I to got this chicken virus, when i exposed default ports inorder to connect to remote access from my home machine.
in my case this site helped me out
Steps
1) List the files under hourly cron. If you can see any .sh file, please open it.
root@vps-# ls -la /etc/cron.hourly/
++++++++++
CT-24007-bash-4.1# ls /etc/cron.hourly/
freshclam gcc.sh
CT-24007-bash-4.1#
++++++++++
2) If the .sh file is showing similar data as shown below, then it's a Virus program!!
root@vps-# cat /etc/cron.hourly/gcc.sh
++++++++++
cat /etc/cron.hourly/gcc.sh
#! / Bin / sh
PATH = / bin: / sbin: / usr / bin: / usr / sbin: / usr / local / bin: / usr / local / sbin: / usr / X11R6 / bin
for i in `cat / proc / net / dev | grep: | awk -F: {'print $ 1'}`; do ifconfig $ i up & done
cp /lib/libudev.so /lib/libudev.so.6
/lib/libudev.so.6
++++++++++
3) Now, please don't be hurry! Stay calm and easy :D
Do not delete gcc.sh or do not remove the crontab. If you do delete or remove it, then another process will generate immediately.
You can either remove the culprit script or disable it. [ I prefer to disable it to show the proof to the customer ]
root@vps-# rm -f /etc/cron.hourly/gcc.sh;
OR
root@vps- # chmod 0 /etc/cron.hourly/gcc.sh; chattr +ia /etc/cron.hourly/gcc.sh; chattr + i /etc/crontab
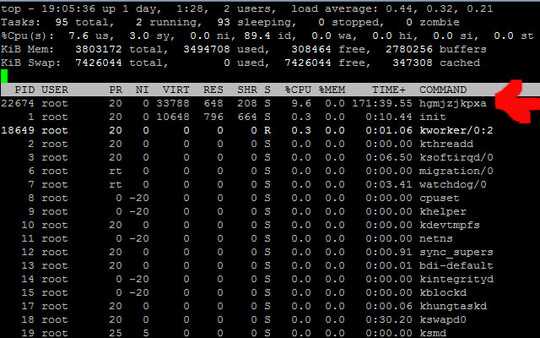
4) Use top command to view virus or malicious file ( Eg :"mtyxkeaofa" ) PID is 16621, do not directly kill the program, otherwise it will again produce, but to stop its operation use the below command.
root@vps- # kill -STOP 16621
Delete files within /etc/init.d. or disable it [ I prefer to disable it to show the proof to the customer ]
root@vps-# find /etc -name '* mtyxkeaofa *' | xargs rm -f
OR
chmod 0 /usr/bin/mtyxkeaofa;
chmod 0 /etc/init.d/mtyxkeaofa;
chattr +ia /usr/bin/mtyxkeaofa;
chattr +ia /etc/init.d/mtyxkeaofa;
6) Delete /usr/bin inside archives.
root@vps-# rm -f /usr/bin/mtyxkeaofa;
7) Check /usr/bin archives recent changes, the virus can also be deleted if the other suspect is the same directory.
root@vps-# ls -lt /usr/bin | head
8) Now kill the malicious program, it will not produce.
root@vps-# pkill mtyxkeaofa
9) Remove the virus body.
root@vps-# rm -f /lib/libudev.so
This trojan is also know as Chinese Chicken Multiplatform DoS botnets Trojan, Unix - Trojan.DDoS_XOR-1, Embedded rootkit,
Note: If you are unable to find .sh file, you may please install ClamAV, RKHunter and check logs/report to find the suspicious/malicious
link to the actual site
https://admin-ahead.com/forum/server-security-hardening/unix-trojan-ddos_xor-1-chinese-chicken-multiplatform-dos-botnets-trojan/
5Probably some botnet client (your machine is compromised). You have to find out how it is started. Utilities like
cruftmay come in handy to see what files do not belong to packages. – Dan – 2015-02-14T13:40:47.7732
ps lwill show you what the parent process is. Most likely, that'll tell you what is spawning this process. Look at the PPID column for the information you want. I wouldn't be so quick to declare this malware. – krowe – 2015-02-14T14:02:54.040+1 to check the parent process. And if the file
/use/bin/hgmjzjkpxaexists (could it be in /usr?) is it also a link, or something else interesting listed inls -la, or viewed withlessorstrings? – Xen2050 – 2015-02-15T04:02:07.920there is no any parent process, it is looking like whoami process, there is one thing when i check "netstat -natp" there is an establisment foreign address is 98.126.251.114:2828. when i try to add rules to iptables, it is not working. But after trying and then restart this address change to 66.102.253.30:2828 this one. do you have any idea about this? – user1424059 – 2015-02-17T12:23:19.020