You can't prove that.
If you did tamper with the image, there are mistakes you could make that might make the tampering obvious. For example (at least on Windows 7), Snipping Tool doesn't write any extra metadata to the image file, and always saves as 32-bit RGBA image data (but maybe that's based on screen image depth). If your purported screenshot has a "Software" tag of "Paint.NET v3.36", then you've definitely tampered with it.
Likewise, tampering could introduce artefacts or inconsistencies in the image itself. For example, if WhatsApp uses a certain font in their user interface and you use a different font; or if you use a slightly different color than what they would actually use; or if they watermark the screen with a QR code of a digitally-signed tag encoding the current date and time, and you destroy or corrupt that watermark. However, a lot of that depends on knowing the details of the WhatsApp application... and once you know the details (so that you can reference them in a "proof"), you can generally in principle make sure that a tampered image conforms to them as well.
WhatsApp might provide a QR code or other barcode of a digital signature over the data you actually want to prove, either easily visible or as a hidden watermark somewhere (in which latter case it might be corrupted by a JPEG screenshot, but should be preserved in PNG). That data might be a recognizable thumbnail of an image, or the text of an associated chat session, or the identity of the person who sent the message. However, I doubt that WhatsApp actually does such a thing.


10
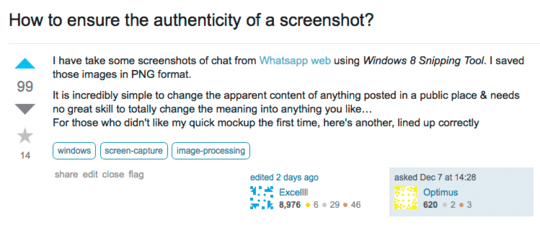
Despite this old post had asked on "How to ensure the authenticity of a picture?", the answers suggested to check the metadata. But metadata is useless for screenshot images. While this question has been underestimated, I wish to read good answers for this matter. Hence, +1.
– None – 2015-12-07T18:31:27.2308Your best bet is probably to ask whatsapp if they can provide who ever need the proof directly from their server... – DrakaSAN – 2015-12-07T20:07:27.233
29Even if you can prove that the screenshot accurately shows what was on the screen at the time, what's to say that the application displaying what you took a screenshot of is legitimate? I could easily make an application that displays an image, and take a screenshot of that. – a CVn – 2015-12-08T08:31:10.557
10Maybe I've missed it, but I'm surprised that metadata has been mentioned a couple times as being missing from a screenshot image, and therefore the metadata cannot be used to verify the image. Metadata in any image can't be used to verify an image - it's possible to modify the metadata too. – Steve – 2015-12-08T21:35:06.080
4Posting this as an answer isn't appropriate because it doesn't actually answer the question. But, I wanted to point out that the premise is false anyway. Even if there was a way to prove that the screenshots were legitimate, there is no way to prove that the application and its contents are legitimate. Further, there is no way to prove, solid screenshot or not, that the messages truly originated from the source that the screenshot claims. There's no proof that you didn't intercept the packets and modify the contents to say what you want, etc etc. The whole thing cannot be proven. – None – 2015-12-13T20:43:31.990
1Just a side point, you can have whatapp email you a full archive of any conversation you have. This would probably be easier to authenticate. (an Email directly from their server) – WhyEnBe – 2015-12-14T17:54:22.983