'Universal Carders'. It described the spring 1999 hack and credit card theft on CyberCash, the stratification of carder proficiencies (script kiddie through to professionals) common purchases for each type and basic phishing schemes to acquire credit card data.[58]
By 1999, United States offline and online credit card fraud annual losses were estimated at between $500,000 and $2 million.[58]
2000–2006
From the early 2000s, sites like 'The Counterfeit Library', also functioning as a diploma mill, grew to prominence, with many of its members going on to join larger cybercrime websites in later years until its closure around September 2004.[39]
In 2001, Russian speaking hackers founded CarderPlanet in Odessa which would go on to be one of the most notorious forums of its kind.[59]
In the summer of 2003, separate US secret service and FBI investigations led to the arrest the top administrator Albert Gonzalez of the large ShadowCrew, turned informant as a part of 'Operation Firewall'. By March 2004, the administrator of 'CarderPlanet' disappeared with Gonzalez taking over. In October 2004 dozens of ShadowCrew members were busted across the US and Canada. Carder's speculate that one of the USSS infiltrators might have been detected by a fellow site member causing the operation to be expedited.[39] Ultimately, the closure of ShadowCrew and CarderPlanet did not reduce the degree of fraud and led to the proliferation of smaller sites.[60][61]
ShadowCrew admin Brett Shannon Johnson managed to avoid being arrested at this time, but was picked up in 2005 on separate charges then turned informant. Continuing to commit tax fraud as an informant, 'Operation Anglerphish' embedded him as admins on both ScandinavianCarding and CardersMarket. When his continued carding activities were exposed as a part of a separate investigation in 2006, he briefly went on the run before being caught for good in August of that year.[62]
In June 2005, the credit card processing company CardSystems was hacked in what was at the time the largest personal information breach in history with many of the stolen information making its way to carding sites.[16] Later in 2007, the TJX Companies breach perpetuated by Albert Gonzalez (who was still an informant at the time)[63] would only come to the public's attention after stolen cards detected being misused to buy large amounts of gift cards.[64] Gonzalez's 2008, intrusion into Heartland Payment Systems to steal card data was characterized as the largest ever criminal breach of card data.[65]
Also in June 2005, UK-based carders were found to be collaborating with Russian mafia and arrested as a result of a National Hi-Tech Crime Unit investigation, looking into Eastern European crime syndicates.[39][66] Some time in 2005, J. Keith Mularski from the NCFTA headed up a sting into popular English language site DarkMarket.ws. One of the few survivors of 'Operation Firewall', Mularski was able to infiltrate the site via taking over the handle 'Master Splyntr', an Eastern European spammer named Pavel Kaminski. In late 2006 the site was hacked by Max Butler, who detected user 'Master Splyntr' had logged in from the NCFTA's offices, but the warning was dismissed as inter-forum rivalry. In 2007 details of the operation was revealed to German national police, that the NCFTA had successfully penetrated the forum's inner 'family'. By October 4, 2007 Mularski announced he was shutting the site due to unwanted attention from a fellow administrator, framed as 'too much attention' from law enforcement.[67] For several years following site closure multiple arrests were made internationally.[68]
From 2004 through to 2006, CardersMarket assimilated various rival forums through marketing, hacking databases.[69] Arrested in 2007, in 2010 the site's owner Max Butler was sentenced to 13 years in prison.[70]
2007–present
Since 2007 to present, Operation Open Market, an operation run by the HIS and the USSS has targeted the primarily Russian language Carder.su organisation, believed to be operating out of Las Vegas.[71] In 2011, alleged site owner Roman Seleznev was apprehended in the Maldives by US law enforcement[72][73] and in 2012, identity thief David Ray Camez was arrested and charged in an unprecedented use of RICO legislation.[74][75]
Horohorin Vladislav, identified as BadB in November 2009 in a sealed indictment from the United States attorney's office was arrested in 2010 by USSS in Nice, France. Vladislav created first fully automated credit card shop and managed websites associates with stolen credit card numbers.[76][77][78] Horohorin Vladislav is also known for being first cyber criminal to promote his illegal activities by creating video cartoons ridiculing American card holders.[79]
