0
I work in an environment that uses 802.1x WiFi network that uses client certificates. I am looking for a creative solution that makes this WiFi network accessible to devices that can understand WPA2 Personal style only.
This is how it works now.
- Users first connect to "Lenovo Guest" network. This is WPA2 Personal style network.
- When you try to access google.com, the web browser gets redirected to a page that prompts user to download and run an application. I believe it is Cisco or Aruba clearpass installer or something of that sort. After running this application, the local certificate store on my PC is getting updated with certs injected by this utility.
- Then I see "Lenovo BYOD" wifi network when I scan for
WiFi. I make my PC forget "Lenova Guest" and then connect to "Lenova
BYOD" network without any authentication. It connects fine and I
have access to internet.
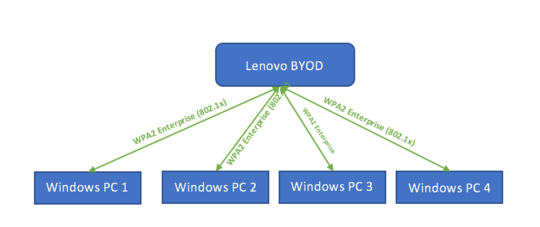 The above picture denotes current setup.
The above picture denotes current setup.
What I am trying to do is use a router that understands 802.1x; provision it with same certificate so that it connects to "Lenova BYOD" as a client and bridge its WiFi clients through NAT'ed. Picture below describes what I am looking for. I want to setup "My Lab WiFi" that bridges 802.1x wifi to WPA2 Personal style wifi.
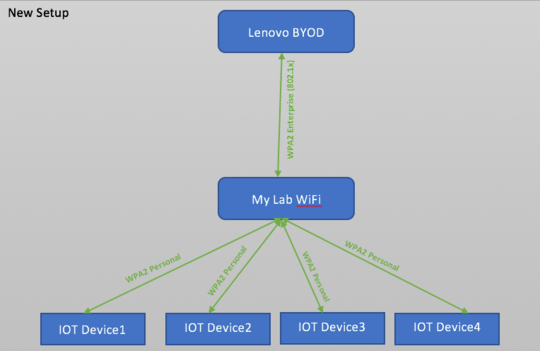
If there is a device that I can buy for $50 r less and configure it, that would be perfect. I looked at OpenWRT forums. Looks like it is possible if I burn OpenWRT firmware on a supported router. Before I go that route, I thought I ask if this one was tried and any solutions exist.
If you have suggestions to try OpenWRT configs, please share as well.
Do you have network administrator approval for this? If so, wouldn't they give you a certificate without having to wrangle with the installer, at least? – user1686 – 2017-12-27T21:11:45.287
The certificate is generated automatically based on user id and password on IT web site that the browser gets redirected to. Our IT is fine as long as the client authenticates with the certificate plus they understand the use case why we are trying to do it. – videoguy – 2017-12-27T23:46:52.847