Check the audit policy subcategory setting. You should also use regedit and gpedit.msc to confirm the actual setting on the domain controller(s), in addition to GPMC.
Windows Settings > Security Settings > Local Policy > Security Options:
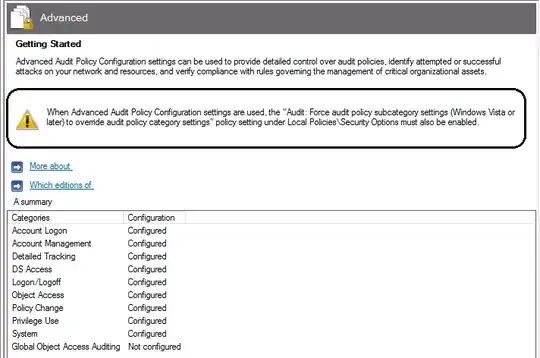
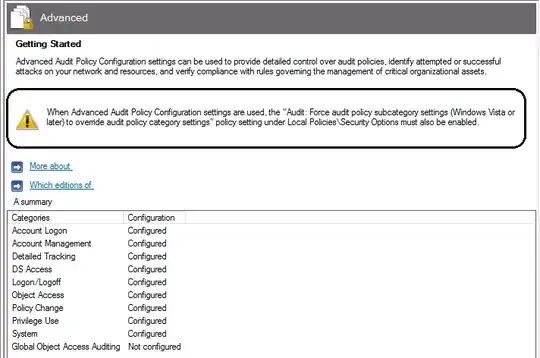
"Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings.
Windows Vista and later versions of Windows allow audit policy to be managed in a more precise way using audit policy subcategories. Setting audit policy at the category level will override the new subcategory audit policy feature. Group Policy only allows audit policy to be set at the category level, and existing group policy may override the subcategory settings of new machines as they are joined to the domain or upgraded to Windows Vista or later versions. To allow audit policy to be managed using subcategories without requiring a change to Group Policy, there is a new registry value in Windows Vista and later versions, SCENoApplyLegacyAuditPolicy, which prevents the application of category-level audit policy from Group Policy and from the Local Security Policy administrative tool.
If the category level audit policy set here is not consistent with the events that are currently being generated, the cause might be that this registry key is set.
Default: Enabled"