In 2011, former Bulgarian ShadowCrew member Aleksi Kolarov (also known as 'APK') was finally arrested and held in Paraguay before being extradited to the United States in 2013 to face charges.[80]
In June 2012, the FBI seized carding and hacking forums UGNazi.com and Carders.org in a sting as a part of a 2-year investigation dubbed Operation Card Shop[1] after setting up a honeypot forum at carderprofit.cc.[81]
In August 2013, hacker and carding forum HackBB was taken down as part of the raid on Freedom Hosting.[82]
In January 2014, fakeplastic.net was closed following an investigation by the US postal service and FBI, after collating previously seized information from TorMail, ShadowCrew and Liberty Reserve. This led to multiple arrests and prosecutions as well as the site's closure.[83][84][85]
A 2014 report from Group-IB, suggested that Russian cybercriminals could be making as much as $680 million a year based on their market research.[86]
In December 2014, the Tor based Tor Carding Forum closed following a site hack, with its administrator 'Verto' directing users to migrate to the Evolution darknet market's[87] forums[88] which would go on to be the largest darknet market exit scam ever seen.[89][90]
'Alpha02', who was notorious for his carding guides, went on to found the AlphaBay darknet market,[91] the first to ever deal in stolen Uber accounts.[92] The site is working on rebuilding the damage to the reputation of markets founded by carders precipitated by the Evolution scam.[93] Meanwhile, most Russian carders selling details do not trust the darknet markets due to the high level of law enforcement attention; however, buyers are more open.[94]
Ercan Findikoğlu, also known as "Segate" and "Predator", with others, led an international conspiracy,[95] stole $55 million by hacking ATM card issuers and making fraudulent cards and was sentenced to eight years in prison by a federal court.[96][97][98][99][100][101][102][103][104][105][106][107][108][109][110][111][112][113][107][114][115][116][117][118][119]
Findikoğlu, a Turkish national, with a Russian wife, Alena Kovalenko, avoided capture by obscuring his cyber fingerprints and avoiding the reach of American law, but he went to Germany in December 2013, was arrested, lost a court challenge, and was extradited. Findikoğlu, as a youngster honed his skills in cyber cafes, the Turkish military, and then masterminded three complex, global financial crimes by hacking into credit card processors, eliminating the limits on prepaid cards then sending PINs and access codes to teams of cashers who, within hours withdrew cash from ATMs. In December 2012, 5,000 cashers in 20 countries withdrew $5 million, $400,000 in 700 transactions from 140 New York ATMs, in 150 minutes. Stolen cash was kicked back via wire transfers and deliveries to Turkey, Romania and Ukraine.[120]
Vladimir Drinkman, 34, a cohort of Albert Gonzalez,[121] pleaded guilty in Camden, New Jersey, that he got credit card numbers from Heartland Payment Systems, 7-Eleven, Hannaford Bros, Nasdaq, Carrefour, JetBlue,[122][123] and other companies from 2005 to 2012. (U.S. v. Drinkman, 09-cr-00626, U.S. District Court, District of New Jersey (Camden))[124][125][126][127][128][129][130][122][131][132][133][134][135][136][137][138][139][140][141][142][143]
In February 2018, the Infraud Organization was revealed.
This site, run by a user named "Prince" was found to be a total scam https://altenens.org. Upon payment with Bitcoin the user's accounts are deleted and the money is stolen.[144]
Contemporary situation
In more recent years, Russian language forums have gained dominance over English language ones, with the former considerably more adept at identifying security researchers and counterintelligence activities[145] and strict invitation systems.[2] Russia's lack of extradition treaty with the United States has made the country somewhat of a safe haven of cyber criminals, with the Russian foreign ministry going so far as to recommend citizens not travel abroad to countries with such treaties.[146] Investigative journalist Brian Krebs has extensively reported on Russian carders as an ongoing game of cat and mouse.[147]
References
- J. Schwartz, Mathew (27 June 2012). "FBI Busts Massive International Carding Ring". Archived from the original on 27 September 2015. Retrieved 11 August 2015.
