10
4
I have strange problem on my HP laptop. This began to happen recently. Whenever I start my machine, Windows 7 Action Center displays the following warning:
You need to restart your computer for UAC to be turned off.
Actually, this does not happen if it happened once on a specific day. For example, when I start the machine in the morning, it shows up; but it never shows up in the subsequent restarts within that day. On the next day, the same thing happens again.
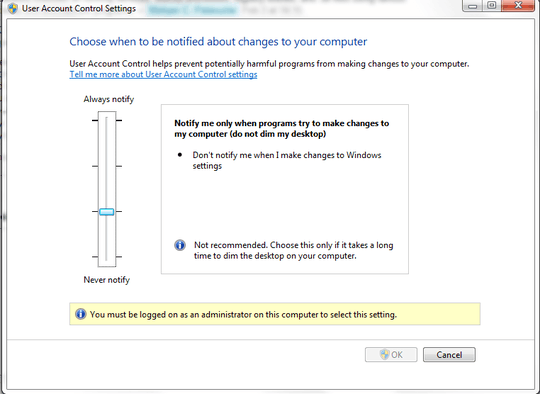
I never disable UAC, but obviously some rootkit or virus causes this. As soon as I get this warning, I head for the UAC settings, and re-enable UAC to dismiss this warning. This is a bothersome situation as I can't fix it.
First, I have run a full scan on the computer for any probable virus and malware/rootkit activity, but TrendMicro OfficeScan said that no viruses have been found. I went to an old Restore Point using Windows System Restore, but the problem was not solved.
What I have tried so far (which couldn't find the rootkit):
- TrendMicro OfficeScan Antivirus
- AVAST
- Malwarebytes' Anti-malware
- Ad-Aware
- Vipre Antivirus
- GMER
- TDSSKiller (Kaspersky Labs)
- HiJackThis
- RegRuns
- UnHackMe
- SuperAntiSpyware Portable
- Tizer Rootkit Razor (*)
- Sophos Anti-Rootkit
- SpyHunter 4
- ComboFix
There are no other strange activities on the machine. Everything works fine except this bizarre incident.
What could be the name of this annoying rootkit? How can I detect and remove it?
EDIT: Below is the log file generated by HijackThis:
Logfile of Trend Micro HijackThis v2.0.4
Scan saved at 13:07:04, on 17.01.2011
Platform: Windows 7 (WinNT 6.00.3504)
MSIE: Internet Explorer v8.00 (8.00.7600.16700)
Boot mode: Normal
Running processes:
C:\Windows\system32\taskhost.exe
C:\Windows\system32\Dwm.exe
C:\Windows\Explorer.EXE
C:\Program Files\CheckPoint\SecuRemote\bin\SR_GUI.Exe
C:\Windows\System32\igfxtray.exe
C:\Windows\System32\hkcmd.exe
C:\Windows\system32\igfxsrvc.exe
C:\Windows\System32\igfxpers.exe
C:\Program Files\Hewlett-Packard\HP Wireless Assistant\HPWAMain.exe
C:\Program Files\Synaptics\SynTP\SynTPEnh.exe
C:\Program Files\Hewlett-Packard\HP Quick Launch Buttons\QLBCTRL.exe
C:\Program Files\Analog Devices\Core\smax4pnp.exe
C:\Program Files\Hewlett-Packard\HP Quick Launch Buttons\VolCtrl.exe
C:\Program Files\LightningFAX\LFclient\lfsndmng.exe
C:\Program Files\Common Files\Java\Java Update\jusched.exe
C:\Program Files\Microsoft Office Communicator\communicator.exe
C:\Program Files\Iron Mountain\Connected BackupPC\Agent.exe
C:\Program Files\Trend Micro\OfficeScan Client\PccNTMon.exe
C:\Program Files\Microsoft LifeCam\LifeExp.exe
C:\Program Files\Hewlett-Packard\Shared\HpqToaster.exe
C:\Program Files\Windows Sidebar\sidebar.exe
C:\Program Files\mimio\mimio Studio\system\aps_tablet\atwtusb.exe
C:\Program Files\Microsoft Office\Office12\OUTLOOK.EXE
C:\Program Files\Babylon\Babylon-Pro\Babylon.exe
C:\Program Files\Mozilla Firefox\firefox.exe
C:\Users\userx\Desktop\HijackThis.exe
R1 - HKCU\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft.com/fwlink/?LinkId=54896
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page = about:blank
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft.com/fwlink/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft.com/fwlink/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft.com/fwlink/?LinkId=54896
