0
I fear that I'm under a linux botnet takeover.
sudo netstat -antpv with all browsers closed, besides other results, returns this:
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
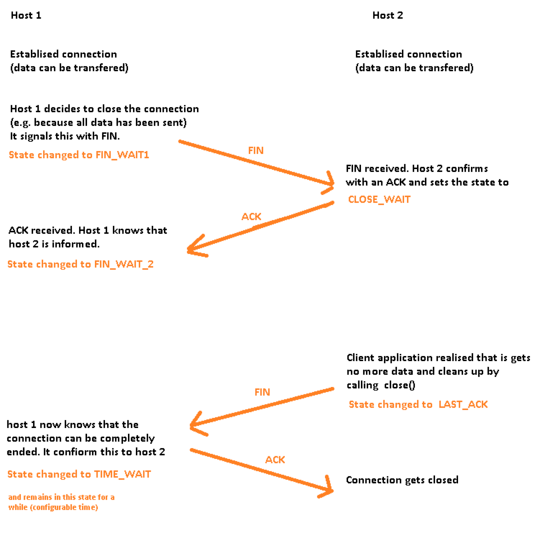
tcp 0 0 192.168.0.100:48090 216.58.197.67:443 TIME_WAIT -
tcp 0 0 192.168.0.100:49130 216.58.197.68:443 TIME_WAIT -
tcp 0 0 192.168.0.100:47830 74.125.200.190:443 TIME_WAIT -
tcp 0 0 192.168.0.100:33494 216.58.197.81:443 TIME_WAIT -
tcp 0 0 192.168.0.100:42121 216.58.220.42:443 TIME_WAIT -
tcp 0 0 192.168.0.100:33497 216.58.197.81:443 TIME_WAIT -
tcp 0 0 192.168.0.100:40590 198.41.215.68:443 TIME_WAIT -
These ip addresses keep changing. These addresses belong to
http://104.244.43.39.ipaddress.com (twitter)
http://54.192.159.56.ipaddress.com (cloudfront/amazon
http://216.58.197.67.ipaddress.com (google) (Same for the rest of the ips in this series)
http://74.125.200.190.ipaddress.com (google)
http://198.41.215.68.ipaddress.com (cloudflare)
So here are my questions:
1) Am I reading this right? Assuming so-
2) How do determine the processes that are doing this
3) How do I safeguard myself. Are there any good linux antivirus solutions
4) What's happening? I can understand twitter spamming, but what about google? Are they clicking on google links for SEO?
5) How do I get rid of them pronto?
I'm usually very careful about not using root. What you're saying all makes sense, thanks a lot. When I run as non-GUI, I don't have these.
I doubt I'll get a better answer but I'm going to wait before selecting this as the answer. – 0fnt – 2016-07-05T11:09:04.950
That is the way it should be done. Accepting to quick is not best. – Hennes – 2016-07-05T11:09:56.250