Radio-frequency identification
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID tag consists of a tiny radio transponder; a radio receiver and transmitter. When triggered by an electromagnetic interrogation pulse from a nearby RFID reader device, the tag transmits digital data, usually an identifying inventory number, back to the reader. This number can be used to inventory goods. There are two types. Passive tags are powered by energy from the RFID reader's interrogating radio waves. Active tags are powered by a battery and thus can be read at a greater range from the RFID reader; up to hundreds of meters. Unlike a barcode, the tag doesn't need to be within the line of sight of the reader, so it may be embedded in the tracked object. RFID is one method of automatic identification and data capture (AIDC).[1]
RFID tags are used in many industries. For example, an RFID tag attached to an automobile during production can be used to track its progress through the assembly line; RFID-tagged pharmaceuticals can be tracked through warehouses; and implanting RFID microchips in livestock and pets enables positive identification of animals.
Since RFID tags can be attached to cash, clothing, and possessions, or implanted in animals and people, the possibility of reading personally-linked information without consent has raised serious privacy concerns.[2] These concerns resulted in standard specifications development addressing privacy and security issues. ISO/IEC 18000 and ISO/IEC 29167 use on-chip cryptography methods for untraceability, tag and reader authentication, and over-the-air privacy. ISO/IEC 20248 specifies a digital signature data structure for RFID and barcodes providing data, source and read method authenticity. This work is done within ISO/IEC JTC 1/SC 31 Automatic identification and data capture techniques. Tags can also be used in shops to expedite checkout, and to prevent theft by customers and employees.
In 2014, the world RFID market was worth US$8.89 billion, up from US$7.77 billion in 2013 and US$6.96 billion in 2012. This figure includes tags, readers, and software/services for RFID cards, labels, fobs, and all other form factors. The market value is expected to rise from $12.08bn in 2020 to US$16.23 billion by 2029.[3]
History

In 1945, Léon Theremin invented a listening device for the Soviet Union which retransmitted incident radio waves with the added audio information. Sound waves vibrated a diaphragm which slightly altered the shape of the resonator, which modulated the reflected radio frequency. Even though this device was a covert listening device, rather than an identification tag, it is considered to be a predecessor of RFID because it was passive, being energized and activated by waves from an outside source.[4]
Similar technology, such as the Identification friend or foe transponder, was routinely used by the allies and Germany in World War II to identify aircraft as friend or foe. Transponders are still used by most powered aircraft. An early work exploring RFID is the landmark 1948 paper by Harry Stockman,[5] who predicted that "... considerable research and development work has to be done before the remaining basic problems in reflected-power communication are solved, and before the field of useful applications is explored."
Mario Cardullo's device, patented on January 23, 1973, was the first true ancestor of modern RFID,[6] as it was a passive radio transponder with memory.[7] The initial device was passive, powered by the interrogating signal, and was demonstrated in 1971 to the New York Port Authority and other potential users. It consisted of a transponder with 16 bit memory for use as a toll device. The basic Cardullo patent covers the use of RF, sound and light as transmission carriers. The original business plan presented to investors in 1969 showed uses in transportation (automotive vehicle identification, automatic toll system, electronic license plate, electronic manifest, vehicle routing, vehicle performance monitoring), banking (electronic checkbook, electronic credit card), security (personnel identification, automatic gates, surveillance) and medical (identification, patient history).[6]
In 1973, an early demonstration of reflected power (modulated backscatter) RFID tags, both passive and semi-passive, was performed by Steven Depp, Alfred Koelle and Robert Frayman at the Los Alamos National Laboratory.[8] The portable system operated at 915 MHz and used 12-bit tags. This technique is used by the majority of today's UHFID and microwave RFID tags.[9]
In 1983, the first patent to be associated with the abbreviation RFID was granted to Charles Walton.[10]
Design
A radio-frequency identification system uses tags, or labels attached to the objects to be identified. Two-way radio transmitter-receivers called interrogators or readers send a signal to the tag and read its response.[11]
Tags
RFID tags are made out of three pieces: a micro chip (an integrated circuit which stores and processes information and modulates and demodulates radio-frequency (RF) signals), an antenna for receiving and transmitting the signal and a substrate.[12] The tag information is stored in a non-volatile memory. The RFID tag includes either fixed or programmable logic for processing the transmission and sensor data, respectively.
RFID tags can be either passive, active or battery-assisted passive. An active tag has an on-board battery and periodically transmits its ID signal. A battery-assisted passive has a small battery on board and is activated when in the presence of an RFID reader. A passive tag is cheaper and smaller because it has no battery; instead, the tag uses the radio energy transmitted by the reader. However, to operate a passive tag, it must be illuminated with a power level roughly a thousand times stronger than an active tag for signal transmission. That makes a difference in interference and in exposure to radiation.
Tags may either be read-only, having a factory-assigned serial number that is used as a key into a database, or may be read/write, where object-specific data can be written into the tag by the system user. Field programmable tags may be write-once, read-multiple; "blank" tags may be written with an electronic product code by the user.
The RFID tag receives the message and then responds with its identification and other information. This may be only a unique tag serial number, or may be product-related information such as a stock number, lot or batch number, production date, or other specific information. Since tags have individual serial numbers, the RFID system design can discriminate among several tags that might be within the range of the RFID reader and read them simultaneously.
Readers
RFID systems can be classified by the type of tag and reader.
A Passive Reader Active Tag (PRAT) system has a passive reader which only receives radio signals from active tags (battery operated, transmit only). The reception range of a PRAT system reader can be adjusted from 1–2,000 feet (0–600 m)[13], allowing flexibility in applications such as asset protection and supervision.
An Active Reader Passive Tag (ARPT) system has an active reader, which transmits interrogator signals and also receives authentication replies from passive tags.
An Active Reader Active Tag (ARAT) system uses active tags awoken with an interrogator signal from the active reader. A variation of this system could also use a Battery-Assisted Passive (BAP) tag which acts like a passive tag but has a small battery to power the tag's return reporting signal.
Fixed readers are set up to create a specific interrogation zone which can be tightly controlled. This allows a highly defined reading area for when tags go in and out of the interrogation zone. Mobile readers may be handheld or mounted on carts or vehicles.
Frequencies
| Band | Regulations | Range | Data speed | ISO/IEC 18000 section | Remarks | Approximate tag cost in volume (2006) US $ |
|---|---|---|---|---|---|---|
| 120–150 kHz (LF) | Unregulated | 10 cm | Low | Part 2 | Animal identification, factory data collection | $1 |
| 13.56 MHz (HF) | ISM band worldwide | 10 cm–1 m | Low to moderate | Part 3 | Smart cards (ISO/IEC 15693, ISO/IEC 14443 A, B). ISO-non-compliant memory cards (Mifare Classic, iCLASS, Legic, Felica ...). ISO-compatible microprocessor cards (Desfire EV1, Seos) | $0.50 to $5 |
| 433 MHz (UHF) | Short range devices | 1–100 m | Moderate | Part 7 | Defense applications, with active tags | $5 |
| 865–868 MHz (Europe) 902–928 MHz (North America) UHF |
ISM band | 1–12 m | Moderate to high | Part 6 | EAN, various standards; used by railroads[16] | $0.15 (passive tags) |
| 2450–5800 MHz (microwave) | ISM band | 1–2 m | High | Part 4 | 802.11 WLAN, Bluetooth standards | $25 (active tags) |
| 3.1–10 GHz (microwave) | Ultra wide band | Up to 200 m | High | Not defined | Requires semi-active or active tags | $5 projected |
Signaling

Signaling between the reader and the tag is done in several different incompatible ways, depending on the frequency band used by the tag. Tags operating on LF and HF bands are, in terms of radio wavelength, very close to the reader antenna because they are only a small percentage of a wavelength away. In this near field region, the tag is closely coupled electrically with the transmitter in the reader. The tag can modulate the field produced by the reader by changing the electrical loading the tag represents. By switching between lower and higher relative loads, the tag produces a change that the reader can detect. At UHF and higher frequencies, the tag is more than one radio wavelength away from the reader, requiring a different approach. The tag can backscatter a signal. Active tags may contain functionally separated transmitters and receivers, and the tag need not respond on a frequency related to the reader's interrogation signal.[17]
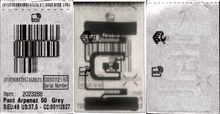
An Electronic Product Code (EPC) is one common type of data stored in a tag. When written into the tag by an RFID printer, the tag contains a 96-bit string of data. The first eight bits are a header which identifies the version of the protocol. The next 28 bits identify the organization that manages the data for this tag; the organization number is assigned by the EPCGlobal consortium. The next 24 bits are an object class, identifying the kind of product; the last 36 bits are a unique serial number for a particular tag. These last two fields are set by the organization that issued the tag. Rather like a URL, the total electronic product code number can be used as a key into a global database to uniquely identify a particular product.[18]
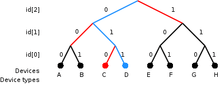
Often more than one tag will respond to a tag reader, for example, many individual products with tags may be shipped in a common box or on a common pallet. Collision detection is important to allow reading of data. Two different types of protocols are used to "singulate" a particular tag, allowing its data to be read in the midst of many similar tags. In a slotted Aloha system, the reader broadcasts an initialization command and a parameter that the tags individually use to pseudo-randomly delay their responses. When using an "adaptive binary tree" protocol, the reader sends an initialization symbol and then transmits one bit of ID data at a time; only tags with matching bits respond, and eventually only one tag matches the complete ID string.[19]
Both methods have drawbacks when used with many tags or with multiple overlapping readers.
