They might do it already, there is a known technique to dedicate malicious and powerful nodes to the network to be able to take control of some of the traffic.
Tor does not advertise itself to be able to protect against adversaries that have control over a fair part of the internet. While there are techniques to check the validity of the nodes if you have control over the internet(a fair part of the network) you can de-anonymize nodes.
Under Tor's website, the FAQ page :
What attacks remain against onion routing?
it is possible for an observer who can view both you and either the destination website or your Tor exit node to correlate timings of your traffic as it enters the Tor network and also as it exits. Tor does not defend against such a threat model.
In a more limited sense, note that if a censor or law enforcement agency has the ability to obtain specific observation of parts of the network, it is possible for them to verify a suspicion that you talk regularly to your friend by observing traffic at both ends and correlating the timing of only that traffic. Again, this is only useful to verify that parties already suspected of communicating with one another are doing so. In most countries, the suspicion required to obtain a warrant already carries more weight than timing correlation would provide.
Furthermore, since Tor reuses circuits for multiple TCP connections, it is possible to associate non anonymous and anonymous traffic at a given exit node, so be careful about what applications you run concurrently over Tor. Perhaps even run separate Tor clients for these applications.
About Tor network takedown:
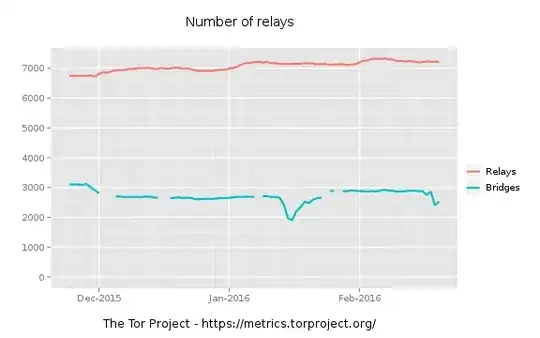
They may not have enough incentives to block the whole system. After all it's a highly decentralized, international network of nodes. If you shut down a node, another one will pop up so it's not trivial to take the whole thing down.
There are also obfuscation techniques Tor uses to hide itself from ISPs and censorship systems. They can't flip a switch and then Tor is down.
About adding malicious nodes to decrypt the traffic, it's not trivial either. You don't need any relay node, you need an exit node to get access to unencrypted traffic (Another layer of encryption may still be present, e.g. HTTPS). Tor also monitors exit nodes for malicious activity and actively blocks them. I'm not saying your provided scenario is not possible, I'm just saying it's not trivial.