1
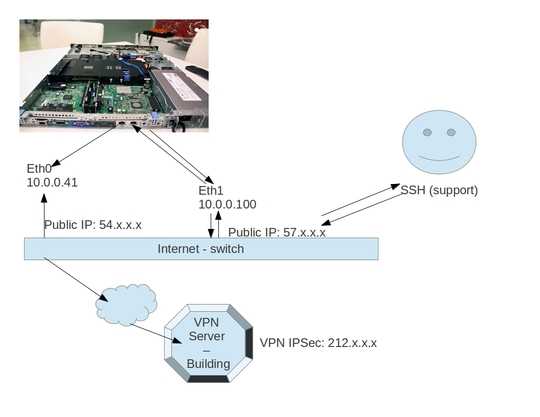
I have:
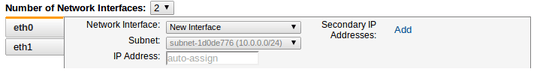
- eth0 interface with 10.0.0.41 having public ip 54.x.x.x (will be used for VPN client)
- eth1 interface with 10.0.0.100 having public ip 57.x.x.x
eth1 is where i am remotely connected using SSH eth0 will be connected to another server as VPN IPsec
because my default routing is eth1, while connecting to VPN it fails cause VPN server only allow ip 54.x.x.x not traffic from 57.x.x.x
Now, how can i tell routing that all traffic going to VPN server address: 212.x.x.x will be sent via eth0 (54.x.x.x) and still have eth1 (57.x.x.x) available for SSH remote access?
EDIT:
EDIT: does amazon allow me to have 2 different subnet public ip to my 2 network interface. it seems like no
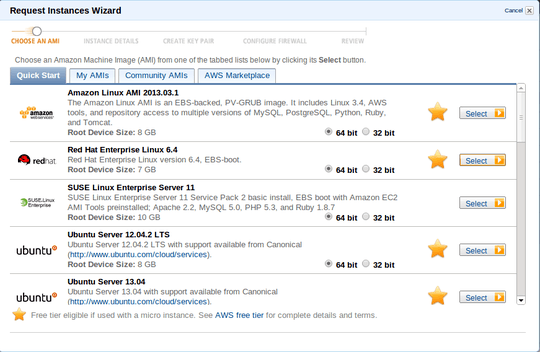
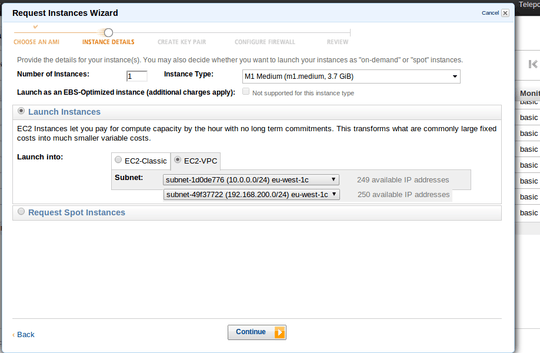
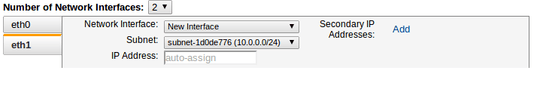
EDIT: Amazon EC2 - VPC with multiple subnets
http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Scenarios.html
Scenario 1: VPC with a Public Subnet Only - 1 subnet http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Scenario1.html
Scenario 2: VPC with Public and Private Subnets - 2 subnet http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Scenario2.html
Scenario 3: VPC with Public and Private Subnets and Hardware VPN Access - 3 subnet http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Scenario3.html
Scenario 4: VPC with a Private Subnet Only and Hardware VPN Access http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/VPC_Scenario4.html
EDIT:
Step 1: Amazon EC2 > Scenario 1: VPC with a Public Subnet Only - 1 subnet
Step 2: this will allow 10.0.0.0/24 subnet with 1:1 NAT
Step 3: Now to do the inbound and outbound traffic by-pass we should do:
ip rule add from 10.0.0.41/32 table 1 # outbound
ip rule add to 10.0.0.41/32 table 1 # inbound
ip route add default via 10.0.0.1 dev eth0 table 1
ip rule add from 10.0.0.100/32 table 2 # outbound
ip rule add to 10.0.0.100/32 table 2 # inbound
ip route add default via 10.0.0.1 dev eth1 table 2
Step 4: test it remotely assuming remote pc has: iamremotely_publicip
ping publicip_eth0
ping publicip_eth1
Step 5: inbound test
$ tcpdump -vv src iamremotely_publicip and not dst port 22 -i any
### inbound reply received for eth0
13:29:02.163426 IP (tos 0x0, ttl 55, id 0, offset 0, flags [DF], proto ICMP (1), length 84)
2.205.81.5 > ip-10-0-0-41.eu-west-1.compute.internal: ICMP echo request, id 10242, seq 1, length 64
### inbound reply received for eth1
13:24:05.415740 IP (tos 0x0, ttl 55, id 0, offset 0, flags [DF], proto ICMP (1), length 84)
2.205.81.5 > ip-10-0-0-100.eu-west-1.compute.internal: ICMP echo request, id 11808, seq 52, length 64
Step 6: outbound test on PC iamremotely_publicip
$ tcpdump -vv src publicip_eth0 and not dst port 22 -i any
$ tcpdump -vv src publicip_eth1 and not dst port 22 -i any
That works without VPN.
1The title doesn't seem to match your question. What you appear to want is *only 212.x.x.x traffic going out of eth0 and everything else out of eth1 - this would enable the VPN to the other server and ssh access from anywhere. – Paul – 2013-07-29T05:56:36.767
Working now: http://unix.stackexchange.com/a/85133/11085
– YumYumYum – 2013-08-01T01:46:37.127