WireShark logs all the network traffic it sees. In particular, on a WiFi network, WireShark will see all other traffic on the same WiFi network.
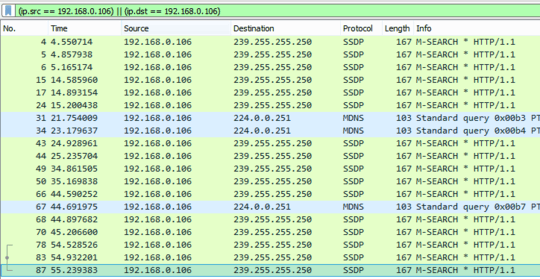
To see traffic to and from your laptop only, you will need to use a filter, similar to the one you defined, but using your laptop's IP address:
ip.src == 192.168.0.107 || ip.dst == 192.168.0.107
This is the way WireShark is intended to work, so that you can use a PC to monitor other devices, such as WebCams, printers, TVs, sound systems, etc, which cannot be used to run WireShark themselves.
I have tested this on Ubuntu with a Laptop which uses a Broadcom WiFi chip-set, and absolutely confirm that WireShark behaves in this manner. This is why I added my answer, because I was seeing buffers which were not explained by @dirkt's answer (which completely answers the buffers logged in the question), and I assumed that the questioner would come across these in future logs.
I was puzzled by my down-vote, so I asked a friend to run similar checks and he got different results on Windows with an Intel chip-set. I was surprised that the same software would behave differently on a different OS, but he suggested that maybe Windows stops the interface running in promiscuous mode.
I don't mind being down-voted if I get something wrong, but I would like to be told what is wrong so that I can correct it. We wouldn't accept a question that says "something's wrong - please help", and I don't see why down-votes should be regarded differently.
but the thing is there are lot of other devices on the LAN too. But I'm not seeing any traffic from other devices except the smartphone. – Bukks – 2017-12-12T02:40:46.570
You become the AP or you run in promiscuous mode. – djsmiley2k TMW – 2017-12-12T09:26:21.230
@djsmiley2k: Wireshark already put the interface in promiscious mode. If the WLAN router isn't copying packets between the Smartphone and some destination to your PC, having the interface on the PC in promiscious mode doesn't help at all. – dirkt – 2017-12-12T10:26:43.020