Bulk reading
"Bulk reading" is a strategy for interrogating multiple tags at the same time, but lacks sufficient precision for inventory control. A group of objects, all of them RFID tagged, are read completely from one single reader position at one time. Bulk reading is a possible use of HF (ISO 18000-3), UHF (ISO 18000-6) and SHF (ISO 18000-4) RFID tags. However, as tags respond strictly sequentially, the time needed for bulk reading grows linearly with the number of labels to be read. This means it takes at least twice as long to read twice as many labels. Due to collision effects, the time required is greater. [20]
A group of tags has to be illuminated by the interrogating signal just like a single tag. This is not a challenge concerning energy, but with respect to visibility; if any of the tags are shielded by other tags, they might not be sufficiently illuminated to return a sufficient response. The response conditions for inductively coupled HF RFID tags and coil antennas in magnetic fields appear better than for UHF or SHF dipole fields, but then distance limits apply and may prevent success.
Under operational conditions, bulk reading is not reliable. Bulk reading can be a rough guide for logistics decisions, but due to a high proportion of reading failures, it is not (yet) suitable for inventory management. However, when a single RFID tag might be seen as not guaranteeing a proper read, a bunch of RFID tags, where at least one will respond, may be a safer approach for detecting a known grouping of objects. In this respect, bulk reading is a fuzzy method for process support. From the perspective of cost and effect, bulk reading is not reported as an economical approach to secure process control in logistics.[21]
Miniaturization
RFID tags are easy to conceal or incorporate in other items. For example, in 2009 researchers at Bristol University successfully glued RFID micro-transponders to live ants in order to study their behavior.[22] This trend towards increasingly miniaturized RFIDs is likely to continue as technology advances.
Hitachi holds the record for the smallest RFID chip, at 0.05 mm × 0.05 mm. This is 1/64th the size of the previous record holder, the mu-chip.[23] Manufacture is enabled by using the silicon-on-insulator (SOI) process. These dust-sized chips can store 38-digit numbers using 128-bit Read Only Memory (ROM).[24] A major challenge is the attachment of antennas, thus limiting read range to only millimeters.
Lifecycle
Manufacture
The microchip is designed and made by a semiconductor manufacturer. The tag manufacturer cuts the chip from the wafer and connects it to the antenna.[12]
The antenna is usually designed and made by a tag manufacturer. It can be made out of copper, aluminum, or silver strips. The antenna can take different shapes: a spiral, a single dipole antenna, two dipoles with one dipole perpendicular to another, or a folded dipole. The antenna length and geometry depends on the frequency at which the tag operates.[12]
Chip and antenna are embedded onto a thin plastic substrate of 100 to 200 nm, for example polymer, PVC, Polyethylenetherephtalate (PET), phenolics, polyesters, styrene, or paper via copper etching or hot stamping. Fastest and cheapest process is via screen printing using conductive ink containing copper, nickel, or carbon.[12]
Disposal
Tags contain metals and recycling is desirable on environmental grounds.[25]
RFID tags can interfere with recycling in the waste stream: Aluminium antennas on glass containers can reduce the amount and quality of recycled glass, if they cannot be separated within the process.[25]:12
In the paper waste stream, laminated copper foil antennas do not readily break down, but have to be removed in pulp as a non-recyclable solid waste, while silver ink from printed, non-laminated labels remains with paper substrate and can not easily be extractable from paper.[26]
RFID tags which cannot be removed from products or do not contain a kill or partial kill-switch may present a privacy concern.[25]:12
As of 2012, the EU had not addressed the question of disposal in its Waste Electrical and Electronic Equipment Directive.[25]:13
Uses
The RFID tag can be affixed to an object and used to track and manage inventory, assets, people, etc. For example, it can be affixed to cars, computer equipment, books, mobile phones, etc.
RFID offers advantages over manual systems or use of bar codes. The tag can be read if passed near a reader, even if it is covered by the object or not visible. The tag can be read inside a case, carton, box or other container, and unlike barcodes, RFID tags can be read hundreds at a time. Bar codes can only be read one at a time using current devices.
In 2011, the cost of passive tags started at US$0.09 each; special tags, meant to be mounted on metal or withstand gamma sterilization, can go up to US$5. Active tags for tracking containers, medical assets, or monitoring environmental conditions in data centers start at US$50 and can go up over US$100 each. Battery-Assisted Passive (BAP) tags are in the US$3–10 range and also have sensor capability like temperature and humidity.[27]
RFID can be used in a variety of applications,[28][29] such as:

- Access management
- Tracking of goods
- Tracking of persons and animals[30]
- Toll collection and contactless payment
- Machine readable travel documents
- Smartdust (for massively distributed sensor networks)
- Locating lost airport baggage[31]
- Timing sporting events
- Tracking and billing processes
In 2010 three factors drove a significant increase in RFID usage: decreased cost of equipment and tags, increased performance to a reliability of 99.9% and a stable international standard around UHF passive RFID. The adoption of these standards were driven by EPCglobal, a joint venture between GS1 and GS1 US, which were responsible for driving global adoption of the barcode in the 1970s and 1980s. The EPCglobal Network was developed by the Auto-ID Center.[32]
Commerce
RFID provides a way for organizations to identify and manage stock, tools and equipment (asset tracking), etc. without manual data entry. Manufactured products such as automobiles or garments can be tracked through the factory and through shipping to the customer. Automatic identification with RFID can be used for inventory systems. Many organisations require that their vendors place RFID tags on all shipments to improve supply chain management.
Retail
RFID is used for item level tagging in retail stores. In addition to inventory control, this provides both protection against theft by customers (shoplifting) and employees ("shrinkage") by using electronic article surveillance (EAS), and a self checkout process for customers. Tags of different type can be physically removed with a special tool or deactivated electronically once items have been paid for.[33] On leaving the shop customers have to pass near an RFID detector; if they have items with active RFID tags, an alarm sounds, both indicating an unpaid-for item, and identifying what it is.
Casinos can use RFID to authenticate poker chips, and can selectively invalidate any chips known to be stolen.[34]
Access control

RFID tags are widely used in identification badges, replacing earlier magnetic stripe cards. These badges need only be held within a certain distance of the reader to authenticate the holder. Tags can also be placed on vehicles, which can be read at a distance, to allow entrance to controlled areas without having to stop the vehicle and present a card or enter an access code.
Advertising
In 2010 Vail Resorts began using UHF Passive RFID tags in ski passes. Facebook is using RFID cards at most of their live events to allow guests to automatically capture and post photos. The automotive brands have adopted RFID for social media product placement more quickly than other industries. Mercedes was an early adopter in 2011 at the PGA Golf Championships,[35] and by the 2013 Geneva Motor Show many of the larger brands were using RFID for social media marketing.[36]
Promotion tracking
To prevent retailers diverting products, manufacturers are exploring the use of RFID tags on promoted merchandise so that they can track exactly which product has sold through the supply chain at fully discounted prices.[37]
Transportation and logistics
Yard management, shipping and freight and distribution centers use RFID tracking. In the railroad industry, RFID tags mounted on locomotives and rolling stock identify the owner, identification number and type of equipment and its characteristics. This can be used with a database to identify the lading, origin, destination, etc. of the commodities being carried.[38]
In commercial aviation, RFID is used to support maintenance on commercial aircraft. RFID tags are used to identify baggage and cargo at several airports and airlines.[39][40]
Some countries are using RFID for vehicle registration and enforcement.[41] RFID can help detect and retrieve stolen cars.[42][43]

RFID is used in intelligent transportation systems. In New York City, RFID readers are deployed at intersections to track E-ZPass tags as a means for monitoring the traffic flow. The data is fed through the broadband wireless infrastructure to the traffic management center to be used in adaptive traffic control of the traffic lights.[44]
Hose stations and conveyance of fluids
The RFID antenna in a permanently installed coupling half (fixed part) unmistakably identifies the RFID transponder placed in the other coupling half (free part) after completed coupling. When connected the transponder of the free part transmits all important information contactless to the fixed part. The coupling's location can be clearly identified by the RFID transponder coding. The control is enabled to automatically start subsequent process steps.