- DeepDotWeb (18 March 2015). "Evolution Market Background: Carding Forums, Ponzi Schemes & LE". Archived from the original on 27 September 2015. Retrieved 27 August 2015.
- Krebs, Brian (4 August 2014). "'White Label' Money Laundering Services". Retrieved 23 August 2015.
- van Hardeveld, Gert Jan (26 October 2015). "Stolen TalkTalk customer details: time bombs that may tick a while before being triggered". Retrieved 19 December 2015.
- Zetter, Kim (19 December 2013). "Target Admits Massive Credit Card Breach; 40 Million Affected". Retrieved 8 August 2015.
- Wizzard, Black. "The Art of Carding". textfiles.com. Retrieved 13 August 2015.
- "Credit Card Bin Attack Fraud". Retrieved 12 November 2015.
- Reporters, Telegraph (2 December 2016). "Hacked in just six seconds: How criminals only need moments to guess card number and security code". Retrieved 2 December 2016.
- Ilascu, Ionut (11 August 2014). "Russian Point-of-Sale Hacker Pleads Not Guilty in US Court". Retrieved 14 September 2015.
- Weisbaum, Herb. "Summer travel alert: Scammer target hotel guests". Retrieved 20 September 2015.
- Shah, Khushbu (9 April 2015). "Meet the Man Crusading Against Restaurant Credit Card Hackers". Retrieved 31 August 2015.
- Krebs, Brian (4 June 2014). "Peek Inside a Professional Carding Shop". Retrieved 8 August 2015.
- DeepDotWeb (20 May 2015). "AlphaBay Market Launched a Fully-Automated Stolen Credit Card Shop". Archived from the original on 8 November 2016. Retrieved 23 October 2016.
- Wilson, Michael (2014-12-05). "Pizza Orders Reveal Credit Card Scheme, and a Secondhand Market". The New York Times. ISSN 0362-4331. Retrieved 2017-11-19.
- Montemayor, Stephen (2 August 2015). "Out-of-state criminals bring cloned credit card schemes to Twin Cities". Retrieved 2 August 2015.
- Zeller JR, Tom (21 June 2005). "Black Market in Stolen Credit Card Data Thrives on Internet". Retrieved 13 August 2015.
- Ducklin, Paul (5 November 2012). "Credit card fraud - want to join the party?". Retrieved 8 August 2015.
- Cox, Joseph (23 April 2015). "The Kalashnikov Carding Club". Retrieved 24 January 2017.
- Vijayan, Jaikumar (6 May 2015). "The identity underworld: How criminals sell your data on the Dark Web". Retrieved 16 August 2015.
- "Carders love CloudFlare". Archived from the original on 13 July 2014. Retrieved 2 August 2015.
- Yadron, Danny (29 September 2014). "CloudFlare Pushes More Encrypted Web". Retrieved 10 August 2015.
- Kovacs, Eduard (17 March 2014). "Underground Payment Card Store Rescator Hacked and Defaced". Retrieved 10 August 2015.
- "The Hidden Data Economy" (PDF). Retrieved 17 October 2015.
- Krebs, Brian (3 November 2015). "How Carders Can Use eBay as a Virtual ATM". Retrieved 5 November 2015.
- Westin, Ken (21 December 2013). "Stolen Target Credit Cards and the Black Market: How the Digital Underground Works". Retrieved 11 August 2015.
- Krebs, Brian (12 October 2011). "Shady Reshipping Centers Exposed, Part I". Retrieved 23 August 2015.
- "How to chain socks with Tor". Archived from the original on 2 February 2017. Retrieved 23 January 2017.
- Graham, James (2009-04-23). Cyber Fraud. p. 45. ISBN 9781420091281.
- Krebs, Brian (16 October 2016). "IoT Devices as Proxies for Cybercrime". Retrieved 23 January 2017.
- van Hardeveld, Gert Jan; Webber, Craig; O'Hara, Kieron. "Discovering credit card fraud methods in online tutorials". Retrieved 7 September 2017.
- Zetter, Kim (9 June 2009). "Bullion and Bandits: The Improbable Rise and Fall of E-Gold". Retrieved 13 August 2015.
- Halpern, Jake (May 2015). "Bank of the Underworld". Retrieved 16 August 2015.
