3
1
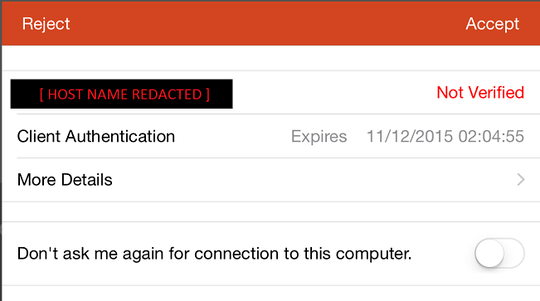
Currently I'm using a desktop machine running Windows 7 Ultimate x64. Also have configured it to enable remote connections using MS Remote Desktop Services (RDS); however, since the machine issues its own self-signed security certificate I get a warning every time I connect to this computer.
 So my questions are:
So my questions are:
- Would it be more secure if I install a SSL certificate from a trusted CA such as GoDaddy, VeriSign, DigiCert, etc rather than simply continuing using a self-signed certificate?
Related to the previous question, reading http://www.alkia.net/index.php/faqs/106-how-to-secure-remote-desktop-connections-using-tls-ssl-based-authentication (specific to Windows Server 2003 including SP1), it says that the certificate should be computer based. So, I imagine when creating the Certificate Signing Request (CSR) the Common Name (CN) would the hostname/computer name rather than a domain name.
- Once I obtain the certificate, how would I install it on the Remote Desktop Protocol (RDP) server so that it is used to secure the remote connections?
This computer is a member of a workgroup.
1Cert from trusted CA won't be more secure. The same security will be achieved by installing the self-signed server certificate on your client machine, so that the cert will be known and it will be able to notify you if someone would try to present you a different cert during an attack. – Marki555 – 2015-05-19T08:07:08.090
1Would it be more secure? no. A trusted CA is essentially used so that you the user (not you the machine) can be confident that the machine you're connecting to is the one you actually mean to be connecting to. You could just as easily create your own self-signed cert with custom information, or just use the default – Russell Uhl – 2015-05-19T15:47:36.280