Track & Trace test vehicles and prototype parts
In the automotive industry RFID is used to Track & Trace test vehicles and prototype parts (project Transparent Prototype).
Infrastructure management and protection
At least one company has introduced RFID to identify and locate underground infrastructure assets such as gas pipelines, sewer lines, electrical cables, communication cables, etc.[45]
Passports
The first RFID passports ("E-passport") were issued by Malaysia in 1998. In addition to information also contained on the visual data page of the passport, Malaysian e-passports record the travel history (time, date, and place) of entries and exits from the country.
Other countries that insert RFID in passports include Norway (2005),[46] Japan (March 1, 2006), most EU countries (around 2006), Australia, Hong Kong, the United States (2007), India (June 2008), Serbia (July 2008), Republic of Korea (August 2008), Taiwan (December 2008), Albania (January 2009), The Philippines (August 2009), Republic of Macedonia (2010), Canada (2013) and Israel (2017).
Standards for RFID passports are determined by the International Civil Aviation Organization (ICAO), and are contained in ICAO Document 9303, Part 1, Volumes 1 and 2 (6th edition, 2006). ICAO refers to the ISO/IEC 14443 RFID chips in e-passports as "contactless integrated circuits". ICAO standards provide for e-passports to be identifiable by a standard e-passport logo on the front cover.
Since 2006, RFID tags included in new United States passports will store the same information that is printed within the passport, and include a digital picture of the owner.[47] The United States Department of State initially stated the chips could only be read from a distance of 10 centimetres (3.9 in), but after widespread criticism and a clear demonstration that special equipment can read the test passports from 10 metres (33 ft) away,[48] the passports were designed to incorporate a thin metal lining to make it more difficult for unauthorized readers to skim information when the passport is closed. The department will also implement Basic Access Control (BAC), which functions as a personal identification number (PIN) in the form of characters printed on the passport data page. Before a passport's tag can be read, this PIN must be entered into an RFID reader. The BAC also enables the encryption of any communication between the chip and interrogator.[49]
Transportation payments
In many countries, RFID tags can be used to pay for mass transit fares on bus, trains, or subways, or to collect tolls on highways.
Some bike lockers are operated with RFID cards assigned to individual users. A prepaid card is required to open or enter a facility or locker and is used to track and charge based on how long the bike is parked.
The Zipcar car-sharing service uses RFID cards for locking and unlocking cars and for member identification.[50]
In Singapore, RFID replaces paper Season Parking Ticket (SPT).[51]
Animal identification
RFID tags for animals represent one of the oldest uses of RFID. Originally meant for large ranches and rough terrain, since the outbreak of mad-cow disease, RFID has become crucial in animal identification management. An implantable RFID tag or transponder can also be used for animal identification. The transponders are better known as PIT (Passive Integrated Transponder) tags, passive RFID, or "chips" on animals.[52] The Canadian Cattle Identification Agency began using RFID tags as a replacement for barcode tags. Currently CCIA tags are used in Wisconsin and by United States farmers on a voluntary basis. The USDA is currently developing its own program.
RFID tags are required for all cattle sold in Australia and in some states, sheep and goats as well. [53]
Human implantation
.jpg)
Biocompatible microchip implants that utilize RFID technology are being routinely implanted in humans. The first reported experiment with RFID implants was conducted by British professor of cybernetics Kevin Warwick who had an RFID chip implanted in his arm by his general practitioner George Boulos in 1998.[54][55] In 2004 the 'Baja Beach Clubs' operated by Conrad Chase in Barcelona[56] and Rotterdam offered implanted chips to identify their VIP customers, who could in turn use it to pay for service. In 2009 British scientist Mark Gasson had an advanced glass capsule RFID device surgically implanted into his left hand and subsequently demonstrated how a computer virus could wirelessly infect his implant and then be transmitted on to other systems.[57]
The Food and Drug Administration in the United States approved the use of RFID chips in humans in 2004.[58]
There is controversy regarding human applications of implantable RFID technology including concerns that individuals could potentially be tracked by carrying an identifier unique to them. Privacy advocates have protested against implantable RFID chips, warning of potential abuse. Some are concerned this could lead to abuse by an authoritarian government, to removal of freedoms,[59] and to the emergence of an "ultimate panopticon", a society where all citizens behave in a socially accepted manner because others might be watching.[60]
On July 22, 2006, Reuters reported that two hackers, Newitz and Westhues, at a conference in New York City demonstrated that they could clone the RFID signal from a human implanted RFID chip, indicating that the device was not as secure as was previously claimed.[61]
Institutions
Hospitals and healthcare
In healthcare, there is a need for increased visibility, efficiency, and gathering of data around relevant interactions. RFID tracking solutions are able to help healthcare facilities manage mobile medical equipment, improve patient workflow, monitor environmental conditions, and protect patients, staff and visitors from infection or other hazards.
Adoption of RFID in the medical industry has been widespread and very effective. Hospitals are among the first users to combine both active and passive RFID. Many successful deployments in the healthcare industry have been cited where active technology tracks high-value, or frequently moved items, where passive technology tracks smaller, lower cost items that only need room-level identification.[62] For example, medical facility rooms can collect data from transmissions of RFID badges worn by patients and employees, as well as from tags assigned to facility assets, such as mobile medical devices.[63] The U.S. Department of Veterans Affairs (VA) recently announced plans to deploy RFID in hospitals across America to improve care and reduce costs.[64]
A physical RFID tag may be incorporated with browser-based software to increase its efficacy. This software allows for different groups or specific hospital staff, nurses, and patients to see real-time data relevant to each piece of tracked equipment or personnel. Real-time data is stored and archived to make use of historical reporting functionality and to prove compliance with various industry regulations. This combination of RFID real-time locating system hardware and software provides a powerful data collection tool for facilities seeking to improve operational efficiency and reduce costs.
The trend is toward using ISO 18000-6c as the tag of choice and combining an active tagging system that relies on existing 802.11X wireless infrastructure for active tags.[65]
Since 2004 a number of U.S. hospitals have begun implanting patients with RFID tags and using RFID systems, usually for workflow and inventory management.[66][67][68] The use of RFID to prevent mix ups between sperm and ova in IVF clinics is also being considered.[69]
In October 2004, the FDA approved the USA's first RFID chips that can be implanted in humans. The 134 kHz RFID chips, from VeriChip Corp. can incorporate personal medical information and could save lives and limit injuries from errors in medical treatments, according to the company. Anti-RFID activists Katherine Albrecht and Liz McIntyre discovered an FDA Warning Letter that spelled out health risks.[70] According to the FDA, these include "adverse tissue reaction", "migration of the implanted transponder", "failure of implanted transponder", "electrical hazards" and "magnetic resonance imaging [MRI] incompatibility."
Libraries

Libraries have used RFID to replace the barcodes on library items. The tag can contain identifying information or may just be a key into a database. An RFID system may replace or supplement bar codes and may offer another method of inventory management and self-service checkout by patrons. It can also act as a security device, taking the place of the more traditional electromagnetic security strip.[71]
It is estimated that over 30 million library items worldwide now contain RFID tags, including some in the Vatican Library in Rome.[72]
Since RFID tags can be read through an item, there is no need to open a book cover or DVD case to scan an item, and a stack of books can be read simultaneously. Book tags can be read while books are in motion on a conveyor belt, which reduces staff time. This can all be done by the borrowers themselves, reducing the need for library staff assistance. With portable readers, inventories could be done on a whole shelf of materials within seconds.[73] However, as of 2008 this technology remained too costly for many smaller libraries, and the conversion period has been estimated at 11 months for an average-size library. A 2004 Dutch estimate was that a library which lends 100,000 books per year should plan on a cost of €50,000 (borrow- and return-stations: 12,500 each, detection porches 10,000 each; tags 0.36 each). RFID taking a large burden off staff could also mean that fewer staff will be needed, resulting in some of them getting laid off,[72] but that has so far not happened in North America where recent surveys have not returned a single library that cut staff because of adding RFID. In fact, library budgets are being reduced for personnel and increased for infrastructure, making it necessary for libraries to add automation to compensate for the reduced staff size. Also, the tasks that RFID takes over are largely not the primary tasks of librarians. A finding in the Netherlands is that borrowers are pleased with the fact that staff are now more available for answering questions.