- Kiell (11 December 2014). "A Carder's First Experience". Archived from the original on 18 April 2015. Retrieved 18 August 2015.
- Kujawa, Adam (24 January 2014). "FBI Takes Down Poorly Secured Carders". Retrieved 23 August 2015.
- PULKKINEN, LEVI (16 January 2015). "Piles of cash, bunches of bling and a public defender?". Retrieved 16 August 2015.
- Krebs, Brian (14 July 2014). "Feds Charge Carding Kingpin in Retail Hacks". Retrieved 16 August 2015.
- Leinwand Leger, Donna (19 October 2014). "How stolen credit cards are fenced on the Dark Web". Retrieved 8 August 2015.
- Jackson Higgins, Kelly (15 December 2014). "Price Tag Rises For Stolen Identities Sold In The Underground". Retrieved 17 August 2015.
- Allen, Hoffmann (5 January 2015). "Before DarkNetMarkets Were Mainstream". Archived from the original on 30 June 2015. Retrieved 16 August 2015.
- Peters, Sara (1 December 2016). "Avalanche Botnet Comes Tumbling Down In Largest-Ever Sinkholing Operation". Retrieved 1 December 2016.
- Krebs, Brian (October 5, 2011). "How Much is That Phished PayPal Account?". Retrieved 2 September 2015.
- Hackett, Robert (30 March 2015). "Stolen Uber user logins are for sale on the dark web: only $1 each". Retrieved 2 September 2015.
- Paganini, Pierluigi (15 May 2015). "Hacking communities in the Deep Web". Retrieved 13 September 2015.
- Raz, Inbar. "Six Ways Bots Will Attack E-Commerce Sites This Holiday Season". Retrieved 11 December 2017.
- Krebs, Brian (15 August 2015). "IRS: 330K Taxpayers Hit by 'Get Transcript' Scam". Retrieved 23 August 2015.
- Cox, Joseph (14 January 2016). "Dark Web Vendor Sentenced for Dealing Counterfeit Coupons". Retrieved 24 January 2016.
- "'Operation Plastic Paradise' nets 18 arrests in $2 million gift card scheme". WFTV. 14 December 2015. Retrieved 19 December 2015.
- "Gift Card Fraud: How It's Committed and Why It's So Lucrative". The State of Security. 2015-06-24. Retrieved 2017-11-19.
- "Google Dorks for getting credit card details (A list of google dorks.)". LATEST TECH NEWS. 2018-06-03. Retrieved 2018-08-03.
- "Credit Cards for fun and profit!". textfiles.com.
- "Hacking Calling Cards".
- "Textfile Writing Groups: The Video Vindicator". textfiles.com. Retrieved 13 August 2015.
- Sterling, Bruce (1994). "Part Three: Law and Order". The Hacker Crackdown: Law And Disorder On The Electronic Frontier. New York: Bantam Books. ISBN 0-553-56370-X. Retrieved 2009-03-08.
- Charles, Dan (1990-07-21). "Crackdown on hackers 'may violate civil rights'". New Scientist. Retrieved 2009-03-08.
- Langberg, Mike (8 September 1995). "AOL ACTS TO THWART HACKERS". Retrieved 13 August 2015.
- "Phishing: General Information". Retrieved 13 August 2015.
- Markoff, John (10 January 2000). "Thief Reveals Credit Card Data When Web Extortion Plot Fails". Retrieved 16 August 2015.
- Vesper (2000). 100% Internet Credit Card Fraud Protected. ISBN 1552125343. Retrieved 16 August 2015.
- Farivar, Cyrus (12 December 2013). "Ukrainian fraudster and CarderPlanet "Don" finally sentenced to 18 years". Retrieved 16 August 2015.
- Zetter, Kim (1 February 2007). "Crime Boards Come Crashing Down". Retrieved 11 August 2015.
- Zetter, Kim (1 July 2013). "9 Years After Shadowcrew, Feds Get Their Hands on Fugitive Cybercrook". Retrieved 11 August 2015.
- Zetter, Kim (6 June 2007). "Secret Service Operative Moonlights as Identity Thief". Retrieved 16 August 2015.
