2
We have a Windows 2012 R2 RDS running as a virtual machine. From time to time, no specific shedule identifiable, a user session will be redirected to a temporary profile.
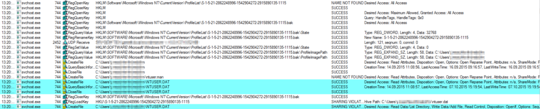
Whenever this happens we can observe a sharing violation on NTUSER.DAT on User loggon. I have added a screenshot of the ProcMon Output and blurred user names and IP-adresses for privacy reasons. All output on this screenshot is regarding the same user.
The issue is solved after the server is rebooted and all users can login just fine until this happens again. There are no handles on the users NTUSER.DAT file when he is not logged on, so no other process is locking the file in the background - it first gets opened / used when the user logs on to the server via RDP.
When the session is redirected we get the following output on "whoami" and "set":
C:\Windows\System32>whoami
domain\user
C:\Windows\System32>set
ALLUSERSPROFILE=C:\ProgramData
APPDATA=C:\Users\TEMP\AppData\Roaming
HOMEPATH=\Users\TEMP
LOCALAPPDATA=C:\Users\TEMP\AppData\Local
TEMP=C:\Users\TEMP\AppData\Local\Temp\3
TMP=C:\Users\TEMP\AppData\Local\Temp\3
USERDNSDOMAIN=domain.LOCAL
USERDOMAIN=domain
USERDOMAIN_ROAMINGPROFILE=domain
USERNAME=user
USERPROFILE=C:\Users\TEMP
Again, I replaced the domain and user name.
Rebooting the server when this problem occurs is not an option since there are other users logged on to this remote desktop server, who have not yet encountered this problem.
What is the best way to get a clue on why there is a sharing violation at logon?
Can you please send us some more details to hueiwang﹫microsoft.com, catalda﹫microsoft.com and niraja﹫microsoft.com - we are engineers working on this and will be in touch with you to try to set up a repro. Thanks! – cdavid – 2015-10-22T16:56:20.753
Hi David, what details exactly are you interessted in? As I said, we cannot reproduce this issue on purpose and it happens only every 2-3 weeks, but next time it happens I will collect all the data you need. – HannesS – 2015-10-26T08:23:00.440
I am reaching out to my colleagues to ask for detailed steps to gather logs. – cdavid – 2015-10-26T22:29:01.970
Did you get any information in what logs to collect? – HannesS – 2015-11-03T21:18:51.623
1We would need traces from sessenv, winlogon, sdclient, tssdjet, terminal services. For winlogon:
reg add HKLM\System\CurrentControlSet\Control\Winlogon /v TracingControlLevel /t REG_DWORD /d 0xffffffff. For TS:HKLM\System\CurrentControlSet\Control\Terminal Server\Debug REG_DWORD 0x1andHKLM\System\CurrentControlSet\Control\Terminal Server\DebugFlags REG_DWORD 0xFFFFFFFFandHKLM\System\CurrentControlSet\Control\Terminal Server\DebugLevel REG_DWORD 0xFFFFFFFF. – cdavid – 2015-11-03T22:17:11.0501The winlogon trace is
umstart*.etlatc:\windowsorc:\windows\system32. For TS, trace is atC:\Windows\System32\LogFiles\WMI\*terminal-service*.etl– cdavid – 2015-11-03T22:18:07.550Possible duplicate of Using temp roaming profile in windows 7 after removing local directory
– Ramhound – 2017-01-18T16:24:35.973