Right, Well I scripted it then.
I still believe that there is an easier way with certreq and powershell but here is the bash script.
Requirements: Cygwin, standard UNIX utilities, clip, openssl
#!/bin/bash
iexplore='/cygdrive/c/Program\ Files\ \(x86\)/Internet\ Explorer/iexplore.exe';
printf "\033c";
echo -e "This function automates IIS7 certificate generation for <YourCompany>";
type openssl > /dev/null 2>&1 || {
echo "Cannot find OpensSSL, it is required to generate certificates. Aborting..." 1>&2;
exit 1
};
openssl version;
echo -e "\n";
read -p "What is the server hostname (NOT FQDN!): " Hostname;
if [[ $Hostname =~ ^[A-Za-z0-9]+$ ]]; then
echo -e "Server name:\t"$Hostname"\nFQDN:\t\t"$Hostname".<yourDomain>\n";
else
echo ""$Hostname" doesn't look quite right... Exiting";
sleep 3;
exit 1;
fi;
mkdir ~/Desktop/certs_temp > /dev/null 2>&1;
cd ~/Desktop/certs_temp;
echo "
[ req ]
default_md = sha512
default_bits = 2048
default_keyfile = rui.key
distinguished_name = req_distinguished_name
encrypt_key = no
prompt = no
string_mask = nombstr
req_extensions = v3_req
input_password = testpassword
output_password = testpassword
[ v3_req ]
basicConstraints = CA:false
keyUsage = digitalSignature, keyEncipherment, dataEncipherment
extendedKeyUsage = serverAuth, clientAuth
subjectAltName = DNS:"$Hostname"
[ req_distinguished_name ]
countryName = AU
stateOrProvinceName = NSW
localityName = Sydney
0.organizationName = <OrgName>
organizationalUnitName = <OrgUName>
commonName = "$Hostname".<YourDomain>" > openssl.cfg;
openssl req -out openssl.csr -new -newkey rsa:2048 -nodes -keyout pk.key -config openssl.cfg > /dev/null 2>&1;
openssl rsa -in pk.key -out openssl.key > /dev/null 2>&1; rm pk.key;
echo -e "Now, upload this Code Signing Request to the Internal Certificate Authority: \n\t- The CSR content has been copied into your clipboard\n\t- You do not require to set any subject alternate name\n\t- Once submitted, open "Certificate Authority" via MMC (<ServerName>), issue pending certificate and export it (Open / Details / Copy To File) Base64 to ~/Desktop/certs_temp/openssl.cer\n";
eval $iexplore https://<ServerName>/certsrv/certrqxt.asp;
cat openssl.csr | clip;
read -p "Press [Enter] when openssl.cer certificate has been place in ~/Desktop/certs_temp";
if [ -f 'openssl.cer' ]; then
cat openssl.cer >> openssl.key;
echo '
-----BEGIN CERTIFICATE-----
<CompanyIntermediate>
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
<CompanyRoot>
-----END CERTIFICATE-----' >> openssl.key;
mv openssl.key ""$Hostname".pem";
echo "Converting PEM Chain certificate to PKCS#12 (.pfx)";
openssl pkcs12 -export -out ""$Hostname".pfx" -in ""$Hostname".pem";
explorer .
else
echo "Cannot find openssl.cer in ~/Desktop/certs_temp... Exiting";
sleep 3;
exit 1;
fi
The script :
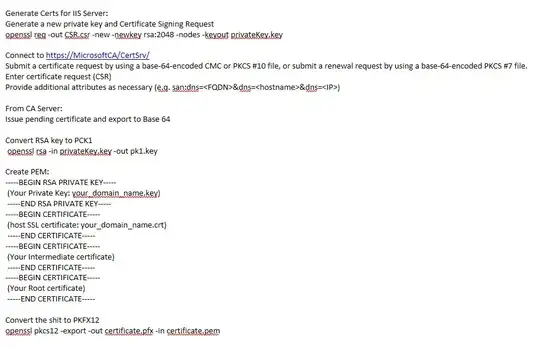
- Generates a private key and code signing request based on a config
file.
- Copies the CSR in the clipboard and open IIS webpage to
request the cert.
- Prompts the user for issuing the pending
certificate and export it base64
- Creates PEM, then export it as
PKCS#12 (.pfx)
Note: You have to change the path for Internet Explorer for Win 32bit and have to replace < ServerName > specific tags.