ID-based encryption
ID-based encryption, or identity-based encryption (IBE), is an important primitive of ID-based cryptography. As such it is a type of public-key encryption in which the public key of a user is some unique information about the identity of the user (e.g. a user's email address). This means that a sender who has access to the public parameters of the system can encrypt a message using e.g. the text-value of the receiver's name or email address as a key. The receiver obtains its decryption key from a central authority, which needs to be trusted as it generates secret keys for every user.
ID-based encryption was proposed by Adi Shamir in 1984.[1] He was however only able to give an instantiation of identity-based signatures. Identity-based encryption remained an open problem for many years.
The pairing-based Boneh–Franklin scheme[2] and Cocks's encryption scheme[3] based on quadratic residues both solved the IBE problem in 2001.
Usage
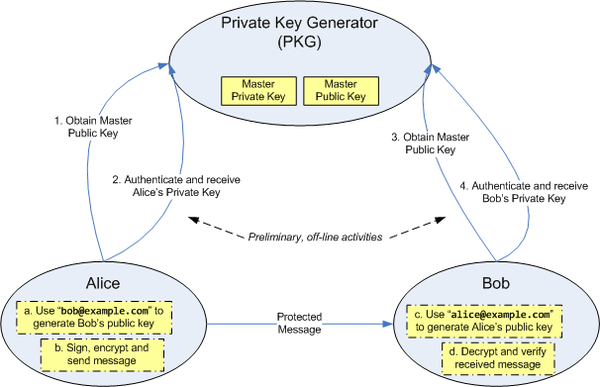
Identity-based systems allow any party to generate a public key from a known identity value such as an ASCII string. A trusted third party, called the Private Key Generator (PKG), generates the corresponding private keys. To operate, the PKG first publishes a master public key, and retains the corresponding master private key (referred to as master key). Given the master public key, any party can compute a public key corresponding to the identity by combining the master public key with the identity value. To obtain a corresponding private key, the party authorized to use the identity ID contacts the PKG, which uses the master private key to generate the private key for identity ID.
As a result, parties may encrypt messages (or verify signatures) with no prior distribution of keys between individual participants. This is extremely useful in cases where pre-distribution of authenticated keys is inconvenient or infeasible due to technical restraints. However, to decrypt or sign messages, the authorized user must obtain the appropriate private key from the PKG. A caveat of this approach is that the PKG must be highly trusted, as it is capable of generating any user's private key and may therefore decrypt (or sign) messages without authorization. Because any user's private key can be generated through the use of the third party's secret, this system has inherent key escrow. A number of variant systems have been proposed which remove the escrow including certificate-based encryption,[4] secure key issuing cryptography[5] and certificateless cryptography.[6]
The steps involved are depicted in this diagram:
Protocol framework
Dan Boneh and Matthew K. Franklin defined a set of four algorithms that form a complete IBE system:
- Setup: This algorithm is run by the PKG one time for creating the whole IBE environment. The master key is kept secret and used to derive users' private keys, while the system parameters are made public. It accepts a security parameter (i.e. binary length of key material) and outputs:
- A set of system parameters, including the message space and ciphertext space and ,
- a master key .
- Extract: This algorithm is run by the PKG when a user requests his private key. Note that the verification of the authenticity of the requestor and the secure transport of are problems with which IBE protocols do not try to deal. It takes as input , and an identifier and returns the private key for user .
- Encrypt: Takes , a message and and outputs the encryption .
- Decrypt: Accepts , and and returns .
Correctness constraint
In order for the whole system to work, one has to postulate that:
Encryption schemes
The most efficient identity-based encryption schemes are currently based on bilinear pairings on elliptic curves, such as the Weil or Tate pairings. The first of these schemes was developed by Dan Boneh and Matthew K. Franklin (2001), and performs probabilistic encryption of arbitrary ciphertexts using an Elgamal-like approach. Though the Boneh-Franklin scheme is provably secure, the security proof rests on relatively new assumptions about the hardness of problems in certain elliptic curve groups.
Another approach to identity-based encryption was proposed by Clifford Cocks in 2001. The Cocks IBE scheme is based on well-studied assumptions (the quadratic residuosity assumption) but encrypts messages one bit at a time with a high degree of ciphertext expansion. Thus it is highly inefficient and impractical for sending all but the shortest messages, such as a session key for use with a symmetric cipher.
A third approach to IBE is through the use of lattices.
Identity-based encryption algorithms
The following lists practical identity-based encryption algorithms
- Boneh–Franklin (BF-IBE).
- Sakai–Kasahara (SK-IBE).[7]
- Boneh–Boyen (BB-IBE).[8]
All these algorithms have security proofs.
