I've been preparing for a CISSP exam and was reading about applied cryptography in regard to email.
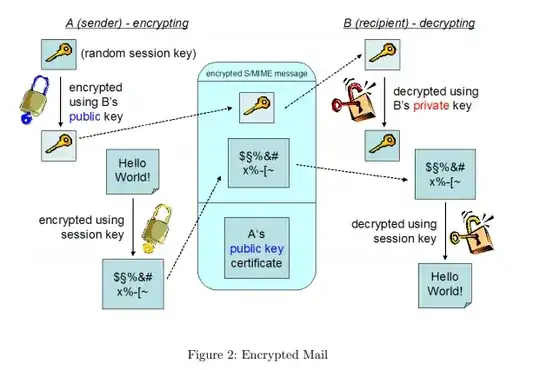
It's my understanding that the popular schemes (PGP,S/Mime) use a combination of asymmetric and symmetric cryptography. If I'm reading things correctly, in S/MIME, the message is encrypted using a sender generated symmetric key. In turn, the symmetric key is encrypted using the receiver's public key.
If the receiver changed their private key, they would no longer be able to decrypt the message. However, I was wondering if it was possible to recover the symmetric key from when the email was previously opened?
My guess would be that the email client does not intentionally store the key since that would present a security risk. Just wanted to see if that actually occurs or if there's something I'm missing.