2
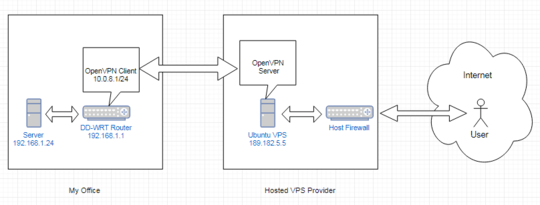
I have the following network layout:
With the VPN connection established, I want a user on the internet to be able to connect to port 555 on server 192.168.1.24, by using the IP address of the VPS server; i.e. 189.182.5.5:555.
What are the firewall/iptable rules I need in place on Ubuntu and DD-WRT to enable this? I have full control over both the DD-WRT router as well as the Ubuntu VPS, and the VPS provider allows me to open ports on their firewall.
Edit 1:
To clarify, 555 is an arbitrary port number. The reality is there are bout 7 ports (both TCP and UDP) that need to be reached, but I'm sure if I can be shown how to do one I'll figure the rest out. I'm also not against implementing a SOCKS proxy or SSH tunnel between DD-WRT and the VPS if that is an easier way of going about this.
Edit 2:
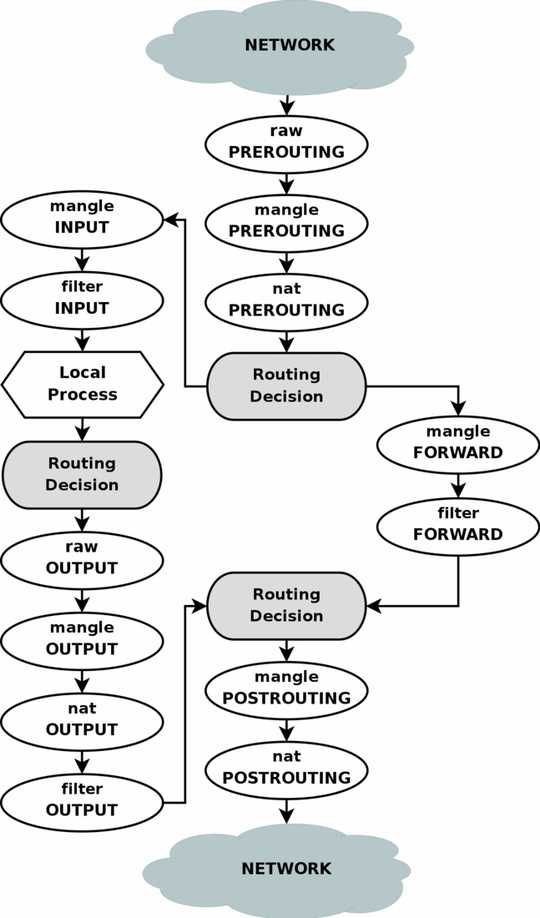
I've done some more testing. As a first step, I just want the VPS server to forward packets received on eth0 on port 555 to the VPN (tun0). Here's what I have:
I enabled tracing on the PREROUTING and OUTPUT raw tables for port 555 with these commands:
iptables -t raw -A PREROUTING -p tcp -m tcp --dport 555 -j TRACE
iptables -t raw -A OUTPUT -p tcp -m tcp --dport 555 -j TRACE
The raw table now looks like this:
-P PREROUTING ACCEPT
-P OUTPUT ACCEPT
-A PREROUTING -p tcp -m tcp --dport 555 -j TRACE
-A OUTPUT -p tcp -m tcp --dport 555 -j TRACE
The NAT table looks like this (I only added the last line, the rest I'm assuming is added by the OpenVPN server)
-P PREROUTING ACCEPT
-P INPUT ACCEPT
-P OUTPUT ACCEPT
-P POSTROUTING ACCEPT
-A POSTROUTING -s 10.8.0.0/24 ! -d 10.8.0.0/24 -j SNAT --to-source 189.182.5.5
-A POSTROUTING -o eth0 -j MASQUERADE
-A POSTROUTING -o tun0 -j MASQUERADE
The default iptables look like this:
-P INPUT ACCEPT
-P FORWARD ACCEPT
-P OUTPUT ACCEPT
-A INPUT -p tcp -m tcp --dport 22 -j ACCEPT
-A INPUT -p tcp -m tcp --dport 1194 -j ACCEPT
-A INPUT -p udp -m udp --dport 1194 -j ACCEPT
-A INPUT -i eth0 -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -i tun0 -m state --state RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -i eth0 -j ACCEPT
Now I run a port-specific TCP traceroute in nmap with this command:
nmap -sT -sU -p T:[555] -n --traceroute 189.182.5.5
The following entries appear in the VPS log:
Sep 13 08:09:01 ubuntu-768mb kernel: [480631.284612] TRACE: raw:PREROUTING:policy:2 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32647 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:01 ubuntu-768mb kernel: [480631.284671] TRACE: nat:PREROUTING:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32647 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:01 ubuntu-768mb kernel: [480631.284704] TRACE: filter:INPUT:policy:6 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32647 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:01 ubuntu-768mb kernel: [480631.284722] TRACE: nat:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32647 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480631.956697] TRACE: raw:PREROUTING:policy:2 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32649 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480631.956750] TRACE: nat:PREROUTING:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32649 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480631.956773] TRACE: filter:INPUT:policy:6 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32649 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480631.956783] TRACE: nat:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32649 DF PROTO=TCP SPT=31881 DPT=555 SEQ=953464685 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480632.150981] TRACE: raw:PREROUTING:policy:2 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32651 