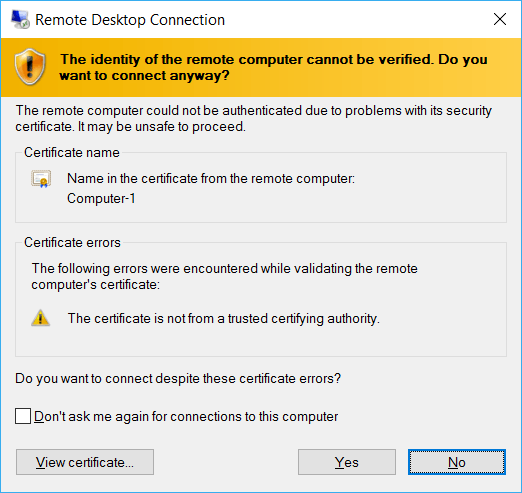
There are at least three solutions to this dialog box:
- Check the
Don't ask me again for connections to this computer
checkbox
- Install the certificate used by the remote machine into
your local machine
Trusted Root Certification Authorities store
- Use a certificate signed by someone both computers trust
The first option is what most people do and it is perfectly fine to do that. It doesn't install the certificate or trust it completely but it remembers to trust this certificate for a RDP connection only and only to the computer with the used host name.
It creates a new registry key at:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Terminal Server Client\Servers\Computer-1
with a Certhash value that has the thumbprint of the certificate.
If you delete this key, you get the dialog box again.
This exception is for your current user only, another user on the same machine has to do the same thing.
The second option is to actually trust the self-signed certificate. You have to start the Remote Desktop Connection as elevated administrator, then click the View certificate button, and on the next page the Install Certificate... button. Select Local Machine and Browse.... Use the Trusted Root Certification Authorities store and finish the import process.
Using this option any user on the computer can RDP into the remote machine without seeing the dialog, but you now added a new CA to your computer which is usually not the best idea and should be avoided. If someone hacks the remote computer, he could get hold of that certificate and use your trust in it for other purposes. The self-signed RDP certificate is for Server Authentication only, it can not be used to sign other certificates, but you never know.
When enabling RDP on the remote computer Windows creates this self-signed certificate automatically, but it is usually only valid for six months, so after six months you have to repeat either option one or two.
With option three you can get certificates that are valid longer but it requires you having your own CA or using a public one.
I would stick with option 1
Thanks yes I can confirm it's at that location in the registry. I have also previously tried installing the certificate the way you suggested and even though there were no errors it seemed to work even though it didn't. I wasn't running as admin so that probably explains that! If I wanted I guess I could create a self signed cert myself with a longer expire time for option 3? – Tom Jenkinson – 2016-08-14T17:07:34.637
Yes, I guess you could create your own and install it into both the remote computer and your local one. I always use my own CA, so I haven't done much with self-signed certs. – Peter Hahndorf – 2016-08-14T17:11:54.250
Once you have accepted option 1, isn't it basically impossible for someone to perform a MITM attack? – trognanders – 2017-05-19T06:37:50.363