TL;DR;
In which registry hive does the ASP.NET Core Data protection system store it's keys when you are running your app in IIS with a worker process account without user profile
It looks like it's reusing the hive used by ASP.NET DPAPI, is it ?
We are setting up a bunch of asp.net core applications that need to work together and the antiforgery validation is currently messing things up for POST requests. It looks like ASP.NET core Data protection needs to be configured so that all applications are using the same keys.
All our applications currently run with a pool user for which neither the user profile nor the HKLM registry key ring seems to be available.
We are not allowed to activate the user profile for these pool users so we are looking to use the registry.
In the "Data protection" section of the "Host ASP.NET Core on Windows with IIS" document here we found that to configure data protection under IIS to persist the key ring, one of the approaches is to create Data Protection Registry Keys with a powershell script from github here :
This script is just called like this :
Provision-AutoGenKeys "4.0" "32" $poolSid
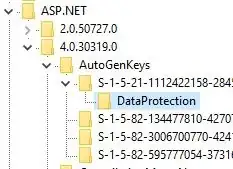
Reading this powershell script it seems that all it does is setting ACLs for the pool user on the following keys :
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\ASP.NET\2.0.50727.0\AutoGenKeys
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\ASP.NET\4.0.30319.0\AutoGenKeys
HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\ASP.NET\2.0.50727.0\AutoGenKeys
HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\ASP.NET\4.0.30319.0\AutoGenKeys
Here is where I'm getting totally confused.... these look like hives for the "old" autogenerated keys for encryption by ASP.NET, not ASP.NET Core....
So, I'm wondering... is Microsoft reusing those hives for ASP.NET Core Data Protection ?
Or should I look elsewhere ?