1
I know how to configure which algorithms I'm willing to use. But the actual algorithm used is based on negotiation between putty and the server. So how do I tell which algorithm is actually being used, once a connection is established?
1
I know how to configure which algorithms I'm willing to use. But the actual algorithm used is based on negotiation between putty and the server. So how do I tell which algorithm is actually being used, once a connection is established?
1
After making your connection in PuTTY, you can open the "Event Log" to see the negotiated encryption and MAC algorithms.
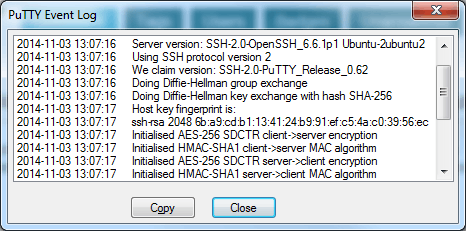
You can access the event log opening the session menu by clicking on the PuTTY icon in the top-left corner of the window.
And as an interesting aside, you can force a re-negotiation by opening the menu and selecting "Special Command" -> "Repeat key exchange" – heavyd – 2014-11-04T20:58:06.027