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page = http://go.microsoft.com/fwlink/?LinkId=69157
R0 - HKLM\Software\Microsoft\Internet Explorer\Search,SearchAssistant =
R0 - HKLM\Software\Microsoft\Internet Explorer\Search,CustomizeSearch =
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,AutoConfigURL = http://www.yaysat.com.tr/proxy/proxy.pac
R0 - HKCU\Software\Microsoft\Internet Explorer\Toolbar,LinksFolderName =
O2 - BHO: AcroIEHelperStub - {18DF081C-E8AD-4283-A596-FA578C2EBDC3} - C:\Program Files\Common Files\Adobe\Acrobat\ActiveX\AcroIEHelperShim.dll
O2 - BHO: Babylon IE plugin - {9CFACCB6-2F3F-4177-94EA-0D2B72D384C1} - C:\Program Files\Babylon\Babylon-Pro\Utils\BabylonIEPI.dll
O2 - BHO: Java(tm) Plug-In 2 SSV Helper - {DBC80044-A445-435b-BC74-9C25C1C588A9} - C:\Program Files\Java\jre6\bin\jp2ssv.dll
O4 - HKLM\..\Run: [IgfxTray] C:\Windows\system32\igfxtray.exe
O4 - HKLM\..\Run: [HotKeysCmds] C:\Windows\system32\hkcmd.exe
O4 - HKLM\..\Run: [Persistence] C:\Windows\system32\igfxpers.exe
O4 - HKLM\..\Run: [hpWirelessAssistant] C:\Program Files\Hewlett-Packard\HP Wireless Assistant\HPWAMain.exe
O4 - HKLM\..\Run: [SynTPEnh] C:\Program Files\Synaptics\SynTP\SynTPEnh.exe
O4 - HKLM\..\Run: [QlbCtrl.exe] C:\Program Files\Hewlett-Packard\HP Quick Launch Buttons\QlbCtrl.exe /Start
O4 - HKLM\..\Run: [SoundMAXPnP] C:\Program Files\Analog Devices\Core\smax4pnp.exe
O4 - HKLM\..\Run: [Adobe Reader Speed Launcher] "C:\Program Files\Adobe\Reader 9.0\Reader\Reader_sl.exe"
O4 - HKLM\..\Run: [Adobe ARM] "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe"
O4 - HKLM\..\Run: [lfsndmng] C:\Program Files\LightningFAX\LFclient\LFSNDMNG.EXE
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Common Files\Java\Java Update\jusched.exe"
O4 - HKLM\..\Run: [Communicator] "C:\Program Files\Microsoft Office Communicator\communicator.exe" /fromrunkey
O4 - HKLM\..\Run: [AgentUiRunKey] "C:\Program Files\Iron Mountain\Connected BackupPC\Agent.exe" -ni -sss -e http://localhost:16386/
O4 - HKLM\..\Run: [OfficeScanNT Monitor] "C:\Program Files\Trend Micro\OfficeScan Client\pccntmon.exe" -HideWindow
O4 - HKLM\..\Run: [Babylon Client] C:\Program Files\Babylon\Babylon-Pro\Babylon.exe -AutoStart
O4 - HKLM\..\Run: [LifeCam] "C:\Program Files\Microsoft LifeCam\LifeExp.exe"
O4 - HKCU\..\Run: [Sidebar] C:\Program Files\Windows Sidebar\sidebar.exe /autoRun
O4 - Global Startup: mimio Studio.lnk = C:\Program Files\mimio\mimio Studio\mimiosys.exe
O8 - Extra context menu item: Microsoft Excel'e &Ver - res://C:\PROGRA~1\MICROS~1\Office12\EXCEL.EXE/3000
O8 - Extra context menu item: Translate this web page with Babylon - res://C:\Program Files\Babylon\Babylon-Pro\Utils\BabylonIEPI.dll/ActionTU.htm
O8 - Extra context menu item: Translate with Babylon - res://C:\Program Files\Babylon\Babylon-Pro\Utils\BabylonIEPI.dll/Action.htm
O9 - Extra button: Research - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~1\Office12\REFIEBAR.DLL
O9 - Extra button: Translate this web page with Babylon - {F72841F0-4EF1-4df5-BCE5-B3AC8ACF5478} - C:\Program Files\Babylon\Babylon-Pro\Utils\BabylonIEPI.dll
O9 - Extra 'Tools' menuitem: Translate this web page with Babylon - {F72841F0-4EF1-4df5-BCE5-B3AC8ACF5478} - C:\Program Files\Babylon\Babylon-Pro\Utils\BabylonIEPI.dll