- Zetter, Kim. "4 Years After TJX Hack, Payment Industry Sets Security Standards". wired.com. Retrieved 21 May 2017.
- Hines, Matt (21 March 2007). "Stolen TJX data used in Florida crime spree".
- King, Rachael (6 July 2009). "Lessons from the Data Breach at Heartland". Retrieved 8 June 2014.
- "Phishing pair jailed for ID fraud". 29 June 2005. Retrieved 16 August 2015.
- Poulsen, Ken (13 October 2008). "Cybercrime Supersite 'DarkMarket' Was FBI Sting, Documents Confirm". Retrieved 13 August 2015.
- Davies, Caroline (14 January 2010). "Welcome to DarkMarket – global one-stop shop for cybercrime and banking fraud". Retrieved 13 August 2015.
- Acohido, Byron (11 October 2006). "Cybercrime flourishes in online hacker forums". Retrieved 11 August 2015.
- Poulsen, Kevin (12 February 2010). "Record 13-Year Sentence for Hacker Max Vision". Retrieved 11 August 2015.
- "Federal Authorities Arrest 19 Persons in Operation "Open Market"". 16 March 2012. Retrieved 8 August 2015.
- Krebs, Brian (8 July 2014). "Feds Charge Carding Kingpin in Retail Hacks". Retrieved 16 August 2015.
- Chiacu, Doina (8 July 2014). "Moscow accuses United States of 'kidnapping' Russian hacker". Retrieved 16 August 2015.
- "US cyber-thief gets 20-year jail term". 19 May 2014. Retrieved 16 August 2015.
- J. Schwartz, Mathew (12 December 2013). "Cybercrime Milestone: Guilty Verdict In RICO Case". Retrieved 16 August 2015.
- Staff, By the CNN Wire. "Alleged credit card trafficker arrested in France - CNN.com". Retrieved 2017-10-26.
- "Alleged global credit card fraud kingpin arrested in France". Christian Science Monitor. 2010-08-11. ISSN 0882-7729. Retrieved 2017-10-26.
- "One of 'world's most wanted cyber-criminals' arrested". 2010-08-12. ISSN 0307-1235. Retrieved 2017-10-26.
- TheNiggerHacker (2012-07-13), Russian Hackers - BadB Promotional Cartoon, retrieved 2017-10-26
- Zetter, Kim (1 July 2013). "9 Years After Shadowcrew, Feds Get Their Hands on Fugitive Cybercrook". Retrieved 16 August 2015.
- Krebs, Brian (26 June 2012). "'Carderprofit' Forum Sting Nets 26 Arrests". Retrieved 11 August 2015.
- Neal, Meghan (5 August 2013). "To Bust a Giant Porn Ring, Did the FBI Crack the Dark Web?". Archived from the original on 2015-08-23. Retrieved 2 August 2015.
- Kovacs, Eduard (25 January 2014). "Operators of Credit Card Counterfeiting Service Fakeplastic.net Charged". Retrieved 25 November 2015.
- "Mastermind of Online Counterfeit Card Retail Shop Pleads Guilty". FBI. 25 September 2014. Retrieved 25 November 2015.
- Krebs, Brian (14 January 2015). "Feds Infiltrate, Bust Counterfeit Card Shop". Retrieved 25 November 2015.
- E Dunn, John (16 October 2014). "Russian cybercriminals made $680 million from stolen credit cards". Retrieved 16 August 2015.
- Wired Staff (1 January 2015). "The Most Dangerous People on the Internet Right Now". Retrieved 1 August 2015.
- Farivar, Cyrus (19 December 2014). "After Silk Road takedowns, Dark Web drug sites still thriving". Retrieved 1 August 2015.
- Krebs, Brian (2015-03-18). "Dark Web's 'Evolution Market' Vanishes". Krebs on Security. Retrieved 2015-03-18.
- DeepDotWeb (10 May 2014). "Evolution Marketplace Staff Speak: We are growing fast!". Archived from the original on 8 October 2015. Retrieved 16 August 2015.
- Cox, Joseph (23 April 2015). "The Kalashnikov Carding Club". Retrieved 16 August 2015.
