Operations security
Operations security (OPSEC) is a process that identifies critical information to determine if friendly actions can be observed by enemy intelligence, determines if information obtained by adversaries could be interpreted to be useful to them, and then executes selected measures that eliminate or reduce adversary exploitation of friendly critical information.
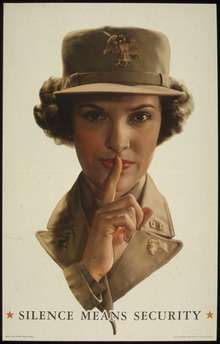
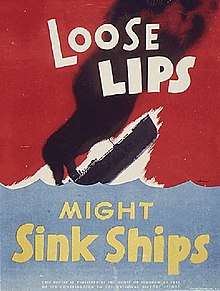
In a more general sense, OPSEC is the process of protecting individual pieces of data that could be grouped together to give the bigger picture (called aggregation). OPSEC is the protection of critical information deemed mission-essential from military commanders, senior leaders, management or other decision-making bodies. The process results in the development of countermeasures, which include technical and non-technical measures such as the use of email encryption software, taking precautions against eavesdropping, paying close attention to a picture you have taken (such as items in the background), or not talking openly on social media sites about information on the unit, activity or organization's Critical Information List.
The term "operations security" was coined by the United States military during the Vietnam War.
Process
OPSEC is a five-step iterative process that assists an organization in identifying specific pieces of information requiring protection and employing measures to protect them:
- Identification of Critical information: Critical information is information about friendly intentions, capabilities and activities that allow an adversary to plan effectively to disrupt their operations. U.S. Army Regulation 530-1 has redefined Critical Information into four broad categories, using the acronym CALI – Capabilities, Activities, Limitations (including vulnerabilities), and Intentions.[1] This step results in the creation of a Critical Information List (CIL). This allows the organization to focus resources on vital information, rather than attempting to protect all classified or sensitive unclassified information. Critical information may include, but is not limited to, military deployment schedules, internal organizational information, details of security measures, etc.
- Analysis of Threats: A Threat comes from an adversary – any individual or group that may attempt to disrupt or compromise a friendly activity. Threat is further divided into adversaries with intent and capability. The greater the combined intent and capability of the adversary, the greater the threat. This step uses multiple sources, such as intelligence activities, law enforcement, and open source information to identify likely adversaries to a planned operation and prioritize their degree of threat.
- Analysis of Vulnerabilities: Examining each aspect of the planned operation to identify OPSEC indicators that could reveal critical information and then comparing those indicators with the adversary's intelligence collection capabilities identified in the previous action. Threat can be thought of as the strength of the adversaries, while vulnerability can be thought of as the weakness of friendly organizations.
- Assessment of Risk: First, planners analyze the vulnerabilities identified in the previous action and identify possible OPSEC measures for each vulnerability. Second, specific OPSEC measures are selected for execution based upon a risk assessment done by the commander and staff. Risk is calculated based on the probability of Critical Information release and the impact if such as release occurs. Probability is further subdivided into the level of threat and the level of vulnerability. The core premise of the subdivision is that the probability of compromise is greatest when the threat is very capable and dedicated, while friendly organizations are simultaneously exposed.
- Application of Appropriate OPSEC Measures: The command implements the OPSEC measures selected in the assessment of risk action or, in the case of planned future operations and activities, includes the measures in specific OPSEC plans. Countermeasures must be continually monitored to ensure that they continue to protect current information against relevant threats.[2] The U.S. Army Regulation 530-1[3] refers to "Measures" as the overarching term, with categories of "Action Control" (controlling one's own actions); "Countermeasures" (countering adversary intelligence collection); and "Counteranalysis" (creating difficulty for adversary analysts seeking to predict friendly intent) as tools to help an OPSEC professional protect critical information.
An OPSEC Assessment is the formal application of the process to an existing operation or activity by a multidisciplinary team of experts. The assessments identify the requirements for additional OPSEC measures and required changes to existing ones.[4] Additionally, OPSEC planners, working closely with Public Affairs personnel, must develop the Essential Elements of Friendly Information (EEFI) used to preclude inadvertent public disclosure of critical or sensitive information.[5] The term "EEFI" is being phased out in favor of "Critical Information", so all affected agencies use the same term, minimizing confusion.
