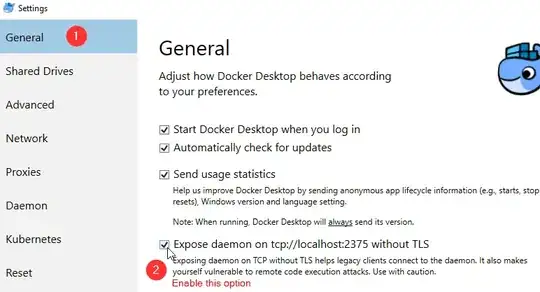
If you expose the Docker daemon without authentication (which is what that options does) then anyone who can make HTTP requests to localhost:2375 will be able to execute Docker commands on your host (the Docker daemon is a REST API so takes HTTP commands)
The consequences of that could be bad depending on the setup in question. For example an attacker could start a container which would connect back to a system controlled by them and allow access to your internal network.
An attacker could also start a container which maps in directories from the underlying host into the container that they control.
How probable these scenarios are, depends on your exact threat model, but that's the kind of thing that could occur.
As to mitigations, you can configure the Docker Daemon to use client certificate authentication via a TLS cert, some more information about setting that up here
Of course that might not work for whatever tooling your developer needs to use.
An alternative options (assuming that it's Linux containers under development rather than windows containers) is that you could use Visual Studio Code's ability to develop against a remote docker instance (more info here )