I want to confirm that the RDP certificate on the remote Win 10 machine matches what the client is using in case of MITM attacks - how do I do this?
So far other answers I have seen do not point me to the location of the same certificate as the one presented to my RDP client. Could this be because my client is set to NLA as the security option? if so, then where is the NLA certificate, if such a thing exists? I have searched on Google and can't find it.
Background
I'm using Remmina RDP client to connect via RDP from my home linux computer to a work Windows 10 machine. Today I received a notification that the certificate used on my Windows 10 work machine had changed. Presumably the old one had expired, but how does one confirm this - it appears as if the old certificate is deleted by the system. When I compared the cert RDP client displayed with that stored in my Win 10 work machine I could not find a match.
Other notes
- Remmina > Advnaced > Security : set to "NLA" (other options include TLS, RDP, Negotiate)
- eventvwr.msc > System > The latest (and only) cert change event here does not match the one presented to my RDP client
- certlm.msc > Remote Desktop > Certificates : likewise I cannot find same cert in here
Certificate Error/Warning :
The certificate changed! Details:
Subject: CN = my.machine.name
Issuer: CN = my.machine.name
Old fingerprint: c2:de:....
New fingerprint: 67:2f:....
Accept changed certificate?
Screenshots
[Update 1] Remmina RDP Client - notification regarding certificate change. The new cert fingerprint does not match the one stored on the computer I am connecting to, as can be seen in certlm and event viewer pictures below.
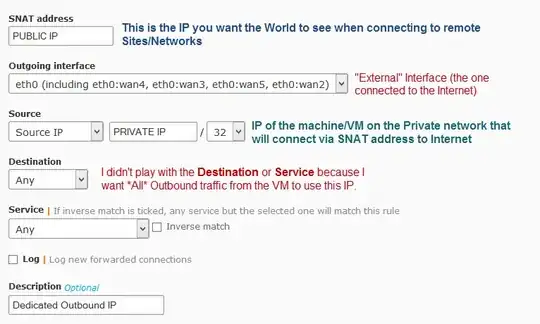
[Update 2] Event Viewer - RDP Cert changed recently on Windows 10 host
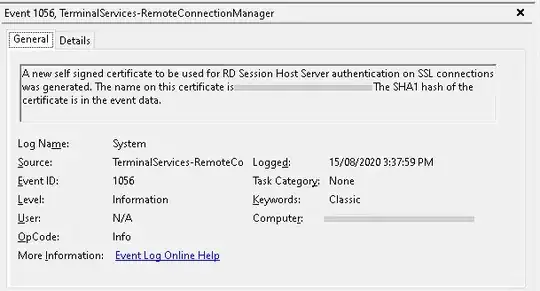

[Update 3] certlm.msc - Certificate manager for local machine. As you can see the fingerprint does not match the one presented to the client