O16 - DPF: {00134F72-5284-44F7-95A8-52A619F70751} (ObjWinNTCheck Class) - https://172.20.12.103:4343/officescan/console/html/ClientInstall/WinNTChk.cab
O16 - DPF: {08D75BC1-D2B5-11D1-88FC-0080C859833B} (OfficeScan Corp Edition Web-Deployment SetupCtrl Class) - https://172.20.12.103:4343/officescan/console/html/ClientInstall/setup.cab
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: Domain = yaysat.com
O17 - HKLM\Software\..\Telephony: DomainName = yaysat.com
O17 - HKLM\System\CS1\Services\Tcpip\Parameters: Domain = yaysat.com
O17 - HKLM\System\CS2\Services\Tcpip\Parameters: Domain = yaysat.com
O18 - Protocol: qcom - {B8DBD265-42C3-43E6-B439-E968C71984C6} - C:\Program Files\Common Files\Quest Shared\CodeXpert\qcom.dll
O22 - SharedTaskScheduler: FencesShellExt - {1984DD45-52CF-49cd-AB77-18F378FEA264} - C:\Program Files\Stardock\Fences\FencesMenu.dll
O23 - Service: Andrea ADI Filters Service (AEADIFilters) - Andrea Electronics Corporation - C:\Windows\system32\AEADISRV.EXE
O23 - Service: AgentService - Iron Mountain Incorporated - C:\Program Files\Iron Mountain\Connected BackupPC\AgentService.exe
O23 - Service: Agere Modem Call Progress Audio (AgereModemAudio) - LSI Corporation - C:\Program Files\LSI SoftModem\agrsmsvc.exe
O23 - Service: BMFMySQL - Unknown owner - C:\Program Files\Quest Software\Benchmark Factory for Databases\Repository\MySQL\bin\mysqld-max-nt.exe
O23 - Service: Com4QLBEx - Hewlett-Packard Development Company, L.P. - C:\Program Files\Hewlett-Packard\HP Quick Launch Buttons\Com4QLBEx.exe
O23 - Service: hpqwmiex - Hewlett-Packard Development Company, L.P. - C:\Program Files\Hewlett-Packard\Shared\hpqwmiex.exe
O23 - Service: OfficeScanNT RealTime Scan (ntrtscan) - Trend Micro Inc. - C:\Program Files\Trend Micro\OfficeScan Client\ntrtscan.exe
O23 - Service: SMS Task Sequence Agent (smstsmgr) - Unknown owner - C:\Windows\system32\CCM\TSManager.exe
O23 - Service: Check Point VPN-1 Securemote service (SR_Service) - Check Point Software Technologies - C:\Program Files\CheckPoint\SecuRemote\bin\SR_Service.exe
O23 - Service: Check Point VPN-1 Securemote watchdog (SR_Watchdog) - Check Point Software Technologies - C:\Program Files\CheckPoint\SecuRemote\bin\SR_Watchdog.exe
O23 - Service: Trend Micro Unauthorized Change Prevention Service (TMBMServer) - Trend Micro Inc. - C:\Program Files\Trend Micro\OfficeScan Client\..\BM\TMBMSRV.exe
O23 - Service: OfficeScan NT Listener (tmlisten) - Trend Micro Inc. - C:\Program Files\Trend Micro\OfficeScan Client\tmlisten.exe
O23 - Service: OfficeScan NT Proxy Service (TmProxy) - Trend Micro Inc. - C:\Program Files\Trend Micro\OfficeScan Client\TmProxy.exe
O23 - Service: VNC Server Version 4 (WinVNC4) - RealVNC Ltd. - C:\Program Files\RealVNC\VNC4\WinVNC4.exe
--
End of file - 8204 bytes
As suggested in this very similar question, I have run full scans (+boot time scans) with RegRun and UnHackMe, but they also did not find anything. I have carefully examined all entries in the Event Viewer, but there's nothing wrong.
Now I know that there is a hidden trojan (rootkit) on my machine which seems to disguise itself quite successfully. Note that I don't have the chance to remove the HDD, or reinstall the OS as this is a work machine subjected to certain IT policies on a company domain.
