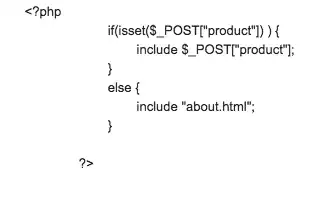
I wonder how to patch the LFI problem in this code? Please suggest a good way to patch this vulnerability.
Asked
Active
Viewed 273 times
-1
-
3[Do not post an image of text. That's rude. Copy-paste the text.](https://unix.meta.stackexchange.com/questions/4086/psa-please-dont-post-images-of-text) – Gilles 'SO- stop being evil' Oct 25 '18 at 19:38
-
This is not something to "patch". You have a design pattern issue. There are multiple tested design patterns for how to process user input to display a valid page. – schroeder Oct 26 '18 at 15:59
-
Is this from a homework assignment or textbook? – schroeder Oct 26 '18 at 16:04
1 Answers
2
Directory traversal/local file inclusion attacks are just a symptom of the problem of failing to validate user input. Consider what you're doing: You're taking input from the Internet and blinding passing it to a function that expects a very particular type of input.
The short answer is: VALIDATE ALL USER INPUT.
The longer answer is, and in this case, verify that what is being POSTed in the Product variable is a legitimate file name in the appropriate directory.
This same premise is how SQL Injection works.
thepip3r
- 633
- 3
- 8