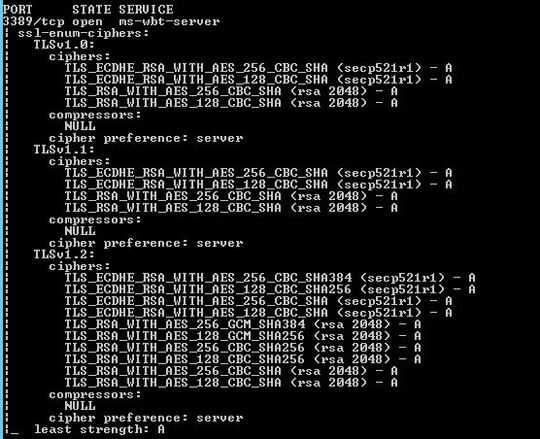
I have disabled 3DES in registry. Port 3389 is successfully disable 3DES (TLS_RSA_WITH_3DES_EDE_CBC_SHA).
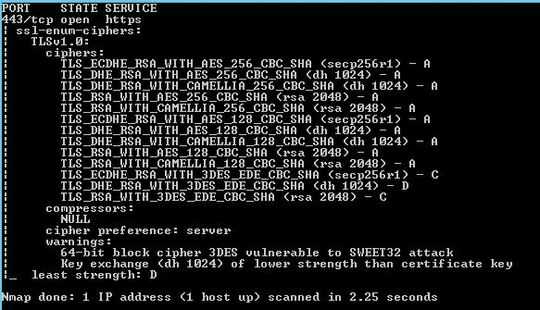
However, 3DES ciphers are still occur in port 443. What should be done to remove 3DES ciphers in port 443?
Thank you.
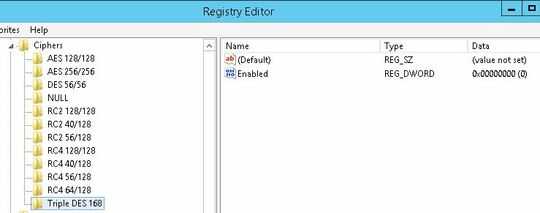
Disable 3DES:
3DES ciphers in port 443:
No 3DES ciphers in port 3389:
Interesting situation. Not sure this affects RDP, (it should, since it's all "schannel" in the background anyway I guess) but please try anyway: Have you tried disabling 3DES via IISCrypto and rebooted?
– StackzOfZtuff – 2018-03-07T13:58:13.910@StackzOfZtuff Yes, I have tried to disable 3DES by IISCrypto and rebooted, but still occur these three 3DES ciphers in port 443. Do you have any ideas? – Edmund Lo – 2018-03-08T02:18:20.453
Are you running something other than IIS on 443? – StackzOfZtuff – 2018-03-08T05:36:18.747
@StackzOfZtuff Yes, apache server is using port 443 for client to access into jedox web (a web interface of BI system). – Edmund Lo – 2018-03-08T07:23:11.747
@StackzOfZtuff Thanks for your reminder! I should mark '!3DES' on the SSLCipherSuite line in ssl.conf file. – Edmund Lo – 2018-03-08T08:47:09.093
Yes. There's also a nice generator that (among other settings) generates an old/intermediate/modern "SSLCipherSuite" line -> https://mozilla.github.io/server-side-tls/ssl-config-generator/
– StackzOfZtuff – 2018-03-08T10:38:06.127