25
12
Title continuation would be “while having limited knowledge of Internet security”.
I have recently set up a small server with a low end computer running debian with the aim to use it as a personal git repository. I have enabled ssh and was quite surprised at the promptness at which it suffered from brute force attacks and the like. Then I read that this is quite common and learned about basic security measures to ward off these attacks (lots of questions and duplicates on serverfault deal with it, see for instance this one or this one).
But now I am wondering if all this is worth the effort. I decided to set up my own server mostly for fun : I could just rely on third party solutions such as those offered by gitbucket.org, bettercodes.org, etc. While part of the fun is about learning about Internet security, I have not enough time to dedicate to it to become an expert and be almost certain that I took the correct prevention measures.
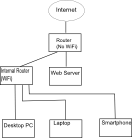
In order to decide if I will continue to play with this toy project, I would like to know what I really risk in doing so. For instance, in what extent are the other computers connected to my network threaten as well? Some of these computer are used by people with even lesser knowledge than mine running Windows.
What is the probability that I get into real trouble if I follow basic guidelines such as strong password, disabled root access for ssh, non standard port for ssh and possibly disabling password login and using one of fail2ban, denyhosts or iptables rules?
Put another way, is there some big bad wolves I should fear or is it all mostly about shooing away script kiddies?
I think you hit the nail on the head when you mentioned that you don't have the time or inclination to become an expert in $TECHNOLOGY security; this is the primary reason to use a hosted solution. The only other common argument in evaluating in-house vs hosting is the cost. Since github and the like are free, you're essentially giving up your personal time just to gain the knowledge of how to run a git repo. We can't tell you what you should be doing with your personal time, but in a professional situation this would make no sense. (caveat emptor: complicated situations have more variables). – Chris S – 2013-08-26T14:09:35.047
1If you decide to run your own server, also add to your todo list regular checking for updates and security vulnerabilities for every service you run. Just setting it up is not enough. – week – 2013-08-26T14:18:50.213
Two words: public keys, as @Stephane put it. Disable
keyboard-interactiveauthentication and use onlypubkeyauthentication. – kostix – 2013-08-26T16:20:23.647