- "Stolen Uber Customer Accounts Are for Sale on the Dark Web for $1". Motherboard.
- G, Joshua (20 April 2015). "Interview With AlphaBay Market Admin". Archived from the original on 29 April 2015. Retrieved 18 August 2015.
- G, Joshua (11 April 2015). "Darknetmarkets And Their Reputation in The Russian Community". Archived from the original on 1 October 2015. Retrieved 27 August 2015.
- https://www.justice.gov/opa/file/482256/download
- "Turkish hacker gets 8 years in $55M ATM milking scheme - Cyberscoop". cyberscoop.com. 10 February 2017. Retrieved 21 May 2017.
- "German court blocks US extradition for "number two" hacker". sophos.com. 4 December 2014. Retrieved 21 May 2017.
- "25 members of $15 million carding gang arrested in Romania". sophos.com. 28 April 2015. Retrieved 21 May 2017.
- "The US will get a chance to try a hacker who allegedly helped steal millions from payment processors". businessinsider.com. Retrieved 21 May 2017.
- "Suspected mastermind behind mass ATM heist spree finally extradited to US". sophos.com. 25 June 2015. Retrieved 21 May 2017.
- "Turkish man stole more than $55 million from ATMs worldwide". cbsnews.com. Retrieved 21 May 2017.
- "Turkish hacker behind cyber heists gets 8 years in U.S. prison". 11 February 2017. Retrieved 21 May 2017 – via Reuters.
- "Ercan Segate Findikoglu — Krebs on Security". krebsonsecurity.com. Retrieved 21 May 2017.
- "Ercan Findikoglu". aljazeera.net. Retrieved 21 May 2017.
- "Sentencing of hacker in $55M scam is a rare win for feds (Update)". phys.org. Retrieved 21 May 2017.
- "Most-Wanted Cybercriminal Extradited to U.S. From Germany". 23 June 2015. Retrieved 21 May 2017 – via www.bloomberg.com.
- "Statement By Secretary Jeh C. Johnson Concerning The Extradition And Arraignment Of Ercan Findikoglu - Homeland Security". www.dhs.gov. Retrieved 21 May 2017.
- "Cybercrime - DOJ Update". www.dojupdate.com. Retrieved 21 May 2017.
- "Transnational Cyber Crime - Homeland Security". www.dhs.gov. Retrieved 21 May 2017.
- "How the U.S. Finally Tracked Down a Hacker Kingpin". 24 June 2015. Retrieved 21 May 2017 – via www.bloomberg.com.
- Germany, SPIEGEL ONLINE, Hamburg. "Cyberbankraub: Meisterhacker in die USA ausgeliefert - SPIEGEL ONLINE - Netzwelt". SPIEGEL ONLINE. Retrieved 21 May 2017.
- "Alleged Mastermind of Global Cybercrime Campaigns Extradited to the United States to Face Charges". www.justice.gov. Retrieved 21 May 2017.
- Grandoni, Dino (24 June 2015). "Suspect in $55 Million A.T.M. Scheme Is Extradited to U.S." Retrieved 21 May 2017 – via NYTimes.com.
- "Homeland Security -". edit-preview.dhs.gov. Archived from the original on 7 November 2017. Retrieved 21 May 2017.
- "ATM hacker who took $55M worldwide pleads guilty in Brooklyn". nydailynews.com. Retrieved 21 May 2017.
- DK (2 May 2017). The Crime Book: Big Ideas Simply Explained. Penguin. ISBN 9781465466549. Retrieved 21 May 2017 – via Google Books.
- "US bank hacker faces long jail term". 3 March 2016. Retrieved 21 May 2017 – via www.bbc.com.
- "Türk Hacker Ercan Fındıklıoğlu, ABD'ye İade Edildi". haberler.com. Retrieved 21 May 2017.
- "'Unlimited Operations': A New Financial Cyber Threat" (PDF). dorlaw.com. Archived from the original (PDF) on 4 August 2016. Retrieved 21 May 2017.
- "Foreign hacker gets 8 years in $55M US scam case". apnews.com. Retrieved 21 May 2017.
