10
2
Is windows built-in Remote Desktop secure? I mean, does it use any encryption methods? or someone can hijack the data that have been transferred between two system?
10
2
Is windows built-in Remote Desktop secure? I mean, does it use any encryption methods? or someone can hijack the data that have been transferred between two system?
13
There are two aspects of the security you should be aware of, how it creates the connection and how the connection is secured. There are two different modes for securing the creation of the connection for remote desktop, Legacy mode (I don't think it has a name) and Network Level Authentication (NLA). When you allow remote desktop you can choose if you only want to allow NLA connections or allow connections from the older legacy mode too.
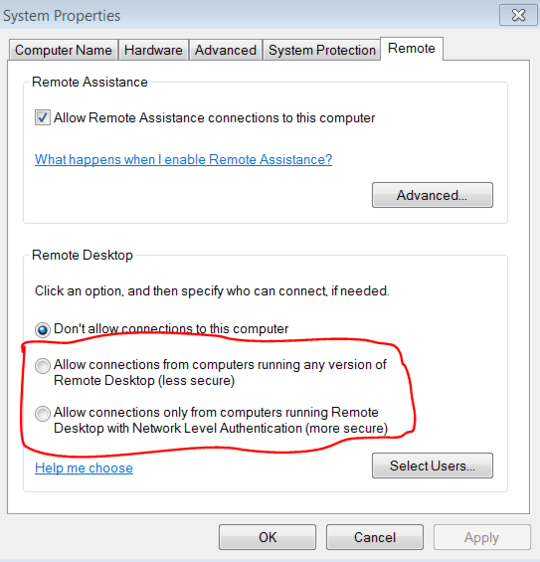
NLA mode is much more secure and has less possibilities for people to capture data from or intercept the connection while it is being established.
For the connection itself there are many fine tuning settings that are all set server side. The Help file summarizes much better than I can so I will just quote that.
Configure Server Authentication and Encryption Levels
By default, Remote Desktop Services sessions are configured to negotiate the encryption level from the client to the RD Session Host server. You can enhance the security of Remote Desktop Services sessions by requiring the use of Transport Layer Security (TLS) 1.0. TLS 1.0 verifies the identity of the RD Session Host server and encrypts all communication between the RD Session Host server and the client computer. The RD Session Host server and the client computer must be correctly configured for TLS to provide enhanced security.
NoteFor more information about RD Session Host, see the Remote Desktop Services page on the Windows Server 2008 R2 TechCenter (http://go.microsoft.com/fwlink/?LinkId=140438).
Three security layers are available.
- SSL (TLS 1.0) - SSL (TLS 1.0) will be used for server authentication and for encrypting all data transferred between the server and the client.
- Negotiate - This is the default setting. The most secure layer that is supported by the client will be used. If supported, SSL (TLS 1.0) will be used. If the client does not support SSL (TLS 1.0), the RDP Security Layer will be used.
- RDP Security Layer - Communication between the server and the client will use native RDP encryption. If you select RDP Security Layer, you cannot use Network Level Authentication.
The most secure layer that is supported by the client will be used. If supported, SSL (TLS 1.0) will be used. If the client does not support SSL (TLS 1.0), the RDP Security Layer will be used.
RDP Security Layer
Communication between the server and the client will use native RDP encryption. If you select RDP Security Layer, you cannot use Network Level Authentication.
A certificate, used to verify the identity of the RD Session Host server and encrypt communication between the RD Session Host and the client, is required to use the TLS 1.0 security layer. You can select a certificate that you have installed on the RD Session Host server, or you can use a self-signed certificate.
By default, Remote Desktop Services connections are encrypted at the highest level of security available. However, some older versions of the Remote Desktop Connection client do not support this high level of encryption. If your network contains such legacy clients, you can set the encryption level of the connection to send and receive data at the highest encryption level supported by the client.
Four encryption levels are available.
- FIPS Compliant - This level encrypts and decrypts data sent from the client to the server and from the server to the client by using Federal Information Process Standard (FIPS) 140-1 validated encryption methods. Clients that do not support this level of encryption cannot connect.
- High - This level encrypts data sent from the client to the server and from the server to the client by using 128-bit encryption. Use this level when the RD Session Host server is running in an environment containing 128-bit clients only (such as Remote Desktop Connection clients). Clients that do not support this level of encryption will not be able to connect.
- Client Compatible - This is the default setting. This level encrypts data sent between the client and the server at the maximum key strength supported by the client. Use this level when the RD Session Host server is running in an environment containing mixed or legacy clients.
- Low - This level encrypts data sent from the client to the server by using 56-bit encryption. Data sent from the server to the client is not encrypted.
4Security is almost always described in terms of probabilities not absolutes. It is not secure against your roommate, it is secure against my dog. First you should characterize things like the cost to you of failure as well as the value to an attacker of compromising. – Ram – 2014-03-26T03:11:34.663