110
16
Warning
The answers to this challenge test for a specific version of the patch that helps stop WannaCrypt/WannaCry attacks. Depending on your operating system, you may have a different patch. The best way to protect yourself is to make sure your PC is fully up to date and be careful when opening attachments and web links.
Introduction
I like to think programmers are inherently good people, even if some aren't so nice, so lets help people make sure they are protected with the MS17-010 patch.
Challenge
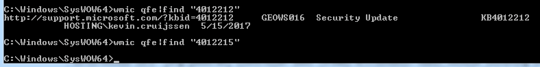
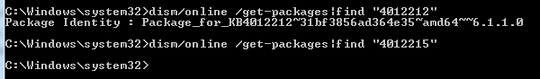
Your challenge is to write a full program or function that returns a truthy or falsey value depending on if the MS17-010 patch is installed on the current operating system.
Input and Output
Input: No input required
Output: A truthy or falsey value (Indicate which is used for each case). An error/exception can be considered a falsey value.
Rules
- Your code should run (and output correctly) on at least one windows operating system for which the patch is available, but doesn't have to run on every operating system (Please state any limitations).
- Standard loopholes apply
- This is code-golf, so the submission with the least amount of bytes wins!
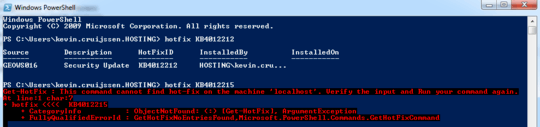
3Hmm, one question.. Regarding the truthy/falsey values, is an error allowed as falsey value, and truthy as an actual return, or isn't this allowed? – Kevin Cruijssen – 2017-05-16T09:14:08.183
@KevinCruijssen even if it was, your answer fails the "only one truthy value" ;-) – John Dvorak – 2017-05-16T09:18:10.723
I don't think it's listed in the "allowed IO methods" meta-question, but feel to add it there to see if it gains traction. – John Dvorak – 2017-05-16T09:19:22.330
3@KevinCruijssen I'm happy to consider an error as a falsely value. I think it's a clear indicator that the patch is not installed. – Notts90 supports Monica – 2017-05-16T09:20:17.277
Nice. My suggestion to list this in the general IO rules still applies, though. – John Dvorak – 2017-05-16T09:26:46.870
12If users missed this patch but installed a later one they will still be protected so this could give a false negative for some users. – Ian Miller – 2017-05-16T11:46:44.810
1I'd be interested in seeing some answers that actually test for the presence of the vulnerability rather than the presence of the patch. I'm not sure how easy it is to exploit/trigger and if it could be done in a short code snippet. – Micheal Johnson – 2017-05-16T20:52:57.170
2@MichealJohnson not sure it's wise to encourage people to post code demonstrating how to exploit the vulnerability. – Notts90 supports Monica – 2017-05-16T20:57:04.030
8Is the infection of the host pc a valid falsey value? It would obviously get the point across – Nic Robertson – 2017-05-16T22:13:15.623
1I thought this was going to be a question AboutJoining WordsTogether LikeThis. – Esolanging Fruit – 2017-05-17T02:38:54.560
Can we use the vulnerability to show the answer ? – Hybris95 – 2017-05-19T13:57:55.420
@Hybris95 No, the challenge is to test if the specific patch is installed, the vulnerability could have been fixed in a different patch. – Notts90 supports Monica – 2017-05-19T14:02:09.837
@IanMiller I'd not use some codegolf thingy to do serious stuff in real life... – Erik the Outgolfer – 2017-08-15T14:13:05.640