When I have manipulated the URI of an application with some SQL or XSS payloads I am able to see a runtime error page. Can we come to a conclusion that the application is vulnerable to SQL Injection or XSS attacks.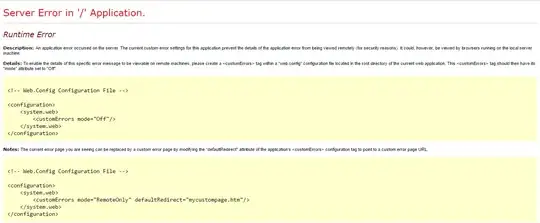
Please Suggest
When I have manipulated the URI of an application with some SQL or XSS payloads I am able to see a runtime error page. Can we come to a conclusion that the application is vulnerable to SQL Injection or XSS attacks.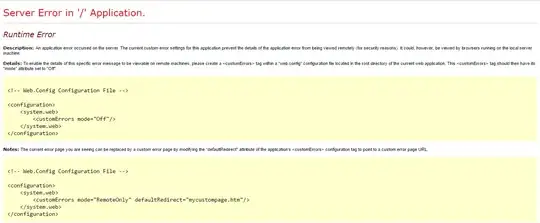
Please Suggest
Can we come to a conclusion that the application is vulnerable to SQL Injection or XSS attacks.
Why would you think so?
If the injected XSS payload is not shown, there is no XSS vulnerability (at least not reflected; we cannot say anything about persistent).
We cannot say anything about SQL injection. There may or may not be one, the presence of an error message doesn't tell either way, you need to perform further tests (and enable error messages if you can).
The fact that you get a generic error message only tells you that your request was invalid, but not why. It could be that the application expected an integer but got a string, and thus shows an error (this is how it should be). It could also be that you injected into a query and broke it, and thus got an error message (this shouldn't happen), or it may be a number of different issues.