Privacy concerns have been raised surrounding library use of RFID. Because some RFID tags can be read from up to 100 metres (330 ft), there is some concern over whether sensitive information could be collected from an unwilling source. However, library RFID tags do not contain any patron information,[74] and the tags used in the majority of libraries use a frequency only readable from approximately 10 feet (3.0 m).[71] Further, another non-library agency could potentially record the RFID tags of every person leaving the library without the library administrator's knowledge or consent. One simple option is to let the book transmit a code that has meaning only in conjunction with the library's database. Another possible enhancement would be to give each book a new code every time it is returned. In future, should readers become ubiquitous (and possibly networked), then stolen books could be traced even outside the library. Tag removal could be made difficult if the tags are so small that they fit invisibly inside a (random) page, possibly put there by the publisher.
Museums
RFID technologies are now also implemented in end-user applications in museums. An example was the custom-designed temporary research application, "eXspot," at the Exploratorium, a science museum in San Francisco, California. A visitor entering the museum received an RF Tag that could be carried as a card. The eXspot system enabled the visitor to receive information about specific exhibits. Aside from the exhibit information, the visitor could take photographs of themselves at the exhibit. It was also intended to allow the visitor to take data for later analysis. The collected information could be retrieved at home from a "personalized" website keyed to the RFID tag.[75]
Schools and universities
School authorities in the Japanese city of Osaka are now chipping children's clothing, backpacks, and student IDs in a primary school.[76] A school in Doncaster, England is piloting a monitoring system designed to keep tabs on pupils by tracking radio chips in their uniforms.[77] St Charles Sixth Form College in west London, England, started in 2008, uses an RFID card system to check in and out of the main gate, to both track attendance and prevent unauthorized entrance. Similarly, Whitcliffe Mount School in Cleckheaton, England uses RFID to track pupils and staff in and out of the building via a specially designed card. In the Philippines, some schools already use RFID in IDs for borrowing books. Gates in those particular schools have RFID ID scanners for buying items at a school shop and canteen. RFID is also used in the library, and to sign in and out for student and teacher attendance.
Sports

RFID for timing races began in the early 1990s with pigeon racing, introduced by the company Deister Electronics in Germany. RFID can provide race start and end timings for individuals in large races where it is impossible to get accurate stopwatch readings for every entrant.
In the race, the racers wear tags that are read by antennas placed alongside the track or on mats across the track. UHF tags provide accurate readings with specially designed antennas. Rush error, lap count errors and accidents at start time are avoided since anyone can start and finish any time without being in a batch mode.
The design of chip+antenna controls the range from which it can be read. Short range compact chips are twist tied to the shoe or velcro strapped to the ankle. These need to be about 400mm from the mat and so give very good temporal resolution. Alternatively, a chip plus a very large (125mm square) antenna can be incorporated into the bib number worn on the athlete's chest at about 1.25m height.
Passive and active RFID systems are used in off-road events such as Orienteering, Enduro and Hare and Hounds racing. Riders have a transponder on their person, normally on their arm. When they complete a lap they swipe or touch the receiver which is connected to a computer and log their lap time.
RFID is being adapted by many recruitment agencies which have a PET (physical endurance test) as their qualifying procedure, especially in cases where the candidate volumes may run into millions (Indian Railway recruitment cells, police and power sector).
A number of ski resorts have adopted RFID tags to provide skiers hands-free access to ski lifts. Skiers do not have to take their passes out of their pockets. Ski jackets have a left pocket into which the chip+card fits. This nearly contacts the sensor unit on the left of the turnstile as the skier pushes through to the lift. These systems were based on high frequency (HF) at 13.56 megahertz. The bulk of ski areas in Europe, from Verbier to Chamonix, use these systems.[78][79][80]
The NFL in the United States equips players with RFID chips that measures speed, distance and direction traveled by each player in real-time. Currently cameras stay focused on the quarterback; however, numerous plays are happening simultaneously on the field. The RFID chip will provide new insight into these simultaneous plays.[81] The chip triangulates the player's position within six inches and will be used to digitally broadcast replays. The RFID chip will make individual player information accessible to the public. The data will be available via the NFL 2015 app.[82] The RFID chips are manufactured by Zebra Technologies. Zebra Technologies tested the RFID chip in 18 stadiums last year to track vector data.[83]
Complement to barcode
RFID tags are often a complement, but not a substitute, for UPC or EAN barcodes. They may never completely replace barcodes, due in part to their higher cost and the advantage of multiple data sources on the same object. Also, unlike RFID labels, barcodes can be generated and distributed electronically, e.g. via e-mail or mobile phone, for printing or display by the recipient. An example is airline boarding passes. The new EPC, along with several other schemes, is widely available at reasonable cost.
The storage of data associated with tracking items will require many terabytes. Filtering and categorizing RFID data is needed to create useful information. It is likely that goods will be tracked by the pallet using RFID tags, and at package level with Universal Product Code (UPC) or EAN from unique barcodes.
The unique identity is a mandatory requirement for RFID tags, despite special choice of the numbering scheme. RFID tag data capacity is large enough that each individual tag will have a unique code, while current bar codes are limited to a single type code for a particular product. The uniqueness of RFID tags means that a product may be tracked as it moves from location to location, finally ending up in the consumer's hands. This may help to combat theft and other forms of product loss. The tracing of products is an important feature that is well supported with RFID tags containing a unique identity of the tag and the serial number of the object. This may help companies cope with quality deficiencies and resulting recall campaigns, but also contributes to concern about tracking and profiling of consumers after the sale.
Waste management
RFID use has recently developed in the waste management industry. RFID tags are installed on waste collection carts, linking carts to the owner's account for easy billing and service verification. The tag is embedded into a garbage and recycle container, and the RFID reader is affixed to the garbage and recycle trucks.[84] RFID also measures a customer's set-out rate and provides insight as to the number of carts serviced by each waste collection vehicle. This RFID process replaces traditional "pay as you throw" (PAYT) municipal solid waste usage-pricing models.
Telemetry
Active RFID tags have the potential to function as low-cost remote sensors that broadcast telemetry back to a base station. Applications of tagometry data could include sensing of road conditions by implanted beacons, weather reports, and noise level monitoring.[85]
Passive RFID tags can also report sensor data. For example, the Wireless Identification and Sensing Platform is a passive tag that reports temperature, acceleration and capacitance to commercial Gen2 RFID readers.
It is possible that active or battery-assisted passive (BAP) RFID tags could broadcast a signal to an in-store receiver to determine whether the RFID tag (product) is in the store.
Regulation and standardization
To avoid injuries to humans and animals RF transmission needs to be controlled.[86] A number of organizations have set standards for RFID, including the International Organization for Standardization (ISO), the International Electrotechnical Commission (IEC), ASTM International, the DASH7 Alliance and EPCglobal.
Several specific industries also have set guidelines, including the Financial Services Technology Consortium (FSTC) for tracking IT Assets with RFID, the Computer Technology Industry Association CompTIA for certifying RFID engineers, and the International Airlines Transport Association IATA for luggage in airports.
Every country can set its own rules for frequency allocation for RFID tags, and not all radio bands are available in all countries. These frequencies are known as the ISM bands (Industrial Scientific and Medical bands). The return signal of the tag may still cause interference for other radio users.
- Low-frequency (LF: 125–134.2 kHz and 140–148.5 kHz) (LowFID) tags and high-frequency (HF: 13.56 MHz) (HighFID) tags can be used globally without a license.
- Ultra-high-frequency (UHF: 865–928 MHz) (Ultra-HighFID or UHFID) tags cannot be used globally as there is no single global standard and regulations differ from country to country.
In North America, UHF can be used unlicensed for 902–928 MHz (±13 MHz from the 915 MHz center frequency), but restrictions exist for transmission power. In Europe, RFID and other low-power radio applications are regulated by ETSI recommendations EN 300 220 and EN 302 208, and ERO recommendation 70 03, allowing RFID operation with somewhat complex band restrictions from 865–868 MHz. Readers are required to monitor a channel before transmitting ("Listen Before Talk"); this requirement has led to some restrictions on performance, the resolution of which is a subject of current research. The North American UHF standard is not accepted in France as it interferes with its military bands. On July 25, 2012, Japan changed its UHF band to 920 MHz, more closely matching the United States’ 915 MHz band.
