Copy detection pattern
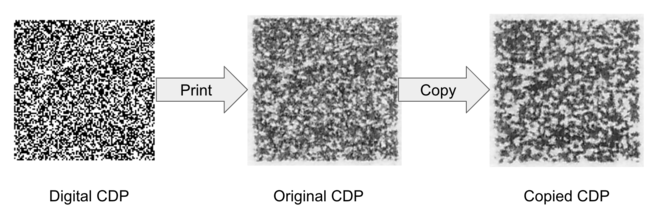
A copy detection pattern (CDP),[1] secure graphic[2] or graphical code[3][4] is a small random or pseudo-random digital image which is printed on documents, labels or products for counterfeit detection. Authentication is made by scanning the printed CDP using an image scanner or mobile phone camera.
The detection of counterfeits using a CDP relies on an "information loss principle",[1] which states that every time a digital image is printed or scanned, some information is lost about the original digital image. A CDP is a maximum entropy image that attempts to take advantage of this information loss. Since producing a counterfeit CDP requires an additional scanning and printing processes, it will have less information than an original CDP. By measuring the information in the scanned CDP, the detector can determine whether the CDP is an original print or a copy.
CDPs aim to address limitations of optical security features such as security holograms. They are motivated by the need for security features that can be originated, managed and transferred digitally, and that are machine readable.[1] Contrarily to many traditional security printing techniques, CDPs do not rely on Security by Obscurity,[5] as the algorithm for generating CDPs can be public as long as the key used to generate it or the digital CDP is not revealed.[6]
CDPs have also been described as a type of optical physical unclonable function.[3]
Security
The theoretical and practical assessment of the security level of CDPs, in other words the detector's ability to detect counterfeit attempts, is an ongoing area of research:
- In,[6] practical recommendations on printing stability, taking into account scanning quality of the detector, and managing the security of printing facilities.
- In,[7] a decision theoretic-model to determine optimality properties of CDPs and under an additive Gaussian noise assumption for the print channel and an optimal showed that the optimal decision function is a correlator.
- In,[8] different new CDP detection metrics are proposed and confirmed a significant improvement of copy detection accuracy.
- In,[9] the impact of multiple printed observations of the same CDP is studied, and it is shown that the noise due to the printing process can be reduced but not completely removed, due to deterministic printing artefacts.
- In,[10] a theoretical comparison is made between the performance of CDPs and natural randomness.
- In [11] and,[12] deep learning methods are used to recover portions of the digital CDP, and it is shown that these can be used to launch clonability attacks.
- In,[13] quality control challenges are reviewed, and an inline verification system of secure graphics is proposed for high security printing applications.
- In,[14] different attack methods based on restoration of the scanned CDP are tested. and show that a classifier based on support vector domain description outperforms other classification methods.
Applications
CDPs are used for different physical item authentication applications:
- As a means of providing a product authentication service using the Internet of Things.[15]
- For securing identification documents, in combination with digital watermarks and 2D barcodes.[5] They were used in 2006 to protect identification badges during the FIFA World Cup.[16][17]
- Integrated into QR Codes to enable consumers to check product authenticity with a smartphone application.[18]
- For authenticating pharmaceutical packaging.[19]
Related techniques
The EURion constellation and digital watermarks are inserted into banknotes to be detected by scanners, photocopiers and image processing software. However the objective of these techniques is not to detect whether a given banknote is a counterfeit, but to deter amateur counterfeiters from reproducing banknotes by blocking the device or software used to make the counterfeit.[20]
Digital watermarks can may be used as well to differentiate original prints from counterfeits.[21][22] A digital watermark may also be inserted into a 2D barcode.[23] The fundamental difference between digital watermarks and CDPs is that a digital watermark must be embedded into an existing image while respecting a fidelity constraint, while the CDP does not have such constraint.[24]
References
- Picard, Justin (2004-06-03). Van Renesse, Rudolf L (ed.). "Digital authentication with copy-detection patterns". Optical Security and Counterfeit Deterrence Techniques V. SPIE. 5310: 176. Bibcode:2004SPIE.5310..176P. doi:10.1117/12.528055.
- Morris, Nicky (2018-08-17). "ScanTrust's anti-counterfeit solution isn't just about blockchain". Ledger Insights - enterprise blockchain. Retrieved 2020-04-20.
- Phan Ho, Anh Thu; Mai Hoang, Bao An; Sawaya, Wadih; Bas, Patrick (2014-06-05). "Document authentication using graphical codes: reliable performance analysis and channel optimization". EURASIP Journal on Information Security. 2014 (1): 9. doi:10.1186/1687-417X-2014-9. ISSN 1687-417X.
- Tkachenko, Iuliia; Puech, William; Destruel, Christophe; Strauss, Olivier; Gaudin, Jean-Marc; Guichard, Christian (2016-03-01). "Two-Level QR Code for Private Message Sharing and Document Authentication". IEEE Transactions on Information Forensics and Security. 11 (3): 571–583. doi:10.1109/TIFS.2015.2506546. ISSN 1556-6021.
