I found a HTML injection vulnerability but there is an issue.
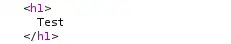
The following request returns the following:
curl "https://redacted.com/xss/para?meter="><h1>Test\</h1>"<meta name="url:url" content="https://redacted.com/xss/para?meter="><h1>Test\</h1>
....
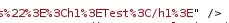
But when I try it on a browser it's automatically displaying https://redacted.com/xss/para?meter=%253E%253Ch1%253ETest%253C%2Fh1%253E and response returns the following:
\<meta name="url:url" content="https://redacted.com/xss/para?meter=%253E%253Ch1%253ETest%253C%2Fh1%253E" /\>
So we need to execute this HTML code on victim for an impact. Is there any way for bypass this?