In some countries, a site license is needed, which needs to be applied for at the local authorities, and can be revoked.
As of 31 October 2014, regulations are in place in 78 countries representing ca. 96.5% of the world's GDP, and work on regulations was in progress in three countries representing circa 1% of the world's GDP.[87]
Standards that have been made regarding RFID include:
- ISO 11784/11785 – Animal identification. Uses 134.2 kHz.
- ISO 14223 – Radiofrequency identification of animals – Advanced transponders
- ISO/IEC 14443: This standard is a popular HF (13.56 MHz) standard for HighFIDs which is being used as the basis of RFID-enabled passports under ICAO 9303. The Near Field Communication standard that lets mobile devices act as RFID readers/transponders is also based on ISO/IEC 14443.
- ISO/IEC 15693: This is also a popular HF (13.56 MHz) standard for HighFIDs widely used for non-contact smart payment and credit cards.
- ISO/IEC 18000: Information technology—Radio frequency identification for item management:
- ISO/IEC 18092 Information technology—Telecommunications and information exchange between systems—Near Field Communication—Interface and Protocol (NFCIP-1)
- ISO 18185: This is the industry standard for electronic seals or "e-seals" for tracking cargo containers using the 433 MHz and 2.4 GHz frequencies.
- ISO/IEC 21481 Information technology—Telecommunications and information exchange between systems—Near Field Communication Interface and Protocol −2 (NFCIP-2)
- ASTM D7434, Standard Test Method for Determining the Performance of Passive Radio Frequency Identification (RFID) Transponders on Palletized or Unitized Loads
- ASTM D7435, Standard Test Method for Determining the Performance of Passive Radio Frequency Identification (RFID) Transponders on Loaded Containers
- ASTM D7580, Standard Test Method for Rotary Stretch Wrapper Method for Determining the Readability of Passive RFID Transponders on Homogenous Palletized or Unitized Loads
- ISO 28560-2— specifies encoding standards and data model to be used within libraries.[88]
In order to ensure global interoperability of products, several organizations have set up additional standards for RFID testing. These standards include conformance, performance and interoperability tests.
EPC Gen2
EPC Gen2 is short for EPCglobal UHF Class 1 Generation 2.
EPCglobal, a joint venture between GS1 and GS1 US, is working on international standards for the use of mostly passive RFID and the Electronic Product Code (EPC) in the identification of many items in the supply chain for companies worldwide.
One of the missions of EPCglobal was to simplify the Babel of protocols prevalent in the RFID world in the 1990s. Two tag air interfaces (the protocol for exchanging information between a tag and a reader) were defined (but not ratified) by EPCglobal prior to 2003. These protocols, commonly known as Class 0 and Class 1, saw significant commercial implementation in 2002–2005.[89]
In 2004, the Hardware Action Group created a new protocol, the Class 1 Generation 2 interface, which addressed a number of problems that had been experienced with Class 0 and Class 1 tags. The EPC Gen2 standard was approved in December 2004. This was approved after a contention from Intermec that the standard may infringe a number of their RFID-related patents. It was decided that the standard itself does not infringe their patents, making the standard royalty free.[90] The EPC Gen2 standard was adopted with minor modifications as ISO 18000-6C in 2006.[91]
In 2007, the lowest cost of Gen2 EPC inlay was offered by the now-defunct company SmartCode, at a price of $0.05 apiece in volumes of 100 million or more.[92]
Problems and concerns
Data flooding
Not every successful reading of a tag (an observation) is useful for business purposes. A large amount of data may be generated that is not useful for managing inventory or other applications. For example, a customer moving a product from one shelf to another, or a pallet load of articles that passes several readers while being moved in a warehouse, are events that do not produce data that are meaningful to an inventory control system.[93]
Event filtering is required to reduce this data inflow to a meaningful depiction of moving goods passing a threshold. Various concepts have been designed, mainly offered as middleware performing the filtering from noisy and redundant raw data to significant processed data.
Global standardization
The frequencies used for UHF RFID in the USA are as of 2007 incompatible with those of Europe or Japan. Furthermore, no emerging standard has yet become as universal as the barcode.[94] To address international trade concerns, it is necessary to use a tag that is operational within all of the international frequency domains.
Security concerns
A primary RFID security concern is the illicit tracking of RFID tags. Tags, which are world-readable, pose a risk to both personal location privacy and corporate/military security. Such concerns have been raised with respect to the United States Department of Defense's recent adoption of RFID tags for supply chain management.[95] More generally, privacy organizations have expressed concerns in the context of ongoing efforts to embed electronic product code (EPC) RFID tags in consumer products. This is mostly as result of the fact that RFID tags can be read, and legitimate transactions with readers can be eavesdropped, from non-trivial distances. RFID used in access control, payment and eID (e-passport) systems operate at a shorter range than EPC RFID systems but are also vulnerable to skimming and eavesdropping, albeit at shorter distance.[96]
A second method of prevention is by using cryptography. Rolling codes and challenge-response authentication (CRA) are commonly used to foil monitor-repetition of the messages between the tag and reader; as any messages that have been recorded would prove to be unsuccessful on repeat transmission. Rolling codes rely upon the tag's id being changed after each interrogation, while CRA uses software to ask for a cryptographically coded response from the tag. The protocols used during CRA can be symmetric, or may use public key cryptography.[97]
Unauthorized reading of RFID tags presents a risk to privacy and to business secrecy.[98] Unauthorized readers can potentially use RFID information to identify or track packages, consumers, carriers, or the contents of a package.[97] Several prototype systems are being developed to combat unauthorized reading, including RFID signal interruption,[99] as well as the possibility of legislation, and 700 scientific papers have been published on this matter since 2002.[100] There are also concerns that the database structure of Object Naming Service may be susceptible to infiltration, similar to denial-of-service attacks, after the EPCglobal Network ONS root servers were shown to be vulnerable.[101]
Shielding
In an effort to prevent the passive “skimming” of RFID-enabled cards or passports, the U.S. General Services Administration (GSA) issued a set of test procedures for evaluating electromagnetically opaque sleeves.[104] For shielding products to be in compliance with FIPS-201 guidelines, they must meet or exceed this published standard; compliant products are listed on the website of the U.S. CIO's FIPS-201 Evaluation Program.[105] The United States government requires that when new ID cards are issued, they must be delivered with an approved shielding sleeve or holder.[106] Although many wallets and passport holders are advertised to protect personal information, there is little evidence that RFID skimming is a serious threat to consumers; data encryption and use of EMV chips rather than RFID makes this sort of theft rare.[107][108]
There are contradictory opinions as to whether aluminum can prevent reading of RFID chips. Some people claim that aluminum shielding, essentially creating a Faraday cage, does work.[109] Others claim that simply wrapping an RFID card in aluminum foil only makes transmission more difficult and is not completely effective at preventing it.[110]
Shielding effectiveness depends on the frequency being used. Low-frequency LowFID tags, like those used in implantable devices for humans and pets, are relatively resistant to shielding, although thick metal foil will prevent most reads. High frequency HighFID tags (13.56 MHz—smart cards and access badges) are sensitive to shielding and are difficult to read when within a few centimetres of a metal surface. UHF Ultra-HighFID tags (pallets and cartons) are difficult to read when placed within a few millimetres of a metal surface, although their read range is actually increased when they are spaced 2–4 cm from a metal surface due to positive reinforcement of the reflected wave and the incident wave at the tag.[111]
Controversies
Privacy
The use of RFID has engendered considerable controversy and even product boycotts by consumer privacy advocates. Consumer privacy experts Katherine Albrecht and Liz McIntyre are two prominent critics of the "spychip" technology. The two main privacy concerns regarding RFID are:
- Since the owner of an item will not necessarily be aware of the presence of an RFID tag and the tag can be read at a distance without the knowledge of the individual, it becomes possible to gather sensitive data about an individual without consent.
- If a tagged item is paid for by credit card or in conjunction with use of a loyalty card, then it would be possible to indirectly deduce the identity of the purchaser by reading the globally unique ID of that item (contained in the RFID tag). This is only true if the person doing the watching also had access to the loyalty card data and the credit card data, and the person with the equipment knows where the purchaser is going to be.