- Picard, Justin; Vielhauer, Claus; Thorwirth, Niels (2004-06-22). Delp Iii, Edward J; Wong, Ping W (eds.). "Towards fraud-proof ID documents using multiple data hiding technologies and biometrics". Security, Steganography, and Watermarking of Multimedia Contents VI. SPIE. 5306: 416. Bibcode:2004SPIE.5306..416P. doi:10.1117/12.525446.
- Picard, Justin (2008). "Copy Detectable Images: From Theory to Practice". Conference on Optical Security and Counterfeit Deterrence 2008. 1: 372–381 – via Reconnaissance International.
- Picard, Justin (2008). "On the Security of Copy Detectable Images". NIP & Digital Fabrication Conference, 2008 International Conference on Digital Printing Technologies.
- Dirik, A. E.; Haas, B. (2012-11-01). "Copy detection pattern-based document protection for variable media". IET Image Processing. 6 (8): 1102–1113. doi:10.1049/iet-ipr.2012.0297. ISSN 1751-9667.
- Baras, Cleo; Cayre, François (2012-08-01). "2D bar-codes for authentication: A security approach". 2012 Proceedings of the 20th European Signal Processing Conference (EUSIPCO): 1760–1766.
- Voloshynovskiy, Slava; Holotyak, Taras; Bas, Patrick (2016-03-01). "Physical object authentication: Detection-theoretic comparison of natural and artificial randomness" (PDF). 2016 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP). IEEE: 2029–2033. doi:10.1109/icassp.2016.7472033. ISBN 978-1-4799-9988-0.
- Taran, Olga; Bonev, Slavi; Voloshynovskiy, Slava (2019-03-18). "Clonability of anti-counterfeiting printable graphical codes: a machine learning approach". arXiv:1903.07359 [cs.CR].
- Yadav, Rohit; Tkachenko, Iuliia; Trémeau, Alain; Fournel, Thierry (2019). "Estimation of Copy-sensitive Codes Using a Neural Approach" (PDF). Proceedings of the ACM Workshop on Information Hiding and Multimedia Security - IH&MMSec'19. New York, New York, USA: ACM Press: 77–82. doi:10.1145/3335203.3335718. ISBN 978-1-4503-6821-6.
- Picard, Justin; Khatri, Nick; 100% Inline Verification of Secure Graphics at High Resolution; 2019-05-15; Digital Document Security;,Reconnaissance International
- Zhang, Pei; Zhang, Weiming; Yu, Nenghai (April 2019). "Copy Detection Pattern-Based Authentication for Printed Documents with Multi-Dimensional Features". 2019 7th International Conference on Information, Communication and Networks (ICICN). IEEE. doi:10.1109/icicn.2019.8834939. ISBN 978-1-7281-0425-6.
- Chaves, Leonardo W. F.; Nochta, Zoltán (2010-07-12), "Breakthrough Towards the Internet of Things", Unique Radio Innovation for the 21st Century, Springer Berlin Heidelberg, pp. 25–38, Bibcode:2010urif.book...25C, doi:10.1007/978-3-642-03462-6_2, ISBN 978-3-642-03461-9
- Yumpu.com. "FIFA World Cup Case Study - Code Corporation". yumpu.com. Retrieved 2020-04-19.
- "Pattern makes 2D barcodes copy-proof". www.securingindustry.com. 2009-07-15. Retrieved 2020-04-19.
- Carron. "Combatting counterfeiting using QR codes".
- "Digital and Analog Technologies for Product Authentication and Tamper Evidence". Packaging Europe. 2019-03-28. Retrieved 2020-04-23.
- "Software Detection of Currency // Dr Steven J. Murdoch". murdoch.is. Retrieved 2020-04-23.
- Mahmoud, Khaled W.; Blackledge, Jonathon M.; Datta, Sekharjit; Flint, James A. (2004-06-22). Delp Iii, Edward J; Wong, Ping W (eds.). "Print protection using high-frequency fractal noise". Security, Steganography, and Watermarking of Multimedia Contents VI. SPIE. 5306: 446. Bibcode:2004SPIE.5306..446M. doi:10.1117/12.526677.
- Zhou, Jifeng; Pang, Mingyong (September 2010). "Digital watermark for printed materials". 2010 2nd IEEE InternationalConference on Network Infrastructure and Digital Content. IEEE: 758–762. doi:10.1109/icnidc.2010.5657884. ISBN 978-1-4244-6851-5.
- Nguyen, Hoai Phuong; Retraint, Florent; Morain-Nicolier, Frédéric; Delahaies, Angès (2019). "A Watermarking Technique to Secure Printed Matrix Barcode—Application for Anti-Counterfeit Packaging". IEEE Access. 7: 131839–131850. doi:10.1109/ACCESS.2019.2937465. ISSN 2169-3536.
- Barni, Mauro; Cox, Ingemar; Kalker, Ton; Kim, Hyoung-Joong, eds. (2005). "Digital Watermarking". Lecture Notes in Computer Science. 3710. doi:10.1007/11551492. ISBN 978-3-540-28768-1. ISSN 0302-9743.
External links
- Database of CDPs from the University of St-Etienne (for academic use only)
- Database of CDPs from University of Geneva