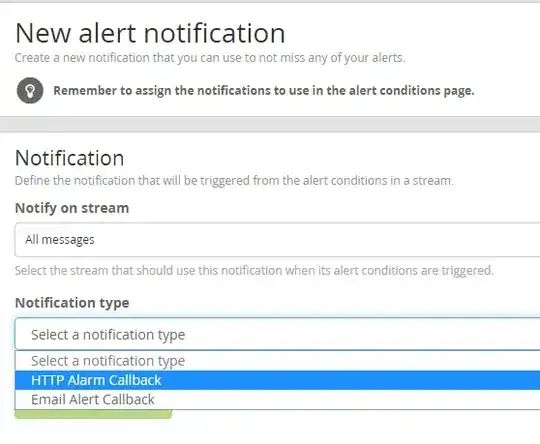
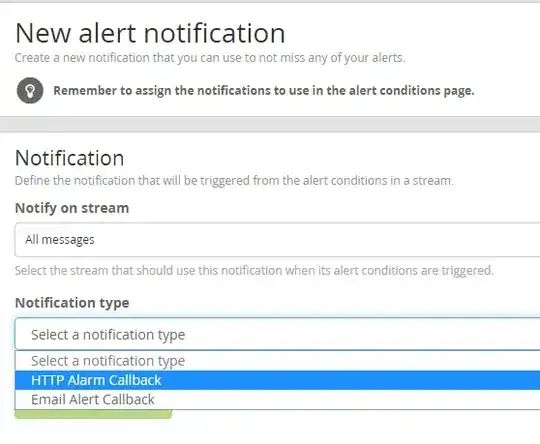
Graylog allows you to define alert triggers/Conditions and Actions/Notifications.
Out of the box it can do an HTTP POST to a nominated URL. I am not sure if parameterisation is available, but this might be enough to do what you need. The graylog marketplace (https://marketplace.graylog.org/) will have some more options which may allow more complex actions - so something may already be available.*
*(Depending on how much hair you have on your chest you can develop your own alert/notification plugin)
I am 99% sure ELK would offer this and even more than Graylog. My ELK experience is limited, but I suspect that Graylog is closest to the Logstash service in the ELK stack. Both use Elasticsearch, but Kibana provides a lot of features not really available in Graylog.
SIEM may also be able to do this, but SIEM's include a lot of pre-defined rule-sets to track anomalies across various sources and correlate and automatically raise security alerts. They generally allow extension of existing rule-sets and/or creating your own. They are almost always goliath systems with a strong learning curve. From what you're saying it seems like overkill.
If you go with SIEM or Centralised Logging - these things need a lot of "juice" (CPU, RAM and IO). If you simply want to deploy application logging, monitoring and alerting, Graylog would likely be the best option. Grab the OVA from the graylog site and have a play, move on to ELK if Graylog falls short and then look at the SIEM options.