Most concerns revolve around the fact that RFID tags affixed to products remain functional even after the products have been purchased and taken home and thus can be used for surveillance and other purposes unrelated to their supply chain inventory functions.[112]
The RFID Network argued that these fears are unfounded in the first episode of their syndicated cable TV series by letting RF engineers demonstrate how RFID works.[113] They provided images of RF engineers driving an RFID-enabled van around a building and trying to take an inventory of items inside. They discussed satellite tracking of a passive RFID tag, which is surprising since the maximum range is under 200m.
The concerns raised by the above may be addressed in part by use of the Clipped Tag. The Clipped Tag is an RFID tag designed to increase consumer privacy. The Clipped Tag has been suggested by IBM researchers Paul Moskowitz and Guenter Karjoth. After the point of sale, a consumer may tear off a portion of the tag. This allows the transformation of a long-range tag into a proximity tag that still may be read, but only at short range – less than a few inches or centimeters. The modification of the tag may be confirmed visually. The tag may still be used later for returns, recalls, or recycling.
However, read range is a function of both the reader and the tag itself. Improvements in technology may increase read ranges for tags. Tags may be read at longer ranges than they are designed for by increasing reader power. The limit on read distance then becomes the signal-to-noise ratio of the signal reflected from the tag back to the reader. Researchers at two security conferences have demonstrated that passive Ultra-HighFID tags normally read at ranges of up to 30 feet, can be read at ranges of 50 to 69 feet using suitable equipment.[114][115]
In January 2004 privacy advocates from CASPIAN and the German privacy group FoeBuD were invited to the METRO Future Store in Germany, where an RFID pilot project was implemented. It was uncovered by accident that METRO "Payback" customer loyalty cards contained RFID tags with customer IDs, a fact that was disclosed neither to customers receiving the cards, nor to this group of privacy advocates. This happened despite assurances by METRO that no customer identification data was tracked and all RFID usage was clearly disclosed.[116]
During the UN World Summit on the Information Society (WSIS) between the 16th to 18 November 2005, founder of the free software movement, Richard Stallman, protested the use of RFID security cards by covering his card with aluminum foil.[117]
In 2004–2005 the Federal Trade Commission staff conducted a workshop and review of RFID privacy concerns and issued a report recommending best practices.[118]
RFID was one of the main topics of 2006 Chaos Communication Congress (organized by the Chaos Computer Club in Berlin) and triggered a big press debate. Topics included: electronic passports, Mifare cryptography and the tickets for the FIFA World Cup 2006. Talks showed how the first real world mass application of RFID at the 2006 FIFA Football World Cup worked. Group monochrom staged a special 'Hack RFID' song.[119]
Government control
Some individuals have grown to fear the loss of rights due to RFID human implantation.
By early 2007, Chris Paget of San Francisco, California, showed that RFID information could be pulled from a US passport card by using only $250 worth of equipment. This suggests that with the information captured, it would be possible to clone such cards.[120]
According to ZDNet, critics believe that RFID will lead to tracking individuals' every movement and will be an invasion of privacy.[121] In the book SpyChips: How Major Corporations and Government Plan to Track Your Every Move by Katherine Albrecht and Liz McIntyre, one is encouraged to "imagine a world of no privacy. Where your every purchase is monitored and recorded in a database and your every belonging is numbered. Where someone many states away or perhaps in another country has a record of everything you have ever bought. What's more, they can be tracked and monitored remotely".[122]
Deliberate destruction in clothing and other items
According to an RSA laboratories FAQ, RFID tags can be destroyed by a standard microwave oven;[123] however some types of RFID tags, particularly those constructed to radiate using large metallic antennas (in particular RF tags and EPC tags), may catch fire if subjected to this process for too long (as would any metallic item inside a microwave oven). This simple method cannot safely be used to deactivate RFID features in electronic devices, or those implanted in living tissue, because of the risk of damage to the "host". However the time required is extremely short (a second or two of radiation) and the method works in many other non-electronic and inanimate items, long before heat or fire become of concern.[124]
Some RFID tags implement a "kill command" mechanism to permanently and irreversibly disable them. This mechanism can be applied if the chip itself is trusted or the mechanism is known by the person that wants to "kill" the tag.
UHF RFID tags that comply with the EPC2 Gen 2 Class 1 standard usually support this mechanism, while protecting the chip from being killed with a password.[125] Guessing or cracking this needed 32-bit password for killing a tag would not be difficult for a determined attacker.[126]
Reliability
Tag reliability
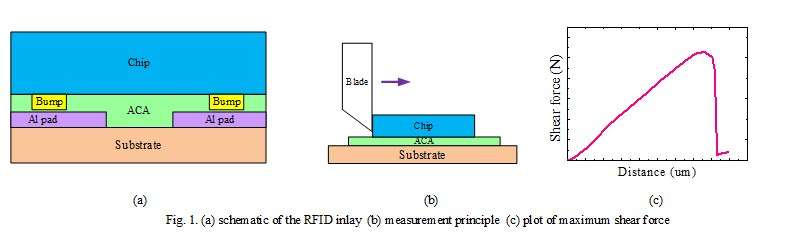
Generally, an RFID tag has an inlay, composed of three components, namely silicon (Si) chip, ACA (Anisotropic conductive adhesive) layer and flexible substrate (Al/PET), as shown in Fig.1(a). The chip is flip-chip assembled on the Al/PET flexible substrate through ACA hot-press process. After bonding process, the shear strength of the tag inlay can be measured using the bond tester. The shear strength test principle is based on the solder ball shear test standard,[127] as shown in Fig.1(b). A rigid clamping device is used to fix one side of the substrate, and the vacuum plate is used to absorb the bottom of the sample. The blade is pushed horizontally from one side. The maximum shear force for each joint, which finally separates the chip from the substrate, is recorded, as shown in Fig.1(c). [128]
See also
- AS5678
- Balise
- Bin bug
- Chipless RFID
- Internet of Things
- Mass surveillance
- Microchip implant (human)
- Near Field Communication (NFC)
- PositiveID
- Privacy by design
- Proximity card
- Resonant inductive coupling
- RFdump
- RFID in schools
- RFID Journal
- RFID on metal
- RSA blocker tag
- Smart label
- Speedpass
- TecTile
- Tracking system
References
- Automatic Identification and Data Collection (AIDC) Archived May 5, 2016, at the Wayback Machine
- Angell, I., Kietzmann, J. (2006). "RFID and the end of cash?" (PDF). Communications of the ACM. 49 (12): 90–96. doi:10.1145/1183236.1183237. Archived from the original (PDF) on 2014-02-24. Retrieved 9 November 2013.CS1 maint: multiple names: authors list (link)
- "RFID Forecasts, Players and Opportunities 2019-2029". IDTechEx. 2020-02-27.
- Hacking Exposed Linux: Linux Security Secrets & Solutions (third ed.). McGraw-Hill Osborne Media. 2008. p. 298. ISBN 978-0-07-226257-5.
- Stockman, Harry (October 1948), "Communication by Means of Reflected Power", Proceedings of the IRE, 36 (10): 1196–1204, doi:10.1109/JRPROC.1948.226245
- "Genesis of the Versatile RFID Tag". RFID Journal. Retrieved 2013-09-22.
- US 3713148, Cardullo, Mario W. & William L. Parks, "Transponder apparatus and system", published May 21, 1970, issued Jan 23, 1973
- Landt, Jerry (2001). "Shrouds of Time: The history of RFID" (PDF). AIM, Inc. Archived from the original (PDF) on 2009-03-27. Retrieved 2006-05-31.
- "Real Time Location Systems" (PDF). clarinox. Retrieved 2010-08-04.
- Charles A. Walton "Portable radio frequency emitting identifier" U.S. Patent 4,384,288 issue date May 17, 1983
- "RFID-Tag". Behance. Retrieved 15 July 2018.
- "Construction of RFID Tags - RFID chip and antenna". RFID4U. n.d. Retrieved 2020-03-01.
- "How Does RFID Technology Work?". MakeUseOf. Retrieved 2019-04-22.
- Sen, Dipankar; Sen, Prosenjit; Das, Anand M. (2009), RFID For Energy and Utility Industries, PennWell, ISBN 978-1-59370-105-5, pp. 1-48
- Weis, Stephen A. (2007), RFID (Radio Frequency Identification): Principles and Applications, MIT CSAIL, CiteSeerX 10.1.1.182.5224
- "RFID and Rail: Advanced Tracking Technology – Railway Technology". 16 March 2008. Retrieved 14 March 2018.
