8
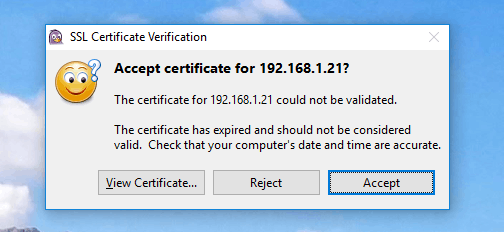
My work uses a local XMPP server (Wildfire, now called Openfire). When using the Pidgin client, it always asks me if it should accept the invalid (expired) certificate.
I would like to get Pidgin to always accept it without asking me. How can I do this without installing a new certificate on the XMPP server?
I attempted to import the certificate into both my Personal store and the Trusted Root store, but I still get the same prompt. The certificate is also stored in %APPDATA%\.purple\certificates\x509\tls_peers, but I still get the prompt.
Here's the debug log upon connecting:
Pidgin Debug Log : 10/4/2016 12:05:16 PM
(12:05:05) account: Connecting to account example@192.168.1.21/.
(12:05:05) connection: Connecting. gc = 04528D78
(12:05:05) dnssrv: querying SRV record for 192.168.1.21: _xmpp-client._tcp.192.168.1.21
(12:05:05) dnssrv: Couldn't look up SRV record. The filename, directory name, or volume label syntax is incorrect. (123).
(12:05:05) dnsquery: Performing DNS lookup for 192.168.1.21
(12:05:05) dnsquery: IP resolved for 192.168.1.21
(12:05:05) proxy: Attempting connection to 192.168.1.21
(12:05:05) proxy: Connecting to 192.168.1.21:5222 with no proxy
(12:05:05) proxy: Connection in progress
(12:05:05) proxy: Connecting to 192.168.1.21:5222.
(12:05:05) proxy: Connected to 192.168.1.21:5222.
(12:05:05) jabber: Sending (example@192.168.1.21): <?xml version='1.0' ?>
(12:05:05) jabber: Sending (example@192.168.1.21): <stream:stream to='192.168.1.21' xmlns='jabber:client' xmlns:stream='http://etherx.jabber.org/streams' version='1.0'>
(12:05:05) jabber: Recv (579): <?xml version='1.0' encoding='UTF-8'?><stream:stream xmlns:stream="http://etherx.jabber.org/streams" xmlns="jabber:client" from="192.168.1.21" id="da08260e" xml:lang="en" version="1.0"><stream:features><starttls xmlns="urn:ietf:params:xml:ns:xmpp-tls"></starttls><mechanisms xmlns="urn:ietf:params:xml:ns:xmpp-sasl"><mechanism>PLAIN</mechanism><mechanism>CRAM-MD5</mechanism><mechanism>DIGEST-MD5</mechanism><mechanism>ANONYMOUS</mechanism></mechanisms><auth xmlns="http://jabber.org/features/iq-auth"/><register xmlns="http://jabber.org/features/iq-register"/></stream:features>
(12:05:05) jabber: Sending (example@192.168.1.21): <starttls xmlns='urn:ietf:params:xml:ns:xmpp-tls'/>
(12:05:05) jabber: Recv (50): <proceed xmlns="urn:ietf:params:xml:ns:xmpp-tls"/>
(12:05:05) nss: SSL version 3.1 using 128-bit AES with 160-bit SHA1 MAC
Server Auth: 2048-bit RSA, Key Exchange: 1024-bit DHE, Compression: NULL
Cipher Suite Name: TLS_DHE_RSA_WITH_AES_128_CBC_SHA
(12:05:05) nss: subject=CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US issuer=CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US
(12:05:05) certificate/x509/tls_cached: Starting verify for 192.168.1.21
(12:05:05) certificate/x509/tls_cached: Certificate 192.168.1.21 expired at Mon Aug 29 09:54:35 2016
(12:05:05) certificate/x509/tls_cached: Checking for cached cert...
(12:05:05) certificate/x509/tls_cached: ...Found cached cert
(12:05:05) nss/x509: Loading certificate from C:\Users\example\AppData\Roaming\.purple\certificates\x509\tls_peers\192.168.1.21
(12:05:05) certificate/x509/tls_cached: Peer cert matched cached
(12:05:07) util: Writing file accounts.xml to directory C:\Users\example\AppData\Roaming\.purple
(12:05:07) util: Writing file C:\Users\example\AppData\Roaming\.purple\accounts.xml
(12:05:07) util: Writing file blist.xml to directory C:\Users\example\AppData\Roaming\.purple
(12:05:07) util: Writing file C:\Users\example\AppData\Roaming\.purple\blist.xml
(12:05:07) certificate/x509/tls_cached: User ACCEPTED cert
Caching first in chain for future use as 192.168.1.21...
(12:05:07) nss/x509: Exporting certificate to C:\Users\example\AppData\Roaming\.purple\certificates\x509\tls_peers\192.168.1.21
(12:05:07) util: Writing file C:\Users\example\AppData\Roaming\.purple\certificates\x509\tls_peers\192.168.1.21
(12:05:07) nss: Trusting CN=Unknown,OU=Unknown,O=REDACTED,L=REDACTED,ST=REDACTED,C=US
(12:05:07) certificate: Successfully verified certificate for 192.168.1.21
Have you tried viewing the certificate and installing it into the Windows certificate store? – Evan Darwin – 2016-09-28T20:26:05.090
Yes, but Pidgin throws the same error message. – Moses – 2016-09-28T20:31:24.603
2Open
Debug Window(Help -> Debug Window), connect to server and chooseAcceptin certificate dialog. There could be some certificate related messages in Debug window. You can attach the log to your original question. Accepted certificates should be stored in%APPDATA%\.purple\certificates\x509\tls_peers. Try to look there if there is file with the same name as your server has. – ge0rdi – 2016-10-01T16:56:52.767@ge0rdi Log is there now. Some info has been redacted for privacy. The cert is present in the
tls_peersfolder. – Moses – 2016-10-04T16:09:49.1371
I have bad news. I'm looking at Pidgin sources (your log helped a lot to orient in the code flow), but it seems that for expired (or not valid yet) certificates there is always prompt. All other certificate errors are not reported if certificate was already accepted. I'd suggest to report this issue to Pidgin developers here.
– ge0rdi – 2016-10-04T16:58:04.4331
In fact there are issues with expired certificates reported in Pidgin ticketing system. Usually the answer is that server's certificate has to be fixed.
– ge0rdi – 2016-10-04T17:19:29.643Have you tried connecting to the server without encryption? – Chris – 2016-10-06T13:57:53.953
@Chris How do I go about doing that? – Moses – 2016-10-06T15:43:16.767
@Moses, Sorry, I seemed to recall there was an option to connect without encryption. I just checked on my own installation of Pidgin and I can only select "Require encryption", "Use encryption if available" and "Use old-style SSL". None of those seem to be what you want. – Chris – 2016-10-07T07:29:18.020