Our Microsoft SQL Servers are running on Windows Servers which are part of an Active Directory domain.
For easy user management, our SQL authorization is set up by using the Active Directory User Groups as explained in this post.
Now this works fine as long as everyone is working inside the domain. People login to their computer using their AD credentials and can connect to the SQL server by using the "Windows Authentication".
Problem is that our users will also be working on other client computers which are not part of the Active Directory domain (and adding them to the domain is not an option).
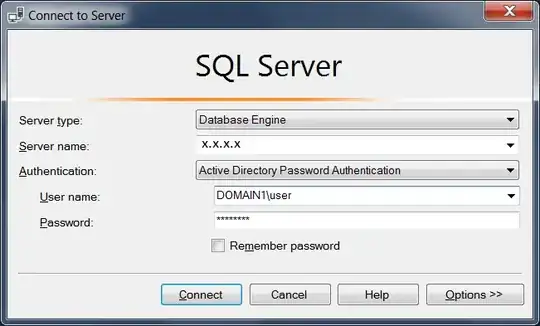
I was hoping they could simply keep using their AD credentials to login to the server by using the AD authentication as mentioned in the SQL Server login screen.
However this does not seem to be working.
Logging in with Acive Directory Password Authentication gives certificate issues. Error: "The certificate chain was issued by an authority that is not trusted."
Cannot connect to x.x.x.x.
===================================
A connection was successfully established with the server, but then an error occurred during the login process. (provider: SSL Provider, error: 0 - The certificate chain was issued by an authority that is not trusted.) (.Net SqlClient Data Provider)
------------------------------
For help, click: http://go.microsoft.com/fwlink?ProdName=Microsoft%20SQL%20Server&EvtSrc=MSSQLServer&EvtID=-2146893019&LinkId=20476 (page does not exist)
Oddly enough, if I go to the "options" settings at the login window and check the box "trust server certificate". I suddenly am NOT able to connect to the server and I simply get the error.
Cannot connect to x.x.x.x.
===================================
Login failed for user ''. (.Net SqlClient Data Provider)
Is the setup I want to achieve possible? And if so, how can I achieve it? :)
Recap: SQL Servers are running in AD domain, users have AD credentials but also need to be able to login from client computers NOT part of the AD domain with their AD credentials.