- "Russian Hacker Who Hit Heartland, NASDAQ, Extradited To US". darkreading.com. Retrieved 21 May 2017.
- http://krebsonsecurity.com/wp-content/uploads/2013/07/DVKRK-Indictment.pdf
- "Hackers hit Nasdaq, 7-Eleven, others for $300 million: feds". nydailynews.com. Retrieved 21 May 2017.
- "Russian National Admits Role in Largest Known Data Breach Conspiracy Ever Prosecuted". www.justice.gov. Retrieved 21 May 2017.
- "Russian Hacker Drinkman Pleads Guilty in Largest Data Breach". 15 September 2015. Retrieved 21 May 2017 – via www.bloomberg.com.
- "For alleged Russian hacker, a visit to Amsterdam is a costly trip". Washington Post. Retrieved 21 May 2017.
- "Russian hacker behind massive data breach pleads guilty". Engadget. Retrieved 21 May 2017.
- eva.ignatuschtschenko. "US v Drinkman, Kalinin, Kotov, Rytikov, Smilianets". www.unodc.org. Retrieved 21 May 2017.
- "Vladimir Drinkman — Krebs on Security". krebsonsecurity.com. Retrieved 21 May 2017.
- "Russian National Charged in Largest Known Data Breach Prosecution Extradited to United States". www.justice.gov. Retrieved 21 May 2017.
- France-Presse, Agence (27 January 2015). "Court rules accused Russian credit card 'megahacker' can be extradited to the US". Retrieved 21 May 2017 – via The Guardian.
- "Zoeken - NRC". www.nrc.nl. Retrieved 21 May 2017.
- "Russian Alleged Hacker Talks About Fighting U.S. Extradition". 15 January 2015. Retrieved 21 May 2017 – via www.bloomberg.com.
- "Accused Russian Hacker Drinkman Pleads Not Guilty in U.S." 17 February 2015. Retrieved 21 May 2017 – via www.bloomberg.com.
- Sengupta, Nathaniel Popper and Somini. "U.S. Says Ring Stole 160 Million Credit Card Numbers". nytimes.com. Retrieved 21 May 2017.
- "Biggest U.S. hacking case is tale of gamers' interrupted vacation". theglobeandmail.com. Retrieved 21 May 2017.
- reports, Tribune wire. "Dutch judge approves hacking suspect's extradition to U.S." chicagotribune.com. Retrieved 21 May 2017.
- "U.S. agents 'got lucky' pursuing accused Russia master hackers". 26 July 2017. Retrieved 21 May 2017 – via Reuters.
- "Russian Foreign Ministry will do everything to have Vladimir Drinkman return home soon". tass.com. Retrieved 21 May 2017.
- "Russian side receives no notification from US that Vladimir Drinkman arrives in the US". tass.com. Retrieved 21 May 2017.
- Miller, Roger LeRoy (5 December 2016). Business Law: Text & Cases - The First Course - Summarized Case Edition. Cengage Learning. ISBN 9781337514453. Retrieved 21 May 2017 – via Google Books.
- Zetter, Kim. "Feds Identify the Young Russians Behind the Top U.S. Cyber Thefts in Last 7 Years". wired.com. Retrieved 21 May 2017.
- "5 Cyberthieves Charged In Biggest US Hacking Case - Law360". www.law360.com. Retrieved 21 May 2017.
- Howard, Rick (2009-04-23). Cyber Fraud: Tactics, Techniques and Procedures. p. 117. ISBN 978-1420091274.
- Poulsen, Kevin (4 September 2013). "Russia gives travel advice to its hackers: don't leave the motherland". Archived from the original on 14 September 2015. Retrieved 16 August 2015.
- Clements, Sam (8 August 2013). "Cyber Criminals Hate Brian Krebs So Much They're Sending Heroin and SWAT Teams to His Home". Retrieved 16 August 2015.
Further reading
- Poulsen, Kevin (2011). Kingpin: The true story of Max Butler, the master hacker who ran a billion dollar cyber crime network. ISBN 978-0733628382. Retrieved 16 August 2015.
- Glenny, Misha (2 October 2012). DarkMarket: How Hackers Became the New Mafia. ISBN 9780307476449.