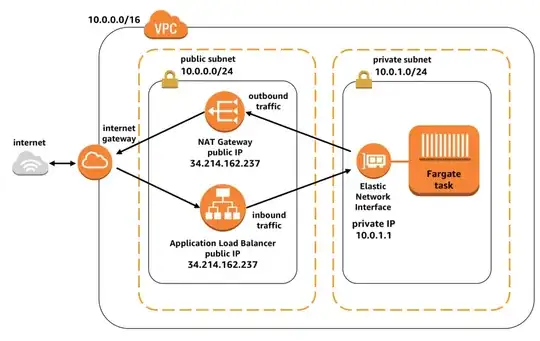
The architectural diagram shown below is taken from an AWS blog titled Task Networking in AWS Fargate. The blog was posted in January 2018.
The description that comes with the image states that:
This configuration allows your tasks in Fargate to be safely isolated from the rest of the internet. They can still initiate network communication with external resources via the NAT gateway, and still receive traffic from the public via the Application Load Balancer that is in the public subnet.
One problem that I have while trying to recreate the architecture is that the same IP address (which I assume is an Elastic IP) is used for both the NAT Gateway and the Application Load Balancer (ALB). I am not able to create an Elastic IP that is usable by both the NAT Gateway and the ALB. Is the diagram flawed, or am I missing something?