History
Vietnam
In 1966, United States Admiral Ulysses Sharp established a multidisciplinary security team to investigate the failure of certain combat operations during the Vietnam War. This operation was dubbed Operation Purple Dragon, and included personnel from the National Security Agency and the Department of Defense.[6]
When the operation concluded, the Purple Dragon team codified their recommendations. They called the process "Operations Security" in order to distinguish the process from existing processes and ensure continued inter-agency support.[7]
NSDD 298
In 1988, President Ronald Reagan signed National Security Decision Directive (NSDD) 298. This document established the National Operations Security Program and named the Director of the National Security Agency as the executive agent for inter-agency OPSEC support. This document also established the Interagency OPSEC Support Staff (IOSS).[8]
International and private-sector application
Although originally developed as a US military methodology, Operations Security has been adopted worldwide for both military and private-sector operations. In 1992, the North Atlantic Treaty Organization (NATO) added OPSEC to its glossary of terms and definitions.[9]
The private sector has also adopted OPSEC as a defensive measure against competitive intelligence collection efforts.[10]
Military and private-sector security and information firms often require OPSEC professionals. Certification is often initially obtained from military or governmental organizations, such as:
Other measures that impact OPSEC
- Communications security (COMSEC)
- Counter-intelligence (CI)
- Information security (INFOSEC)
- Signal security (SIGSEC)
- Transmission security (TRANSEC)
- Cybersecurity
See also
| Wikimedia Commons has media related to Anti-rumor propaganda. |
- For Official Use Only – FOUO
- Information security
- Intelligence cycle security
- Security
- Security Culture
- Sensitive but unclassified – SBU
- Controlled Unclassified Information - CUI
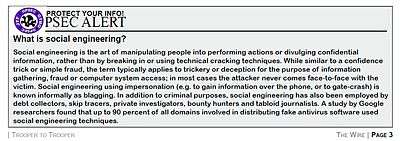
- Social engineering
References
- https://fas.org/irp/doddir/army/ar530-1.pdf
- "The OPSEC Process". The Operations Security Professional's Association. Retrieved April 12, 2011.
- https://fas.org/irp/doddir/army/ar530-1.pdf
- "OPSEC Glossary of Terms". Interagency OPSEC Support Staff. Retrieved June 16, 2016.
- "Joint Operation Planning Process and Public Affairs Actions" (PDF). Defense Technical Information Center (DTIC). Archived from the original (PDF) on 2016-08-08. Retrieved June 16, 2016.
- "PURPLE DRAGON: The Formations of OPSEC". Information Assurance Directorate. National Security Agency. Retrieved June 15, 2016.
- "The Origin of OPSEC- from the dragon's mouth". www.opsecprofessionals.org. Retrieved 2016-06-16.
- "About the IOSS". National OPSEC Program. Interagency OPSEC Support Staff. Retrieved June 15, 2016.
- "NATO Glossary of Terms and Definitions" (PDF). AAP-6. NATO. Retrieved June 16, 2016.
- Kahaner, Larry (1997). Competitive Intelligence. Simon & Schuster. pp. 252–255.
- "Army OPSEC Support Element (OSE) Training". 1stiocmd.army.mil. Ft. Belvoir, VA: 1st Information Operations Command. Retrieved June 20, 2018.
- "Naval Operations Security Support Team". Navy.mil. Washington, DC: U.S. Navy. Retrieved June 20, 2018.
- "The Marine Corps Operations Security (OPSEC) Program". Marines.mil. Washington, DC: U.S. Marine Corps. Retrieved June 20, 2018.
- "Air Force OPSEC Support Team". Washington, DC: U.S. Air Force. Retrieved June 20, 2018 – via Facebook.com./
- Commandant of the Coast Guard (April 22, 2014). Commandant Instruction M5510.24A, Operations Security (OPSEC) Program (PDF). Washington, DC: U.S. Coast Guard. p. 1.
- "JIOWC OPSEC Support". Lackland Air Force Base: U.S. Joint Information Operations Warfare Center. Retrieved June 20, 2018 – via Facebook.com.
- "National OPSEC Program". iad.gov/ioss/. Ft. George G. Meade, MD: Interagency OPSEC Support Staff (IOSS). Retrieved June 20, 2018.
External links
- Espionage Target You - DoD Film on Operational Security on YouTube
- U.S. Government OPSEC site
- Operations Security Professionals Association
- National Security Decision Directive 298
- Purple Dragon, The Origin & Development of the United States OPSEC Program, NSA, 1993.
- Operations Security (JP 3-13.3) PDF U.S. DoD Operations Security Doctrine.
- "Bin Laden Trail 'Stone Cold'". Washington Post. September 10, 2006.
- "After a Decade at War With West, Al-Qaeda Still Impervious to Spies". Washington Post. March 20, 2008.
- How to Conduct an OPSEC Assessment