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480632.151061] TRACE: nat:PREROUTING:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32651 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480632.151095] TRACE: filter:INPUT:policy:6 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32651 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:02 ubuntu-768mb kernel: [480632.151113] TRACE: nat:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32651 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:03 ubuntu-768mb kernel: [480632.824527] TRACE: raw:PREROUTING:policy:2 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32653 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:03 ubuntu-768mb kernel: [480632.824583] TRACE: nat:PREROUTING:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32653 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:03 ubuntu-768mb kernel: [480632.824614] TRACE: filter:INPUT:policy:6 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32653 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 08:09:03 ubuntu-768mb kernel: [480632.824633] TRACE: nat:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=244 ID=32653 DF PROTO=TCP SPT=31882 DPT=555 SEQ=137592908 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Edit 3:
I've got the VPS to forward packets received on port 555 to the tun0 device, using the following command:
iptables -t nat -A PREROUTING -p tcp --dport 555 -j DNAT --to 10.8.0.2
This works because the VPN Server already creates a route for the 10.8.0/24 subnet targeting the tun0 interface:
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default 185.181.9.1 0.0.0.0 UG 0 0 0 eth0
10.8.0.0 * 255.255.255.0 U 0 0 0 tun0
185.181.9.0 * 255.255.255.0 U 0 0 0 eth0
Now in the log I can see the following entries:
Sep 13 11:55:03 ubuntu-768mb kernel: [ 6330.222757] TRACE: nat:PREROUTING:rule:2 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=189.182.5.5 LEN=52 TOS=0x00 PREC=0x00 TTL=117 ID=4482 DF PROTO=TCP SPT=38891 DPT=555 SEQ=3082300013 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 11:55:03 ubuntu-768mb kernel: [ 6330.222778] TRACE: mangle:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=10.8.0.1 LEN=52 TOS=0x00 PREC=0x00 TTL=117 ID=4482 DF PROTO=TCP SPT=38891 DPT=555 SEQ=3082300013 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 11:55:03 ubuntu-768mb kernel: [ 6330.222789] TRACE: filter:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=10.8.0.1 LEN=52 TOS=0x00 PREC=0x00 TTL=117 ID=4482 DF PROTO=TCP SPT=38891 DPT=555 SEQ=3082300013 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 11:55:03 ubuntu-768mb kernel: [ 6330.222799] TRACE: nat:INPUT:policy:1 IN=eth0 OUT= MAC=00:16:3e:0a:d3:67:80:71:1f:ca:8c:01:08:00 SRC=129.232.161.114 DST=10.8.0.1 LEN=52 TOS=0x00 PREC=0x00 TTL=117 ID=4482 DF PROTO=TCP SPT=38891 DPT=555 SEQ=3082300013 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
Sep 13 11:52:28 ubuntu-768mb kernel: [ 6175.035548] TRACE: mangle:POSTROUTING:policy:1 IN= OUT=tun0 SRC=129.232.161.114 DST=10.8.0.2 LEN=52 TOS=0x00 PREC=0x00 TTL=116 ID=4265 DF PROTO=TCP SPT=38840 DPT=555 SEQ=3344052408 ACK=0 WINDOW=64240 RES=0x00 SYN URGP=0 OPT (020405060103030801010402)
You'll see I'm currently using a DNAT rule to change the destination of the packet to 10.8.02, which is the IP address of tun0 on the client's side. I'm not sure if it should be 10.8.0.1, which is the tun0 address of the VPN Server?
What service protocol is this 'port' 555 traffic? If it is http/https then it would be easier to run a proxy on your VPS that proxies the traffic to the internal address. – Zoredache – 2017-09-12T17:45:48.363
Zoredache, the 555 is for illustrative purposes only, to make the question easier to answer. In reality there is about 6 ports, both tcp and udp – staterium – 2017-09-12T18:04:38.567