- Daniel M. Dobkin, The RF in RFID: Passive UHF RFID In Practice, Newnes 2008 ISBN 978-0-7506-8209-1, chapter 8
- John R. Vacca Computer and information security handbook, Morgan Kaufmann, 2009 ISBN 0-12-374354-0, page 208
- Bill Glover, Himanshu Bhatt ,RFID essentials, O'Reilly Media, Inc., 2006 ISBN 0-596-00944-5, pages 88–89
- "Frequently Asked Questions - RFID Journal". www.rfidjournal.com. Retrieved 2019-04-22.
- "STGF Report" (PDF).
- "Ants' home search habit uncovered". BBC News. 2009-04-22. Retrieved 2013-09-03.
- "Hitachi's RFID powder freaks us the heck out". Engadget. Retrieved 2010-04-24.
- TFOT (2007). "Hitachi Develops World's Smallest RFID Chip". Archived from the original on 2009-04-16. Retrieved 2009-03-27.
- Europe, RAND (2012). "SMART TRASH: Study on RFID tags and the recycling industry: Interim Report (D3) SMART 2010/0042". www.rand.org. Retrieved 2020-03-01.
- "Can RFID Tags Become An Environmental Problem?". www.industryweek.com. 2005-08-05. Retrieved 2020-03-01.
- "EPTLS | The Electronic Product Tag & Labelling Scheme". eptls.org. Retrieved 2019-04-22.
- Martein Meints (June 2007). "D3.7 A Structured Collection on Information and Literature on Technological and Usability Aspects of Radio Frequency Identification (RFID), FIDIS deliverable 3(7)". Retrieved 2013-09-22.
- Paolo Magrassi (2001). "A World Of Smart Objects: The Role Of Auto Identification Technologies". Retrieved 2007-06-24.
- Silva, S., Lowry, M., Macaya-Solis, C., Byatt, B., & Lucas, M. C. (2017). Can navigation locks be used to help migratory fishes with poor swimming performance pass tidal barrages? A test with lampreys. Ecological engineering, 102, 291–302.
- Pete Harrison (2009-07-28). "EU considers overhauling rules for lost air luggage". Reuters. Retrieved 2009-09-09.
- [Miles, Stephen Bell (2011). RFID Technology and Applications. London: Cambridge University Press. pp. 6–8]
- "Benefits of RFID in Theft Protection – CONTROLTEK". Controltek. 14 February 2014. Retrieved 11 October 2017.
- Rohrlich, Justin (15 December 2010). "RFID-Tagged Gaming Chips Render Hotel Bellagio Robbery Haul Worthless". Minyanville Financial Media. Retrieved 16 December 2010.
- "Mercedes Provides RFID Facebook Checkins at PGA Championship". Mashable.com. 2011-08-11. Retrieved 2013-09-22.
- Patrick Sweeney (2013-03-26). "Social Media Winner's Circle at Geneva Motor Show [Video". Social Media Today. Archived from the original on 2013-09-27. Retrieved 2013-09-22.
- James P. Farrell & Ralf Saykiewicz. "Keeping Track of Promotion Progress: How Marketing Will Become the Greatest Advocate of RFID". Consumer Goods Technology. Archived from the original on 2008-04-11. Retrieved 2008-04-10.
- "AEI technology". Softrail. Archived from the original on 2008-04-06. Retrieved 2008-10-12.
- "Qantas Next Generation Check-in". Qantas Airways Limited. Retrieved 2010-12-27.
- Archived August 1, 2015, at the Wayback Machine
- "Bermuda's RFID Vehicle Registration System Could Save $2 Million/Year". Rfidjournal.com. 2007-05-18. Retrieved 2013-09-03.
- "Smart License May Cut Car Theft". Rfidjournal.com. 2002-10-11. Retrieved 2013-09-03.
- "Mexico's Electronic Vehicle Registration system opens with Sirit open road toll technology, Dec 29, 2009". Tollroadsnews.com. Archived from the original on 2013-07-03. Retrieved 2013-09-03.
- "New York's award-winning traffic control system". ITS International. January–February 2013. Retrieved 3 May 2014.
- "Locating and Marking Products". 3M Company. Retrieved 25 June 2012.
- "Datatilsynet misfornøyd med nye pass". Digi.no. Archived from the original on 2008-04-05. Retrieved 2013-09-22.
- "Contactless inlays from SMARTRAC ordered for US ePassport project". Retrieved 2009-03-25.
- Lettice, John (30 January 2006). "Face and fingerprints swiped in Dutch biometric passport crack: Chip skimmed, then security breached". The Register. Archived from the original on 31 January 2006. Retrieved 9 September 2013.
- "United States sets date for E-passports".
- Mary Catherine O'Connor (7 January 2008). "RFID Is Key to Car Clubs' Success". RFID Journal. Retrieved 9 May 2011.
- Tay, Lay (2007-11-01). "HDB Introduces RFID Season Parking Ticket". RFID Asia. Retrieved 2009-10-17.
- "National Livestock Identification System". Meat & Livestock Australia Limited. Archived from the original on 2013-08-20. Retrieved 2013-09-03.
- Witt, Sam. "CNN – Is human chip implant wave of the future? – January 14, 1999". edition.cnn.com. Retrieved 14 March 2018.
- "Professor has world's first silicon chip implant". 26 August 1998. Retrieved 14 March 2018.
- "Technology | Barcelona clubbers get chipped". BBC News. 2004-09-29. Retrieved 2013-09-22.
- Gasson, M. N. (2010). "Human Enhancement: Could you become infected with a computer virus?" (PDF). 2010 IEEE International Symposium on Technology and Society. pp. 61–68. doi:10.1109/ISTAS.2010.5514651. ISBN 978-1-4244-7777-7.
- Greene, Thomas C. (2004). "Feds approve human RFID implants". Retrieved 2007-03-01.
- Monahan, Torin and Tyler Wall. 2007. Somatic Surveillance: Corporeal Control through Information Networks. Surveillance & Society 4 (3): 154–173 Archived 2016-06-15 at the Wayback Machine
- Kietzmann, J., Angell, I. (2010). "Panopticon revisited" (PDF). Communications of the ACM. 53 (6): 135–138. doi:10.1145/1743546.1743582. Archived from the original (PDF) on 2014-02-24. Retrieved 9 November 2013.CS1 maint: multiple names: authors list (link)
- Fulton, Nic (2006-07-22). "Reuters". Blogs.reuters.com. Retrieved 2013-09-03.
- "RFID Frequently Asked Questions". RFIDJournal.com. Retrieved 2013-05-20.
- "Group Health Reinvents Patient Care With RTLS". RFID Journal. 22 August 2012.
- "Veterans Affairs to Install RFID in Hospitals across America". Impinj. 14 June 2013. Archived from the original on 19 March 2014.
- Systems, computer media, and methods for using electromagnetic frequency (EMF) identification (ID) devices for monitoring, collection, analysis, use and tracking of personal, medical, transaction, and location data for one or more individuals, retrieved 2019-04-22
- Fisher, Jill A., Monahan, Torin (2012). "Evaluation of Real-time Location Systems in their Hospital Contexts" (PDF). International Journal of Medical Informatics. 81 (10): 705–712. doi:10.1016/j.ijmedinf.2012.07.001. PMID 22857790.CS1 maint: multiple names: authors list (link)
- Fisher, Jill A., Monahan, Torin (2008). "Tracking the Social Dimensions of RFID Systems in Hospitals" (PDF). International Journal of Medical Informatics. 77 (3): 176–183. doi:10.1016/j.ijmedinf.2007.04.010. PMID 17544841.CS1 maint: multiple names: authors list (link)
- Fisher, Jill A. 2006. Indoor Positioning and Digital Management: Emerging Surveillance Regimes in Hospitals. In T. Monahan (Ed), Surveillance and Security: Technological Politics and Power in Everyday Life (pp. 77–88). New York: Routledge.
- "Electronic tags for eggs, sperm and embryos – life – 30 March 2005". New Scientist. Retrieved 2010-04-24.
- "Verichip Special Report". spychips.com. Archived from the original on 2012-03-23. Retrieved 2013-09-22.
- Butters, Alan (December 2006). "Radio Frequency Identification: An Introduction for Library Professionals". Australasian Public Libraries and Information Services. 19 (4): 164–74. ISSN 1030-5033.
- Sing, Jay; Brar, Navjit; Fong, Carmen (2013). "The State of RFID Applications in Libraries". Information Technology and Libraries. 25–32: 24. doi:10.6017/ital.v25i1.3326.
