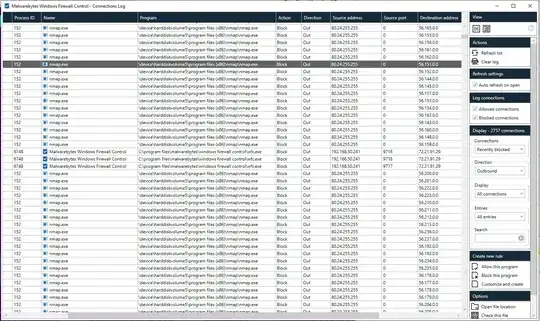
10 minutes after installing Nmap on a fresh install of windows, NMap loaded on its own and attempted to scan dozens of IP addresses around the globe. I never initiated the scan. Notice the source address is different than my own IP 192.168.50.241. How is this possible? Is this a feature in NMap? Packet generator? Virtual address injected into my hyper-visor through AMD PSP?
Asked
Active
Viewed 131 times
0
-
1is it installed as a service or bundled in another software ? – elsadek Feb 11 '20 at 08:00
-
1Where exactly did you obtain nmap from? – Feb 11 '20 at 10:06
-
nmap.com; Npcap was already installed with wireshark and when I did install nmap it said "networx is using "nmap" or "npcap" (probably the latter) please close before installing," something to that effect. It was a copy of Networx which is a bandwidth monitor that had an invalid signature. "2020 6.2.7.20016 repack by KpoJIuK". You can download it for testing if you like. Networx does not use or install npcap however, so I suspect this program may have been backdoored. With networx still installed, a few hrs later Nmap started scanning. How can the source address be different than my own? – Tyler Feb 12 '20 at 10:20
-
I guess the nmap loopback device could have had its own ip set to 80.24.255.255? – Tyler Feb 12 '20 at 15:54
1 Answers
0
The answer is that nmap has this functionality built in, I just noticed the folliwng:
Source option: "use decoy to hide identiy" code: -D
Send fake decoy probes from spoofed addresses to hide your own address. Give a list of addresses separated by commas. Use RND for a random address and ME to set the position of your address.
Tyler
- 417
- 5
- 12
-
2This would still require you to have used Nmap with the `-D` or `-S` option. Nmap will not "load on its own" so did you start this scan yourself? – bonsaiviking Feb 12 '20 at 16:33
-