The RST packets in your capture are unrelated to all the other TCP connections seen in your capture. That makes it difficult to guess what may have triggered them. I see no evidence to suggest that the RST packets were triggered by other packets in your capture.
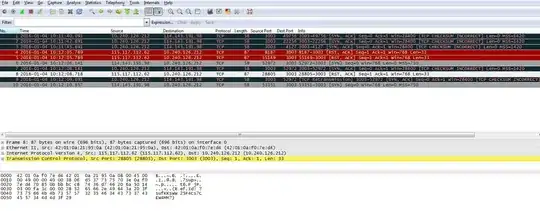
Unlike a normal RST packet, each RST packet in your capture also has a payload. The selected packet has this payload:
(Ref.Id: ?sufKKsWW25F4Cs7CEW4MM?)
This payload is the best hint so far about what may have caused those RST packets. Maybe if you capture traffic for a longer period of time you'll find out if the RST packets are related to a TCP connection which has been idle for a while.
Also check the logs on any middleboxes (NAT, firewall, etc.) for the string sufKKsWW25F4Cs7CEW4MM.
Searching for Ref.Id and RST leads to this older question about a firewall called Sonicwall NSA 2400. And from a quick look over the other search results it appears that the majority of them also mention Sonicwall. So it sounds like the RST packets are most likely produced by a Sonicwall firewall.