Despite all my attempts, the problem still remains. I strictly need a to-the-point method or a pukka rootkit remover to remove whatever it is. I don't want to monkey with the system settings, i.e. disabling auto runs one by one, messing the registry, etc.
EDIT 2: I have found an article which is closely related to my trouble:
Malware can turn off UAC in Windows 7; “By design” says Microsoft. Special thanks(!) to Microsoft.
In the article, a VBScript code is given to disable UAC automatically:
'// 1337H4x Written by _____________
'// (12 year old)
Set WshShell = WScript.CreateObject("WScript.Shell")
'// Toggle Start menu
WshShell.SendKeys("^{ESC}")
WScript.Sleep(500)
'// Search for UAC applet
WshShell.SendKeys("change uac")
WScript.Sleep(2000)
'// Open the applet (assuming second result)
WshShell.SendKeys("{DOWN}")
WshShell.SendKeys("{DOWN}")
WshShell.SendKeys("{ENTER}")
WScript.Sleep(2000)
'// Set UAC level to lowest (assuming out-of-box Default setting)
WshShell.SendKeys("{TAB}")
WshShell.SendKeys("{DOWN}")
WshShell.SendKeys("{DOWN}")
WshShell.SendKeys("{DOWN}")
'// Save our changes
WshShell.SendKeys("{TAB}")
WshShell.SendKeys("{ENTER}")
'// TODO: Add code to handle installation of rebound
'// process to continue exploitation, i.e. place something
'// evil in Startup folder
'// Reboot the system
'// WshShell.Run "shutdown /r /f"
Unfortunately, that doesn't tell me how I can get rid of this malicious code running on my system.
EDIT 3: Last night, I left the laptop open because of a running SQL task. When I came in the morning, I saw that UAC was turned off. So, I suspect that the problem is not related to startup. It is happening once a day for sure no matter if the machine is rebooted.
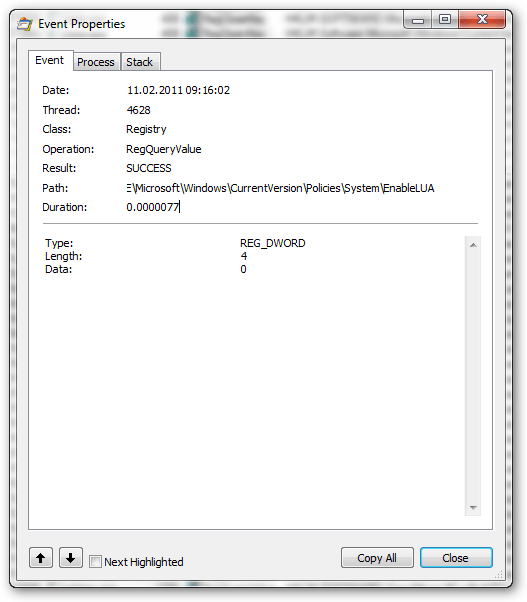
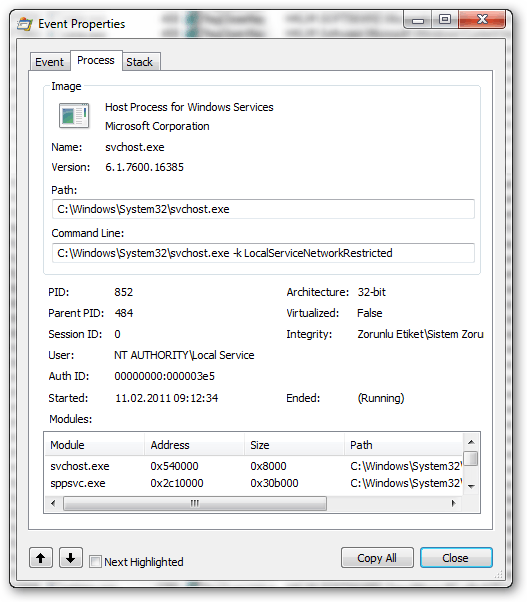
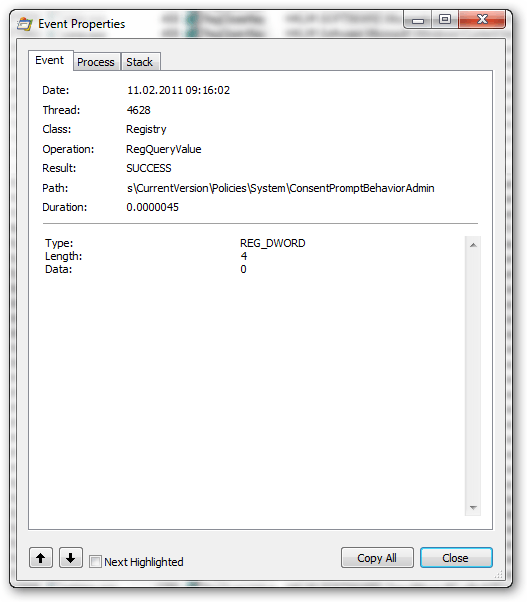
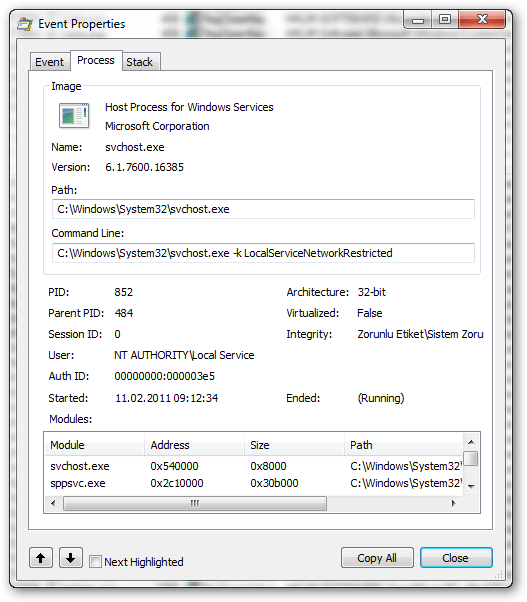
EDIT 4: Today, I immediately started "Process Monitor" as soon as Windows was started to hopefully catch the guilty one (thanks to @harrymc for the idea). At 9:17, UAC slider was slided to the bottom (Windows 7 Action Center gave the warning). I investigated all the registry actions between 9:16 and 9:18. I saved the Process Monitor log file (70MB containing only that 2 minutes interval). There are lots of EnableLUA = 0 (and the other) entries. I'm posting the screenshots of the properties windows of the first 4 below. It says svchost.exe is doing this, and gives some thread and PID numbers. I don't know what I should infer about them:
1As an extra thing to investigate, this could possibly be a setting that is being applied by the Group Policy from your domain controller. It may be that they (for some reason) have it set to reset UAC on a daily basis. Of course if they're enabling it using group policies and malware is disabling it, then that is bad. I'd have a chat with your IT guys, that is if they're the talkative kind. – Mokubai – 2011-01-21T13:34:24.743
@Mokubai: Thanks for your suggestion. I talked to the other colleagues in the company, and none of them is having such an issue. I'm sure our IT has not disabled UAC, as they are very sensitive on security issues. The interesting thing is, how did that (possible) rootkit befool the antivirus or other security measures put in place by IT? – Mehper C. Palavuzlar – 2011-01-21T14:33:27.663
As to how you may have gotten this possible infection in the first place, at it's simplest any malware protection you may have is generally reactive in nature, though proactive detection is possible it is not reliable. Someone dreams up a way to break into a system, then a company spots it and writes up a way to detect or remove it, action and reaction. If you do indeed have an infection it could very well be a completely new strain that hasn't been seen by the AV companies yet. As to how you got it there are too many security holes in places you wouldn't expect to give any idea... – Mokubai – 2011-01-21T17:07:05.940
HijackThis is clean. You might want to consider to get a filewall. Please try Autoruns and Process Monitor as described by Harry. – Tamara Wijsman – 2011-02-03T19:29:00.537
Have you tried looking in the Task Scheduler? (Start -> Control Panel -> Administrative Tools -> Task Scheduler) Click "Task Scheduler Library" to see Tasks set up by by things like the Google Updater. It is possible that your daily UAC reset is somewhere in there as tasks can be set up at a particular time and then be set to run X minutes after login if that time has already passed... I would have to say though, it could be a long and arduous task searching through the thousands of items in there. – Mokubai – 2011-02-06T19:21:16.240
@Mokubai: Yes. Please see my latest comments under harrymc's answer.
– Mehper C. Palavuzlar – 2011-02-06T21:33:29.197