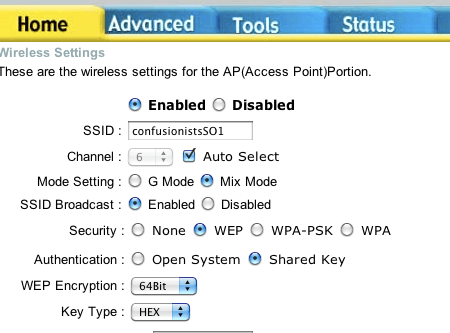
The screenshot looks like an older version of the D-Link config interface I use – you're missing WPA2, and the radio selection is a drop-down in my interface. What you should do is:
- Set SSID broadcast to disabled.
- Switch to WPA.
- Set up MAC filtering.
- Update your firmware (Tools > Firmware > follow the instructions).
- Switch to WPA2 if that option becomes available.
The end result is a network that does not advertise itself and requires both getting the security type and password correct and also that the connecting interface use an explicitly whitelisted MAC address.
To set up MAC filtering:
- Go to Advanced > Filters.
- Click on MAC filters.
- Select to only allow the listed MAC addresses.
- Populate the list with the MAC addresses of your machines using the drop-down and apply buttons.
The drop-down only lists the MAC addresses of interfaces that have connected in the past. When you later want to connect a new computer, or connect an old one via a new interface, you'll have to find a way to get the MAC address for the interface you want to use from the machine yourself; the router won't be able to help you out. Once you have it, you just type it in along with a name and add it to the list.
I get the MAC address using ifconfig en0 or ifconfig en1 (as appropriate) on my Mac; you can likely use ipconfig under Windows, but the MAC address is undoubtedly exposed in some graphical UI somewhere on every consumer system you'll want to connect to the router.
MAC spoofing is still a possibility, but if someone is that determined to get on your network, you'll either need to create a much more clever setup or just switch to using a cabled network.
6
(Someone voted to move this to Server Fault, but I disagree. From its FAQ: Server Fault is for system administrators and IT professionals, people who manage or maintain computers in a professional capacity. If you are in charge of servers/networks/many desktop PCs (other than your own) then you're in the right place to ask your question! Well, as long as the question is about your servers, your networks, or desktops you support, anyway.)
– Arjan – 2010-12-21T12:36:13.0503Delete his files. He'll disconnect or disclose his identity eventually. – Daniel Beck – 2010-12-21T12:41:03.870
3Hmmm, instead of deleting, copying files and altering a bit might do the trick too? One might even find some photos to see which neighbour it is? (Now wondering if it's illegal in some countries to browse an unknown hard disk when someone connects to your computer.) Also, after having cracked WEP, it's a bit odd —or stupid— to have an AFP share open, so the things one finds might have been put there on purpose too? – Arjan – 2010-12-21T13:14:35.327
1@Arjan He even cracked the network to be able to share his data. Of course he wants others to access his data :-) – Daniel Beck – 2010-12-21T16:33:17.933