- Wadham, Rachel (2003). "Radio Frequency Identification". Library Mosaics. 14 (5): 22.
- Dorman, David (December 2003). "RFID Poses No Problem for Patron Privacy". American Libraries. 34 (11): 86.
- Hsi, Sherry; Fait, Holly (2005). "RFID enhances visitors' museum experience at the Exploratorium". Communications of the ACM. 48 (9): 60–5. doi:10.1145/1081992.1082021.
- "Schoolchildren to be RFID-chipped". Networks.silicon.com. Archived from the original on April 27, 2012. Retrieved 2013-09-03.
- Williams, Christopher (2007-10-22). "Schoolkid chipping trial 'a success'". Theregister.co.uk. Retrieved 2013-09-03.
- "Epic Mix – Skiiers [sic] and Snowboarders Social Media Dream". 2010-09-07. Retrieved 2013-09-22.
- "Vail Resorts Launches Epic Mix | SNOWBOARD MAGAZINE". Archived from the original on 2010-09-04. Retrieved 2020-03-01.
- Kinsella, Bret. (2010-09-07) Vail shows that Consumer RFID delivers a better experience Archived 2010-11-06 at the Wayback Machine. Blog.odintechnologies.com. Retrieved on 2013-08-16.
- "How a pair of microchips could transform football into an intricate dance of data". DailyDot. 2015-08-12. Retrieved 1 September 2015.
- "The NFL has a (RFID) Chip on its shoulder". News Surgo Group. Archived from the original on 2015-09-06. Retrieved 1 September 2015.
- Moynihan, Tim (2015-08-07). "All NFL Players Are Getting RFID Chips This Season". Wired. Retrieved 1 September 2015.
- "RFID Still In Early Stages of Adoption by Waste Industry". 2016-08-10.
- 0001-0782
- "RFID Regulations". RFID4U. n.d. Retrieved 2020-03-01. Check date values in:
|date=(help) - "Regulatory status for using RFID in the EPC Gen 2 band (860 to 960 MHz) of the UHF spectrum" (PDF). GS1.org. 2014-10-31. Retrieved 2015-03-23.
- "ISO 28560-2:2011 – Information and documentation – RFID in libraries – Part 2: Encoding of RFID data elements based on rules from ISO/IEC 15962". www.iso.org. Retrieved 14 March 2018.
- "RFID Standards and Mandates".
- Roberti, Mark (2004-12-16). "EPCglobal Ratifies Gen 2 Standard". RFID Journal. Retrieved 2011-07-07.
- Catherine O'Connor, Mary (2004-07-12). "Gen 2 EPC Protocol Approved as ISO 18000-6C". RFID Journal. Retrieved 2011-07-07.
- Roberti, Mark (2006-05-06). "A 5-Cent Breakthrough". RFID Journal. Retrieved 2007-01-26.
- Bill Glover, Himanshu Bhatt, RFID Essentials, O'Reilly Media, Inc., 2006 ISBN 0-596-00944-5 page 43
- "Radio Silence". The Economist. 7 June 2007.
- "What's New". Radio Frequency Identification (RFID). 4 April 2007. Archived from the original on 28 February 2006.
- Hancke, Gerhard P (2011). "Practical eavesdropping and skimming attacks on high-frequency RFID tokens". Journal of Computer Security. 19 (2): 259–288. CiteSeerX 10.1.1.169.9341. doi:10.3233/JCS-2010-0407. Archived from the original on 27 May 2016. Retrieved 10 August 2012.
- Ilyas, edited by Syed Ahson, Mohammad (2008). "26.5". RFID handbook : applications, technology, security, and privacy ([Online-Ausg.] ed.). Boca Raton: CRC Press. p. 478. ISBN 9781420054996. Retrieved 7 August 2012.CS1 maint: extra text: authors list (link)
- "Business risks from naive use of RFID in tracking, tracing and logistics - Conference papers - VDE Publishing House". www.vde-verlag.de. Retrieved 2019-12-09.
- "RFID Privacy and Security". RSA Laboratories. Archived from the original on 2006-12-18. Retrieved 2013-09-22.
- "RFID Security and Privacy Lounge". Avoine.net. Retrieved 2013-09-22.
- Tedjasaputra, Adi (2006-12-11). "Putting RFID Network Security in Perspective". RFID Asia. Retrieved 2007-08-03.
- Albrecht, Katherine (2010). Microchip-induced tumors in laboratory rodents and dogs: A review of the literature 1990–2006. IEEE. pp. 337–349. doi:10.1109/ISTAS.2010.5514622. ISBN 978-1-4244-7777-7.
- Lewan, Todd (8 September 2007). "Chip Implants Linked to Animal Tumors". Washington Post.
- "Electromagnetically Opaque Sleeve Test Procedure version 3.0.0" (PDF). GSA.
- "FIPS 201 Evaluation Program Approved Products List (APL)". U.S. CIO and the Federal CIO Councils.
- "FIPS-201, Personal Identity Verification (PIV) of Federal Employees and Contractors" (PDF). NIST. Archived from the original (PDF) on 2010-12-26. Retrieved 2019-01-10.
- Oremus, Will (2015-08-25). "Do You Really Need an RFID-Blocking Wallet?". Slate Magazine. Retrieved 2019-11-10.
- "There Are Plenty Of RFID-Blocking Products, But Do You Need Them?". NPR.org. Retrieved 2019-11-10.
- "Can Aluminum Shield RFID Chips?". RFID Shield. Archived from the original on 2014-03-30. Retrieved 2007-03-27.
- "Aluminum Foil Does Not Stop RFID". Omniscience is Bliss.
- "A Primer on RFID" (PDF).
- Markus Hansen, Sebastian Meissner: Identification and Tracking of Individuals and Social Networks using the Electronic Product Code on RFID Tags, IFIP Summer School, Karlstad, 2007, Slides.
- "How to read data from rfid reader". 0y3v.errandrunner.org. Retrieved 2019-04-22.
- Archived September 28, 2011, at the Wayback Machine
- Archived February 7, 2009, at the Wayback Machine
- Katherine Albrecht; Liz McIntyre. "The METRO "Future Store" Special Report". Spychips. Archived from the original on 2005-05-08. Retrieved 2005-05-05.
- Richard M Stallman. "The WSIS in Tunis". Fsf.org. Retrieved 2013-09-22.
- "Radio Frequency Identification: Applications and Implications for Consumers" (PDF). Ftc.gov. March 2005. Retrieved 2013-09-22.
- monochrom. "R F I D". Archived from the original on 2010-02-20. Retrieved 2007-01-04.
- Iain Thomson in San Francisco. "Hacker clones passports in drive-by RFID heist – V3.co.uk – formerly vnunet.com". V3.co.uk. Archived from the original on 2010-03-24. Retrieved 2010-04-24.
- "Human chips more than skin-deep | Tech News on ZDNet". News.zdnet.com. Archived from the original on 2010-03-24. Retrieved 2010-04-24.
- Katherine Albrecht; Liz McIntyre (2005). Spychips: how major corporations and government plan to track your every move with RFID. Thomas Nelson Inc. ISBN 978-1-59555-020-0.
- "FAQ on RFID and RFID privacy". rsa.com. Retrieved 2015-03-23.
- "Declara | Your Personal Knowledge Engine". declara.com. Retrieved 2019-04-22.
- "EPC™ Radio-Frequency Identity Protocols Generation-2 UHF RFID, Version 2.0.0" (PDF). GS1.org. November 2013. Retrieved 23 March 2015.
- "EPC Gen 2 FAQ". Smart Card Alliance. July 2006. Archived from the original on 2015-03-20. Retrieved 2015-03-25.
- JEDEC Standard JESD22-B117A. [" Solder Ball Shear "]. JEDEC Solid State Technology Association. 2006.
- G. Wu et al. "Study on the shear strength degradation of ACA joints induced by different hygrothermal aging conditions ". Microelectronics Reliability. 2013.
External links
| Wikimedia Commons has media related to RFID. |
- An open source RFID library used as door opener
- UHF regulations overview by GS1
- What is RFID? Educational video by The RFID Network
- How RFID Works at HowStuffWorks
- Privacy concerns and proposed privacy legislation
- RFID at Curlie
- What is RFID? – animated explanation
- Hardgrave, Bill C.; Aloysius, John; Goyal, Sandeep (2009). "Does RFID improve inventory accuracy? A preliminary analysis". International Journal of RF Technologies: Research and Applications. 1 (1): 45–56. doi:10.1080/17545730802338333.
- IEEE Council on RFID