I live in a city where CCTV camera coverage is comprehensive and increasing. Cameras are getting cheaper and higher resolution. Everyone has a video camera in their pocket already, and we are starting to see trends which indicate always-on cameras may become commonplace in other devices like glasses.
It has occurred to me, when out in public and entering my username/password into apps on my phone and laptop, that if a camera could capture both my screen and my keyboard, it could be fairly straightforward for a viewer to grab or guess my credentials from the footage assuming a high enough resolution image and the view not being (too) obscured.
Without going too much into the details of how it would be implemented, the accuracy and cost etc, I have a background in image processing and so am also aware that this would likely be automatable to at least some degree.
So I thought I would ask the community here if this is actually a viable risk? Have there been any known instances of it happening already? Are people thinking about this with respect to the viability of plaintext credential entry into apps in the long run?
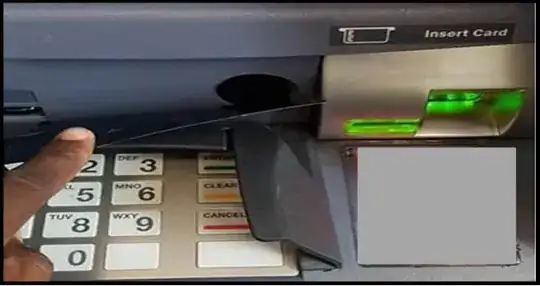 Hidden camera behind ATM faceplate (
Hidden camera behind ATM faceplate ( Hidden camera glued to corner of ATM (
Hidden camera glued to corner of ATM ( Hidden camera on fake panel of ATM (
Hidden camera on fake panel of ATM (