Advantages
One of the major advantages of any identity-based encryption scheme is that if there are only a finite number of users, after all users have been issued with keys the third party's secret can be destroyed. This can take place because this system assumes that, once issued, keys are always valid (as this basic system lacks a method of key revocation). The majority of derivatives of this system which have key revocation lose this advantage.
Moreover, as public keys are derived from identifiers, IBE eliminates the need for a public key distribution infrastructure. The authenticity of the public keys is guaranteed implicitly as long as the transport of the private keys to the corresponding user is kept secure (authenticity, integrity, confidentiality).
Apart from these aspects, IBE offers interesting features emanating from the possibility to encode additional information into the identifier. For instance, a sender might specify an expiration date for a message. He appends this timestamp to the actual recipient's identity (possibly using some binary format like X.509). When the receiver contacts the PKG to retrieve the private key for this public key, the PKG can evaluate the identifier and decline the extraction if the expiration date has passed. Generally, embedding data in the ID corresponds to opening an additional channel between sender and PKG with authenticity guaranteed through the dependency of the private key on the identifier.
Drawbacks
- If a Private Key Generator (PKG) is compromised, all messages protected over the entire lifetime of the public-private key pair used by that server are also compromised. This makes the PKG a high-value target to adversaries. To limit the exposure due to a compromised server, the master private-public key pair could be updated with a new independent key pair. However, this introduces a key-management problem where all users must have the most recent public key for the server.
- Because the Private Key Generator (PKG) generates private keys for users, it may decrypt and/or sign any message without authorization. This implies that IBS systems cannot be used for non-repudiation. This may not be an issue for organizations that host their own PKG and are willing to trust their system administrators and do not require non-repudiation.
- The issue of implicit key escrow does not exist with the current PKI system, wherein private keys are usually generated on the user's computer. Depending on the context key escrow can be seen as a positive feature (e.g., within Enterprises). A number of variant systems have been proposed which remove the escrow including certificate-based encryption, secret sharing, secure key issuing cryptography and certificateless cryptography.
- A secure channel between a user and the Private Key Generator (PKG) is required for transmitting the private key on joining the system. Here, a SSL-like connection is a common solution for a large-scale system. It is important to observe that users that hold accounts with the PKG must be able to authenticate themselves. In principle, this may be achieved through username, password or through public key pairs managed on smart cards.
- IBE solutions may rely on cryptographic techniques that are insecure against code breaking quantum computer attacks (see Shor's algorithm)
See also
References
- Adi Shamir, Identity-Based Cryptosystems and Signature Schemes. Advances in Cryptology: Proceedings of CRYPTO 84, Lecture Notes in Computer Science, 7:47--53, 1984
- Dan Boneh, Matthew K. Franklin, Identity-Based Encryption from the Weil Pairing Advances in Cryptology - Proceedings of CRYPTO 2001 (2001)
- Clifford Cocks, An Identity Based Encryption Scheme Based on Quadratic Residues, Proceedings of the 8th IMA International Conference on Cryptography and Coding, 2001
- Craig Gentry Certificate-Based Encryption and the Certificate Revocation Problem Advances in Cryptology - Proceedings of EUROCRYPT 2003 (2003)
- Lee, Byoungcheon; Boyd, Colin; Dawson, Ed; Kim, Kwangjo; Yang, Jeongmo; Yoo, Seungjae (2004). Secure Key Issuing in ID-based Cryptography. ACS Conferences in Research and Practice in Information Technology - Proceedings of the Second Australian Information Security Workshop-AISW 2004. CiteSeerX 10.1.1.6.337.
- SS Al-Riyami, KG Paterson Certificateless Public Key Cryptography Advances in Cryptology - Proceedings of ASIACRYPT 2003 (2003)
- Sakai, Ryuichi; Kasahara, Masao (2003). "ID Based cryptosystems with pairing on elliptic curve" (PDF). Cryptography ePrint Archive. 2003/054.
- Boneh, Dan; Boyen, X (2004). "Efficient selective-ID secure identity based encryption without random oracles". LNCS. Advances in Cryptography - EUROCRYPT 2004. Springer-Verlag. 3027: 223–238. doi:10.1007/978-3-540-24676-3_14. ISBN 978-3-540-21935-4.
External links
- Seminar 'Cryptography and Security in Banking'/'Alternative Cryptology', Ruhr University Bochum, Germany
- RFC 5091 - the IETF RFC defining two common IBE algorithms
- HP Role-Based Encryption
- The Pairing-Based Crypto Lounge
- The Voltage Security Network - IBE encryption web service
- Analyst report on the cost of IBE versus PKI