1
0
A work desktop has Windows 7 Enterprise operating system and Microsoft Outlook 2010 e-mail client. The employer uses Microsoft Exchange for the e-mail server.
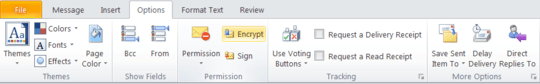
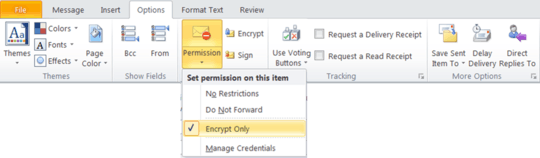
Desktop keyboards feature a slot for inserting a PIV card. An employee inserts his PIV card to log-on, and once logged on, he opens Microsoft Outlook 2010. He composes an e-mail containing information that requires encryption. In order to encrypt, he has two available methods, indicated by the two following images:
Method 1:
Method 2:
What are the differences between the two types of encryption methods offered in the aforementioned images?