4
1
I have scheduled task that should run every two hours, with the following command line action:
- Program:
mshta - Arguments:
vbscript:Execute("CreateObject(""Wscript.Shell"").Run ""powershell -NoLogo -Command """"& 'X:\Path\To\Custom\powershellScript.ps1'"""""", 0 : window.close")
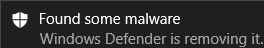
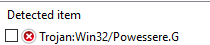
Every two hours, instead of the task getting run, i'm getting:
and in Defender history:
I don't want to stop Windows Defender, because of potential security implications of doing so. Is there a way to add exclusion in Defender to ignore the task?.
I tried adding both script path, folder, mshta.exe and powershell.exe to exclusions, also ps1 to file types. Nothing works.
By the way, Defender doesn't remove the task, or the script that should be run, just stops it from running.
Clarification:
It must be run in background, no window should pop out when the task is run, it has to be run with the user if he's logged in, i don't want to store password/run with other user account or highest privileges.
The script has to be executed as the logged in user. The purpose of it is to change the wallpaper for the logged in user to downloaded one (
$picturePathvariable). Excerpt:
$registryPropertyPath = "HKCU:\Control Panel\Desktop\"
$registryPropertyName = "Wallpaper"
$wallpaperProperty = (Get-ItemProperty -Path $registryPropertyPath -Name $registryPropertyName).WallPaper
if ($wallpaperProperty -ne $picturePath) {
Set-ItemProperty -Path $registryPropertyPath -Name $registryPropertyName -Value $picturePath
for ($i = 0; $i -lt 20; $i++) {
RUNDLL32.EXE USER32.DLL,UpdatePerUserSystemParameters 1, True
}
}
#1 Ignoring the script host and powershell is a really terrible idea. These are very common threat vectors that need to be scanned. – HackSlash – 2018-06-25T16:40:11.507
1#2 Why are you using Wscript to call powershell? Why not just run your script from Task Sched? That should fix the detection problem. – HackSlash – 2018-06-25T16:40:59.240
@HackSlash because running it normally causes window to pop out every two hours. This is a desktop machine, I don't want it, it should be run completely in background. – Hex – 2018-06-25T18:04:24.857
The script has to be run as logged-in user (Run only when user is logged on). – Hex – 2018-06-26T07:18:46.817
1..so your task runs a HTA which runs a VBScript which runs PowerShell which runs rundll32 to call a function not even meant to be called from rundll32? Don't be surprised if other programs find it suspicious. – user1686 – 2018-06-26T07:29:35.380
1But for a start, have you tried 1) running VBScript via
wscriptrather than MSHTA? 2) avoiding the PowerShell layer and doing everything via VBScript? It can read and write registry, too. – user1686 – 2018-06-26T07:30:31.577